Archive for month: August, 2018
SPX - The SPX broke out above the upper trend line, but dropped back down on Thursday. We see a gap & the 10sma below, these could be initial targets, so let's see how things play out.
 Read More
Read More Let's discuss the current set up in various market sectors.
Read More1. Last Night I mentioned to my readers that I was seeing a drop in Gold coming. Gold was at $1212, and I posted this chart saying that we could see a drop to $1200. That is not a big deal, but we are waiting for a short cover rally, so apparently we had to 'expect delays'...

2. The drop started here, and I posted this in the comments section. Again, not a big scary concern, just Expect delays..

Let's talk about Gold $1200
Read MoreA Monday night report should be short, because we've only had one day since the weekend report, but Monday was a very active market. This report will be longer than the usual Monday report.
.
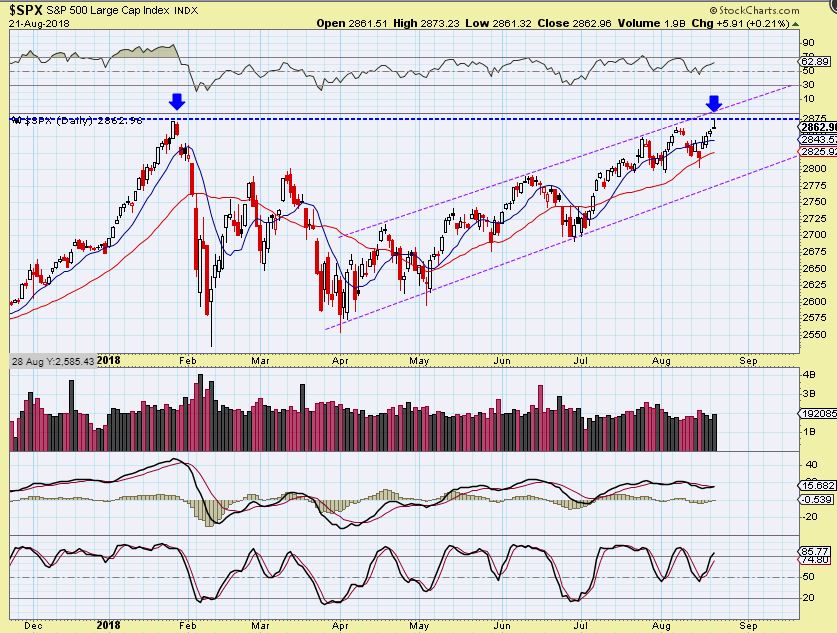
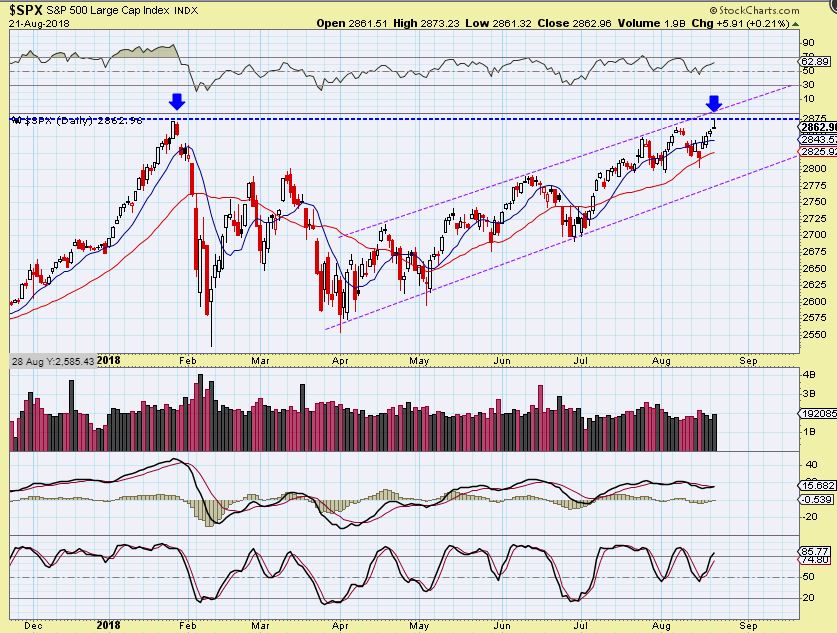
Review SPX August 21st - This was last week, and we saw the SPX meet up with 2 resistance points.
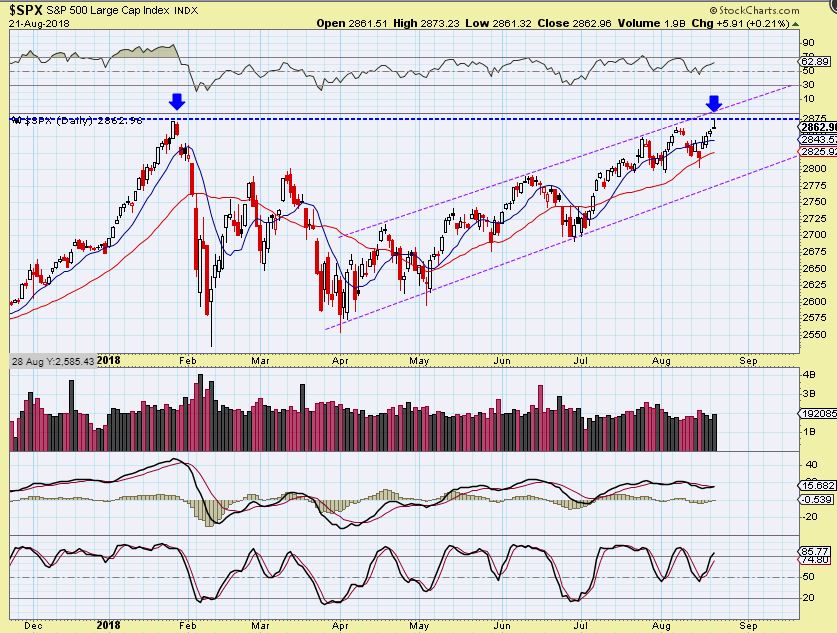
SPX WEEKLY Aug 24th - So for the weekend report, I drew that same resistance here. It could climb along the upper magenta line, but would need to break the blue line first...
 Read More
Read MoreFriday seemed like some sort of an anti-gravity day, with most sectors climbing nicely higher. We even had Swing Lows enter the dance floor, so let's take a look at our current market set ups...
RUSSELL 2000 - We looked at IWM and TNA earlier this week as buy signals, and we have follow through. Raise stops and see if they continue higher ...
 Read More
Read MoreWelcome to the last trading day of the week...
USD- This is a copy/ paste from yesterdays report, expecting a USD DCL.
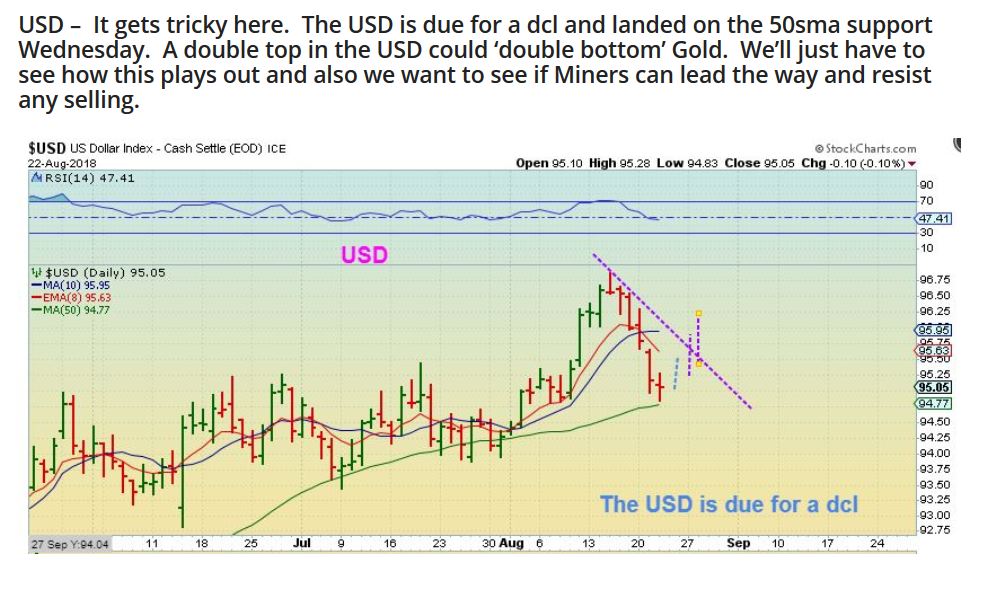
UUP ( USD) - It looks like the DCL may have formed. I mentioned yesterday

