Archive for month: April, 2019
APRIL 27th Weekend Wrap Up – Time To Rest Up
/in Premium /by Alex - Chart FreakThis weekend may be a bit more relaxing for those interested in the Precious Metals Sector, because as discussed in recent reports, some of the ideas presented here do still seem to be playing out. I will discuss how to take advantage of current set up, without losing too much sleep. 🙂
. Read MoreApril 25th – Staying In Focus
/in Premium /by Alex - Chart FreakToday I really want to Focus on the precious metals, so after a very brief review of a few other sectors, we'll get right to it...
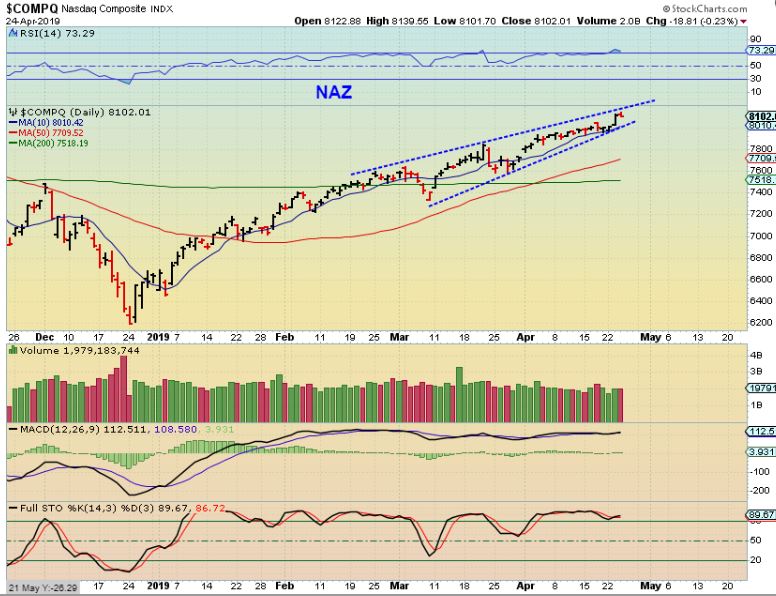
.NASDAQ - Nothing changed with the General Markets since yesterdays report.
 Read More
Read MoreWednesday April 23rd
/in Premium /by Alex - Chart FreakWhere are we in the various sectors of the Markets? ...
Read MoreTuesday April 23rd –
/in Premium /by Alex - Chart FreakEven though only 1 day passed since the weekend report, we do have a lot to cover, so let's get right into it...
Read MoreApril 20 Weekend Report
/in Premium /by Alex - Chart FreakTo the joy of many readers here, we are finally getting some of the sale prices on Miners that we have been expecting for a while now. Let's take a look at our weekend review and see how things stand after this 4 day trading week...
.SPX WEEKLY - We are coming due for a pull back cycle-wise. In the past, we have seen pull backs drop to the 50 week ma, as shown here.
1. It could happen at the next drop to a dcl, or
2. It may happen after a small drop to a dcl and then a break to news highs that rolls over, as shown here.
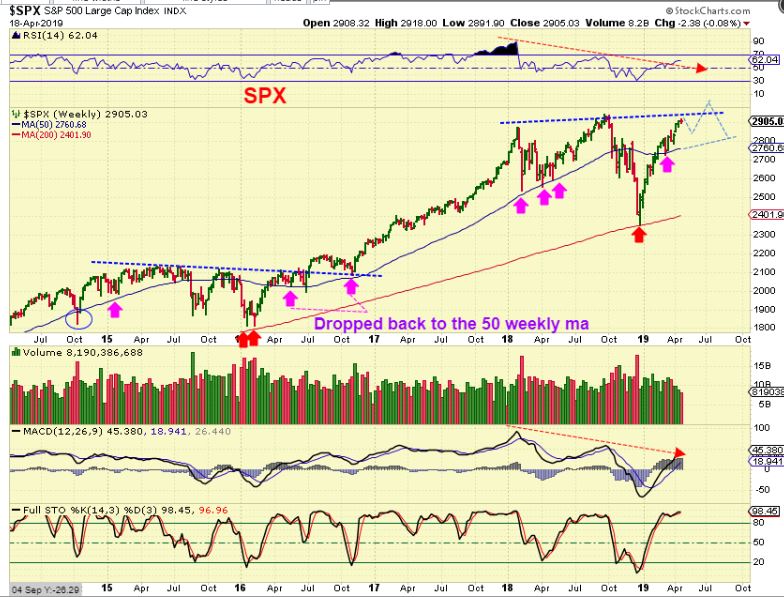
Let's discuss this a bit further...
Read MoreThursday April 17th
/in Premium /by Alex - Chart FreakFriday is a holiday and the markets are closed, so today is the last trading day of the week. Earlier this week I had mentioned cycle counts and a possible bearish rising wedge, so 'tighten stops and stay alert' was the thought for the General Markets at that time, but now? It may be time to consider 'Safety First'. Let me explain...
