Archive for month: June, 2017
Wed June 28th – Buy The Dip?
/123 Comments/in Premium /by Alex - Chart FreakBuy the dip? I would say that one might want to be careful when choosing where or when to enter this time.
.SPX - It is day 27 and there is time to drop further, but we are also due for an ICL (overdue), so this could drop even further than many expect in my opinion.

QQQ - Yesterday I pointed out the MACD on the QQQ ( Nasdaq too) . This looked ready to drop.
 Read More
Read MoreTuesday June 27th
/128 Comments/in Premium /by Alex - Chart FreakIn the last few reports I have been discussing a good number of bullish trade set ups that have been forming after sell offs and consolidation periods. In some areas, the entire sector seems to be reacting. We will continue that discussion today.
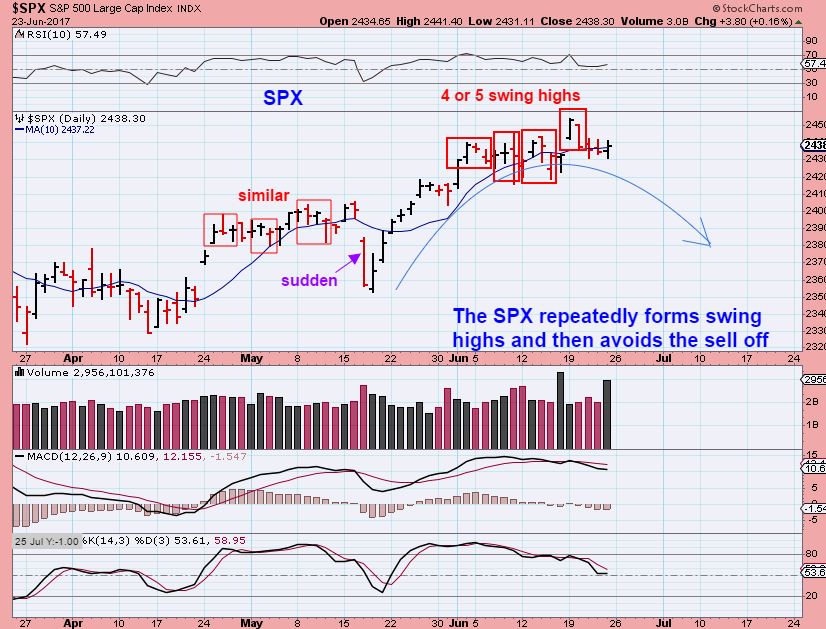
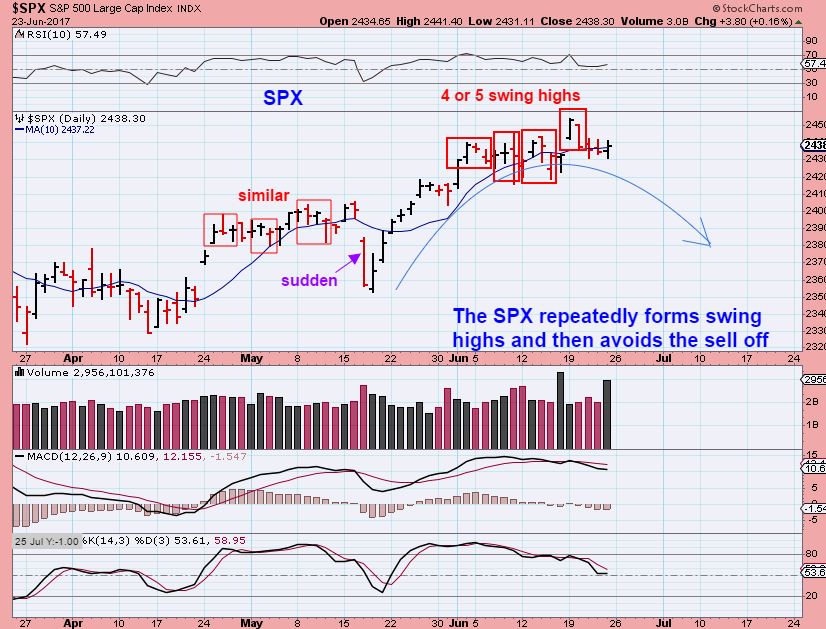
SPX FROM JUNE 23 - The bulls and bears are battling, but this looks like a topping process. We are due for a correction in the general markets.
QQQ - Monday saw a bit of a bearish reversal in the Q's, and that MACD is not showing signs of strength.

