Aug 18th – Friday Again
Let's talk about 3 things here today...
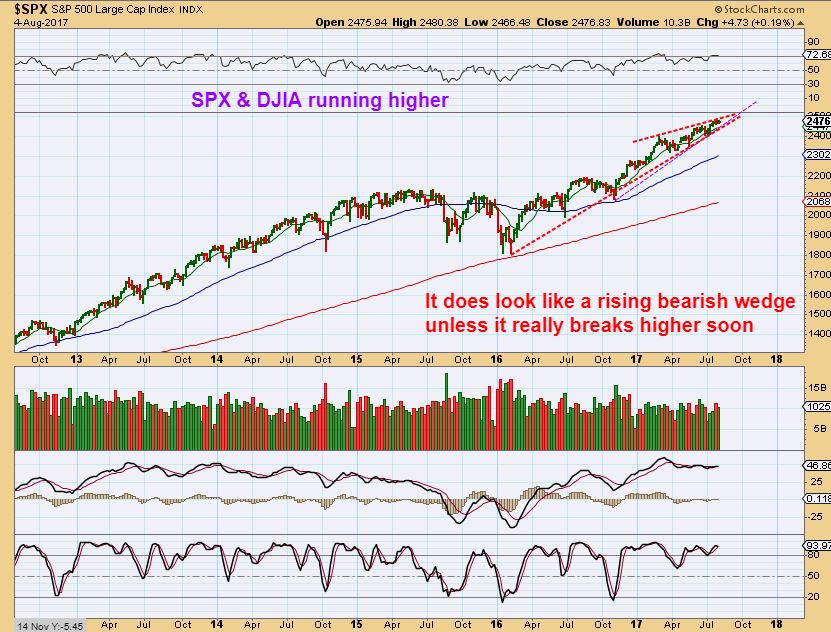
1. QQQ - I thought that QQQ was a bull trap for several reasons, like Cycle timing, The MACD, the Open Gap was pretty obvious, and other internal factors were keeping me cautious, but the Bulls were still buying each reversal.Was this just another Bull Trap?

QQQ - The NASDAQ dropped as expected, actually losing 123 points. The QQQ slammed into the 50sma and it could bounce from here, but ...