Archive for month: February, 2017
WEEKEND REPORT – Solving Puzzles
/197 Comments/in Premium /by Alex - Chart FreakWelcome to the weekend report after a semi puzzling week. We saw higher Gold & Silver prices, and lack luster GDX GDXJ performance. Let's get right into the weekend report...
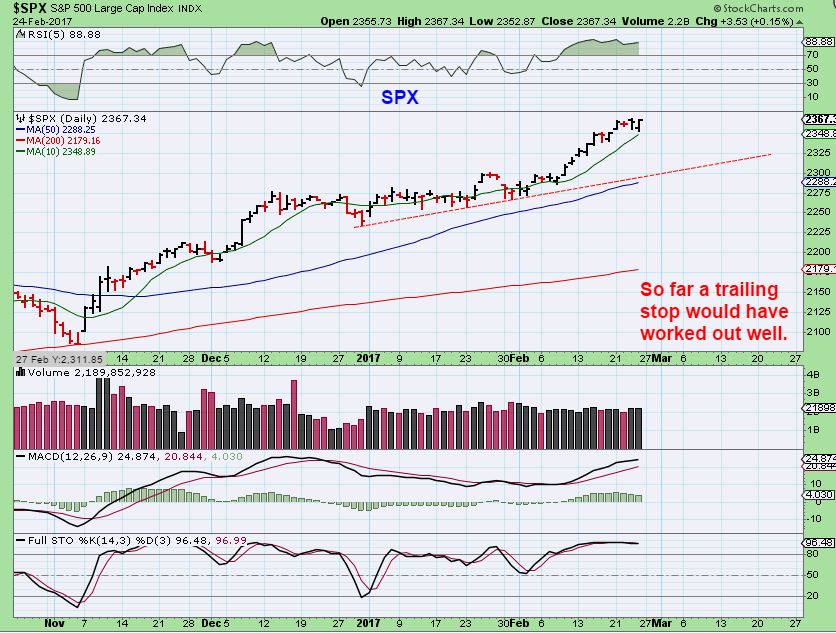
.SPX - I have a target for this move, but on Feb 22 I thought we could get a multi-day pullback to the 10sma before moving higher. This would be similar to what we saw in December.

SPX - We have had a 4 day sideways move to the 10sma, stronger than that dec drop, and another reversal higher Friday. Will we reach 2427 on this run? At this point in our timing, I would expect a dcl before getting that high, and then a continuation higher. The markets have been strong in this area of new highs ( no resistance) so time will tell. As recommended, a trailing stop would have worked very well.
 Read More
Read MoreSTICK THAT LANDING
/177 Comments/in Premium /by Alex - Chart FreakIf you want to look good while you're performing tricks on the slopes, you definitely need to stick that landing. Let's see if we had that in Thursdays trading...
GOLD - We were looking for a higher high to give us a peak that could make this a right translated daily cycle. Gold stuck the landing with this break out, and the volume was encouraging.

If Gold continues to stick the landing, it should make it to this target area.
 Read More
Read MoreFeb 23 – No Change?
/131 Comments/in Premium /by Alex - Chart FreakThe Fed Minutes were released on Wednesday at 2 P.M.. Was there any change?
SPX - No change here. We could use a pause if we are going to reach a target of 2400+.
 Read More
Read MoreFeb 22 Review
/181 Comments/in Premium /by Alex - Chart FreakWe've only seen one day of trading after a 3 day weekend in the U.S., so this report will just be a brief review of the markets and a few of the trade ideas discussed recently.
.SPX - Nothing has changed here, we are seeing a strong move into new highs with no real resistance, I have targeted 2400 since the break out. It is getting quite over bougt and over heated.
 Read More
Read MoreMore Low Lying Fruit?
/117 Comments/in Premium /by Alex - Chart FreakI wanted to put out a bonus report on Tuesday morning. Realistically we probably have enough on our plate, so if you are happy with your current positions, please just view this as a possible heads up for possible future trade set ups or a watch list going forward. In the past few months we have been trading Energy, industrial Metals like CLF, VALE, WRN, NAK, X, etc. We have been trading in the Precious metals sector ( I also encouraged readers to buy & just hold on to some positions from the December lows forward ).
You may also recall my special report in December on another sector that turned very bullish. We will discuss that a bit further here today, as well as what could be some more low lying fruit in another sector that may be sending out some bullish shoots. These are just extra trade ideas for the active traders. Let's take a look...
Read MoreFeb 18 Weekend Report – Another Big Picture Review
/19 Comments/in Premium /by Alex - Chart FreakFor the weekend report, I often feel the need to review the Bigger Picture to gain perspective. I am going to do that this weekend too. To open this report, I'm going to start with a scare tactic. Yes, that's odd, but I see it all the time in the markets, and I believe that there is no better way to face your fears than to, well... Face Your Fears.
.This Chart is an actual Real Bull Market that I have clipped for us to look at. I am calling it Gold ( though it wasn't) and it has a similar movement to what we just saw when the Miners ran higher in 2016 and peaked in July/ August, and then sold off. The Fear tactic is that we always hear "Gold is in a bear market and must drop below $1000 to re-set." Well, now I have heard that this was just a bounce and is an A-B-C-D down to $1000 in Gold & will put the Miners into single digits. Please read the chart.

Compare it to GDX currently - We see the big run up in 2016, The peak in July/ August, followed by a strong sell off. All very similar to the above chart. Are we in for a massive sell off? That is what I'm starting to hear again. "GDX has hit resistance and is just too weak to push through."

Now that I've got your attention - lets look at the bigger picture in all sectors of the market, and answer that nagging question that is being raised above.
Read MoreFeb 17th – Choices
/217 Comments/in Premium /by Alex - Chart FreakThere are times when I feel like I can't even find a solid trade set up, and then there are other times when I feel like there are plenty to choose from. Right now, I feel like I'm seeing a lot of trade set ups. This Friday edition is going to feature some trade set ups after a quick review of the USD, NATGAS, and Precious Metals.
. Read MoreFeb 16 – Building Bridges
/331 Comments/in Premium /by Alex - Chart FreakSometimes building bridges by means of consolidation pave the way to higher ground. I will discuss that later in the report, after a quick market review.
.SPX - Again, this is like a melt up phase, and if I were long I would use trailing stops and let it ride. That long bridge of consolidation has built up some energy.

This was eye opening...
Read MoreFeb 14th – Yellen Is Done Testifying
/156 Comments/in Premium /by Alex - Chart FreakTuesday had Janet Yellen speaking before congress, and the USD and Gold both actually acted as expected. That's a relief. Let's review the markets and then of course we have to discuss the day that Nak got Whacked. What can we expect next after that big reversal?
.SPX - The markets are on their way higher after a long consolidation. That consolidation gives energy to the move and even though the vix is low, I would just use a trailing stop and follow this higher. It is turning into a nice steady move higher at this point, and these can just melt upward.
 Read More
Read MoreContact Us
26 Broadway,
8th Floor
New York, NY 10004
admin@bigleaguefinance.com
admin@bigleaguefinance.com
Latest Blog Posts
accelerator diet pills goji berry diet pills ultra 90 diet pills keto meal replacement bar top weight loss diet pills for thyroid patients where to buy t lite diet pills keto friendly thickener diet fuel diet pills peanuts keto friendly rite aid diet pills that work envy diet pills diet pills for breastfeeding moms belique diet pills perfect slim weight loss pills calories in a bottle of white wine