I discussed in the weekend report that we are due for a steeper pull back into an ICL, and...
Read MoreWeekend Report June 25 – Perking Up
/216 Comments/in Premium /by Alex - Chart FreakWe have seen an increase in trade set ups and patterns following through the past couple of weeks, and it actually looks like this may continue for a while. Let's review the markets and then we can discuss that...
SPX - Fridays report - We could dip down and back test the break out.

SPX - We do have a swing high in place, but that has happened a lot lately. We closed below the 10sma, but then recovered it. The bears take control and the Bulls buy it back.
SPX WEEKLY - The weekly chart bullishly climbs along the 10ma.
 Read More
Read MoreFriday June 23
/228 Comments/in Premium /by Alex - Chart FreakSPX - We are really well along in the entire intermediate cycle, so I would expect this daily to top and become L.T. and begin to drop. We are overdue for an ICL, but these markets have just been pure bullish.
 Read More
Read MoreThursday June 22 – BOUNCE?
/182 Comments/in Premium /by Alex - Chart FreakThis was my IBB Weekly chart on June 20th. It is breaking out in bullish manner ( It hit 316 yesterday) and has the potential to get to 330 in a few weeks. The daily chart could back test the break out or it may just bull flag and continue higher.

I will discuss this further later in the report.
Read MoreWednesday June 21
/162 Comments/in Premium /by Alex - Chart FreakSo far, The SPX has put in a swing high every 4 days or so, 🙂 and here we see another one. Since we are getting late in the intermediate cycle, and since we are on day 22 of the daily cycle, I am watching each swing high as a possible top. A break of the lower trendline could escalate the selling, so my stop would be below that.

The NASDAQ...
Read MoreJune 20 – Market Snapshot
/146 Comments/in Premium /by Alex - Chart FreakOn the weekend, I used this chart to point out that the NASDAQ did find support on the 10 weekly MA. This is often an area that holds as support, so would the markets move higher from here?
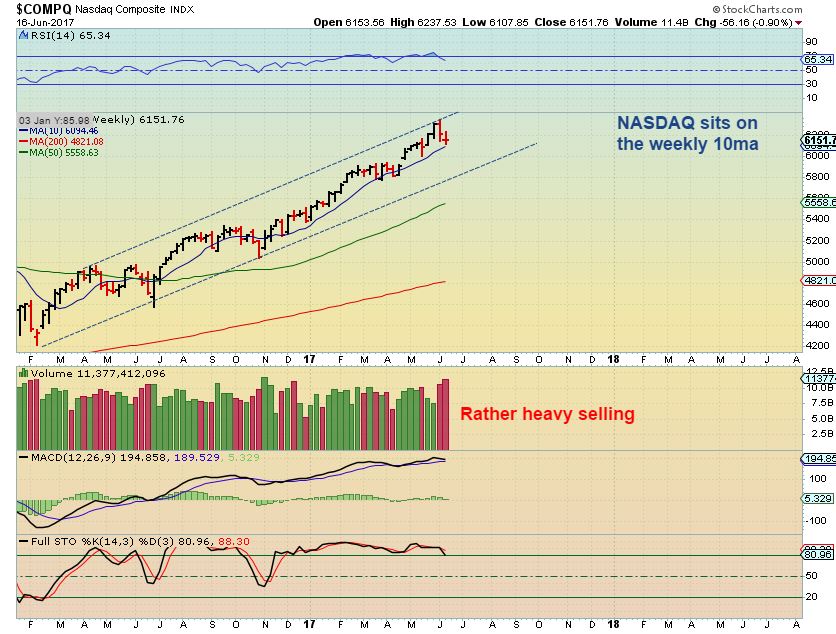
The markets did move higher, and I would use recent lows as a stop.
 Read More
Read MoreA Few Trade Ideas For Monday
/52 Comments/in Premium /by Alex - Chart FreakI posted the following 2 charts in the weekend report as a reminder of a few trade ideas that we are currently watching. I have a few more that I wanted to add before the market opens...
NAK - we have been accumulating this on and around the 200sma for months. Friday mornings report showed that NAK was back on the 200sma, and it popped Friday...

We also looked at this chart again...
Read MoreContact Us
26 Broadway,
8th Floor
New York, NY 10004
admin@bigleaguefinance.com
admin@bigleaguefinance.com
Latest Blog Posts
accelerator diet pills goji berry diet pills ultra 90 diet pills keto meal replacement bar top weight loss diet pills for thyroid patients where to buy t lite diet pills keto friendly thickener diet fuel diet pills peanuts keto friendly rite aid diet pills that work envy diet pills diet pills for breastfeeding moms belique diet pills perfect slim weight loss pills calories in a bottle of white wine