.XBI #1 - This was the XBI ( A Biotech ETF) Tuesday. It landed on the 50sma and also had the support of the 200sma below it.

XBI #2 - This was the XBI on Wednesday, the very next day. Look at that volume and how easily it sliced right through both moving averages. If that is some kind of warning of what might be coming in the rest of the markets, we better be listening.
 Read More
Read MoreWednesday April 17th Trading
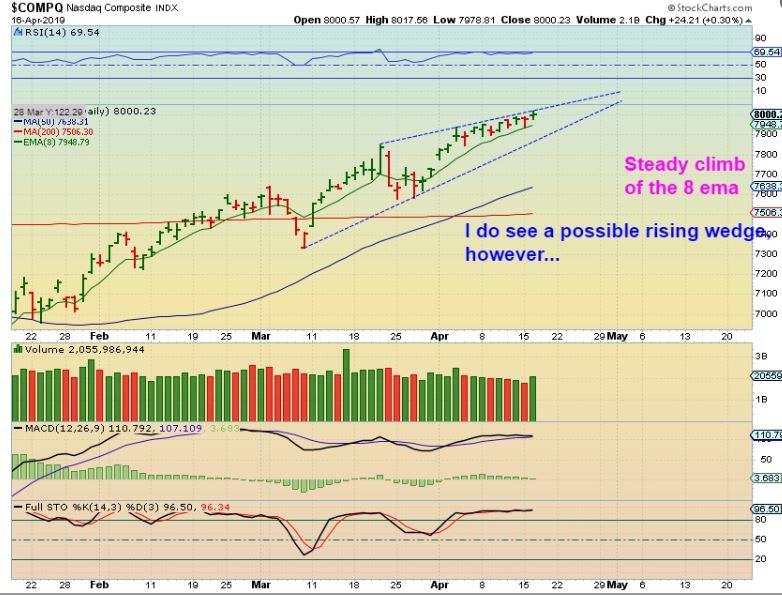
/in Premium /by Alex - Chart FreakNASDAQ #1 - The NASDAQ has been climbing along the top of that 8 ema ( or 10sma) Bullishly.
 Read More
Read MoreTuesday April 16th – Observations
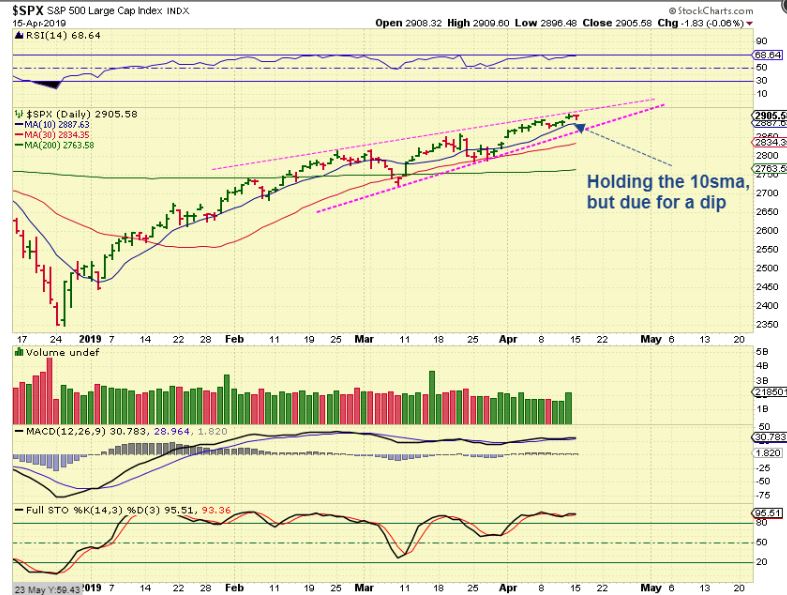
/in Premium /by Alex - Chart FreakThe General Markets should have a little more upside, and if you are willing to ride the dips and just hold current positions, you can use a reasonable stop. If you hate losing any of your gains, it might be wise to tighten stops and keep an eye on open positions. The markets have been running strong and pull backs have been fairly shallow, but it is looking like we could be due for another pull back soon. Let's review what we have...
.
SPX - The bearish rising wedge has been moving closer to the Apex. This is at least shorter term bearish. It doesn't call for a crash, but it does signal a possible pull back may be coming soon, and...
 Read More
Read MoreContact Us
26 Broadway,
8th Floor
New York, NY 10004
admin@bigleaguefinance.com
admin@bigleaguefinance.com
Latest Blog Posts
accelerator diet pills goji berry diet pills ultra 90 diet pills keto meal replacement bar top weight loss diet pills for thyroid patients where to buy t lite diet pills keto friendly thickener diet fuel diet pills peanuts keto friendly rite aid diet pills that work envy diet pills diet pills for breastfeeding moms belique diet pills perfect slim weight loss pills calories in a bottle of white wine