Now let's discuss Gold...
Read More.
I will have many trade ideas at the end of this report.
.
TNA - I mentioned that The Russell 2000 ( RUT, IWM, and you can use the TNA) Looked bullish, and this was the break out. It was and is a buy.
 Read More
Read MoreThe release of the FOMC Minutes from the last Fed Meeting is scheduled to be released today. At times, this can cause a reaction in the markets, if the verbiage or language that was used seems more Hawkish or Dovish than originally interpreted. For example, if they were to mention a concern pertaining to inflation rising faster than expected, that could affect certain sectors, so we just want to be mindful that the markets could move unexpectedly around 2 P.M. Eastern.
SPX #1 - Right where the SPX was about to break to new highs, it sold off a bit.
 Read More
Read MoreSometimes what seems to be impossible actually becomes possible, but a man rides in to town on Tuesday and leaves 2 days later on Tuesday? If that is possible, then I guess it is possible that Gold may have bottomed too. Oh, and by the way, his horse was named Tuesday. Let's review our markets...
Read MoreI hope that everyone can just enjoy some rest and relation this week, after last weeks market action. We also may want to rest up, because next week looks to be setting up to be interesting at this point...
.
General Markets were a bit Mixed, and remain that way
.
SPX - I've been expecting a drop into a dcl. The DJIA and NASDAQ looked to be dropping, and so did the SPX, but with a Wednesday reversal, it has moved higher. AT THIS POINT, I don't think that this is enough to be a dcl, but I shouldn't rule it out completely. Lets look at ...
 Read More
Read More
Scroll to top
 Read More
Read More Read More
Read More

