Archive for month: April, 2019
Lets get our Big Picture View in the weekend report, the weekly wrap up.
.
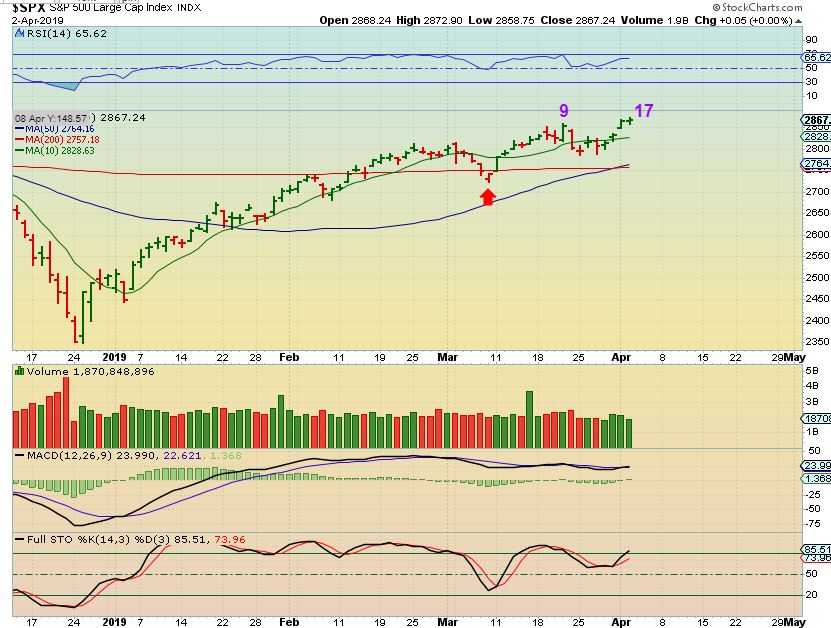
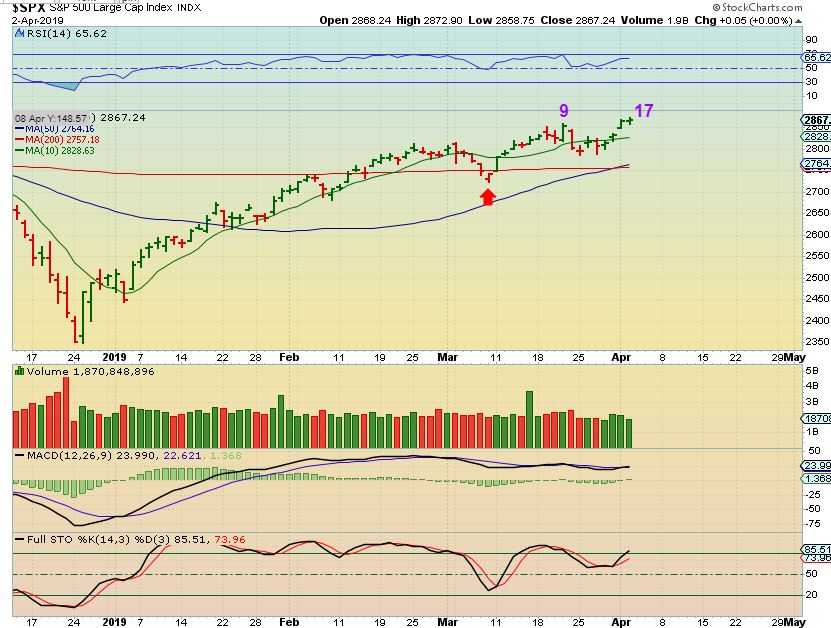
SPX WEEKLY - The SPX continues higher, and will likely meet the 2018 highs, whether that happens now or whether we get a pull back to a dcl first, and it happens on the next daily cycle. This current daily cycle seems to be a right translated Daily Cycle, so the next should pop to new highs again. So far, this remains set up bullishly in the big picture, even if we get a short term dip.
 Read More
Read MoreToday I want to review the market action, discuss the Precious Metals, and then discuss a few trades, including some of the ones that we have been riding in the Blockchain area, since Bitcoin and other cryptocurrencies were setting up Bullishly. Let's get right to the Thursday report...
Read MoreAfter a brief market review, allow me to explain why we might actually be at the 'Moment Of Truth' for the precious metals sector
.
SPX - The SPX is on day 22 and price inside of this short term bearish wedge is heading into the APEX. I would expect a drop into the dcl soon. The 200sma may act as support.
 Read More
Read MoreLast weeks markets were active, so let's take a look at what happened and see what that means to the Big Picture in various sectors.
Read MoreToday's report will focus strictly on what most were discussing Thursday -
"What is happening in The Precious Metals Market?" Is it party time? We have a lot to look at, and I have over 30 charts to examine on this subject alone, so let's get started...
.
Read MoreThe markets continue to run straight up. Well, maybe not straight up, but like the Theme picture shows, they have been working their way higher and some sectors are at new recent highs. I want to point out a few things on this run higher, so lets get right into it. We'll start with the Sox...
.
SOX - Take a look at the purple line and that represents a break out after the SOX briefly lost & regained the 200sma. From there it popped higher and chopped lower, back under the 10sma. Now it has popped to new recent highs again.

That shows that a bullish run is not always an easy one to ride. Now let's take a look at the SPX...
Read MoreNot much changed from yesterdays report, so let's start with a quick review...
.
SPX - Day 17 and we have a new peak. You could say that these markets are a bit choppy and sideways , but it does continue to climb higher with that action.
Read MoreWeakness followed by a break down in parts of the General Markets ( The TRAN & RUT) was reported here by me over a week ago. Over time, we gradually saw improvement, so that is what was also reported toward the end of last week and in the weekend report. These area would need to be monitored continually. Well, Monday we saw signs of healing, so we need to address that as a starting point.
.
RUT - On March 22, the Russell 2000 lost the 50 sma and broke below the prior low. This is a bad sign and needed to be monitored. As this was taking place, the Transports were showing signs of weakness too, so these areas were to be reported on daily.

TRAN - The Transports were also breaking down as noted on March 20

TRAN -A week later the Tran stayed below the 50sma, so this is a concern and caution was warranted.

TRAN - I did point out a bullish possibility, but until the 50sma is recovered, I would be staying away from the Transports, and I would remain cautious in the General Markets.
 Read More
Read More
Scroll to top
 Read More
Read More