 Read More
Read More Read More
Read More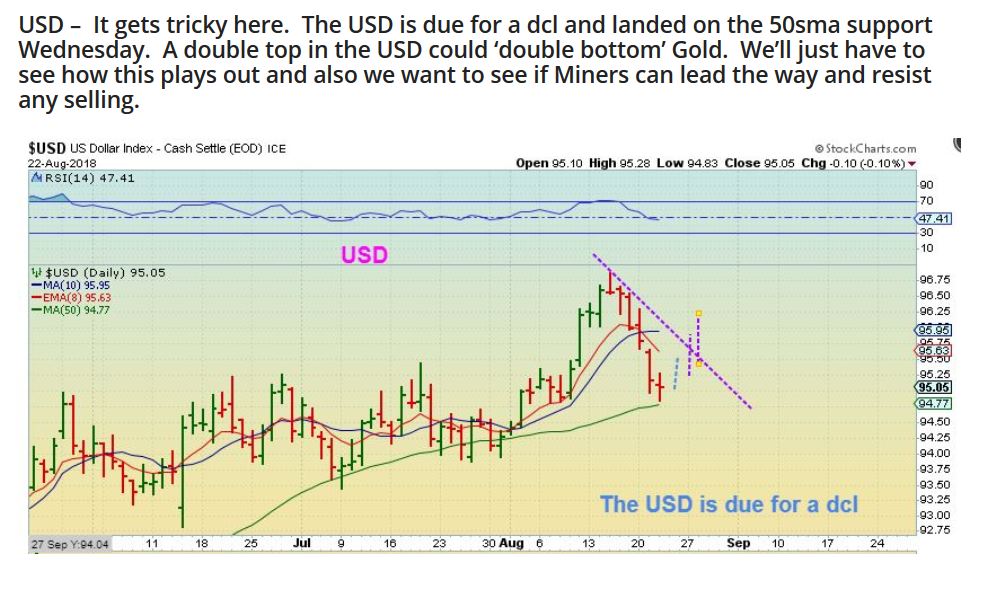

 Read More
Read More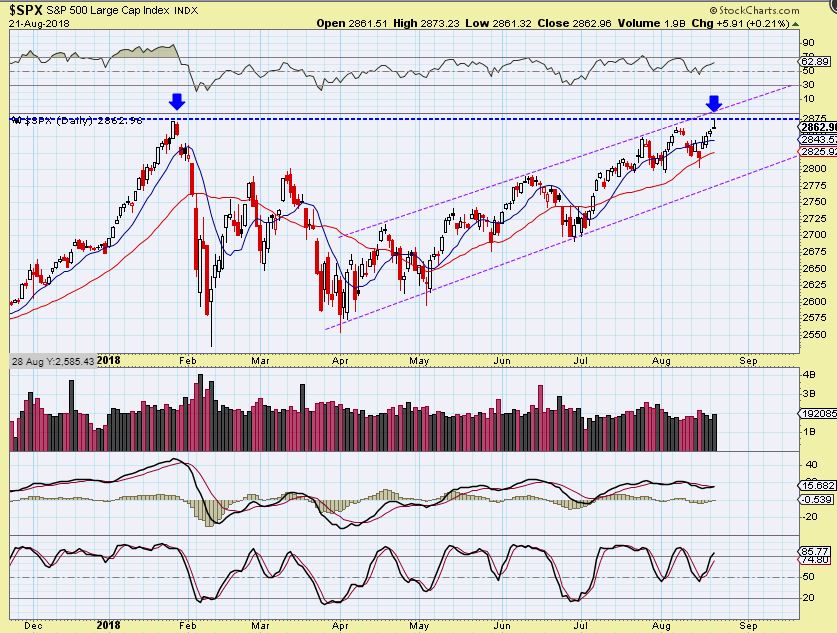 Read More
Read More Read More
Read More