Archive for month: December, 2016
Dec 29th: High Five -Things Are lining Up
/199 Comments/in Premium /by Alex - Chart FreakWhat is lining up? Let's take a look.
.DJIA - I do believe that DOW 20,000 will have to wait for 2017. This is dipping into a daily cycle low.
 Read More
Read MoreWednesday December 28th – 20,000
/100 Comments/in Premium /by Alex - Chart Freak.
All eyes on Dow 20,000. It was close, but we didn't quite get there yet.
.DJIA - I'm expecting a drop into a dcl, but the question remains, "Will we see Dow 20,000 before 2017?" It is possible, but then I think the markets experience that pull back.. Dow 19980.24 was the high Tuesday.

We do have a right translated daily cycle, so I would expect Dow 20,000 sooner or later.
Read MoreDEC 25 WEEKEND REPORT
/109 Comments/in Premium /by Alex - Chart FreakWe have one shortened week left in the trading year, and it could be a light volume week at that. Lets review what happened last week and see where we could be heading from here.
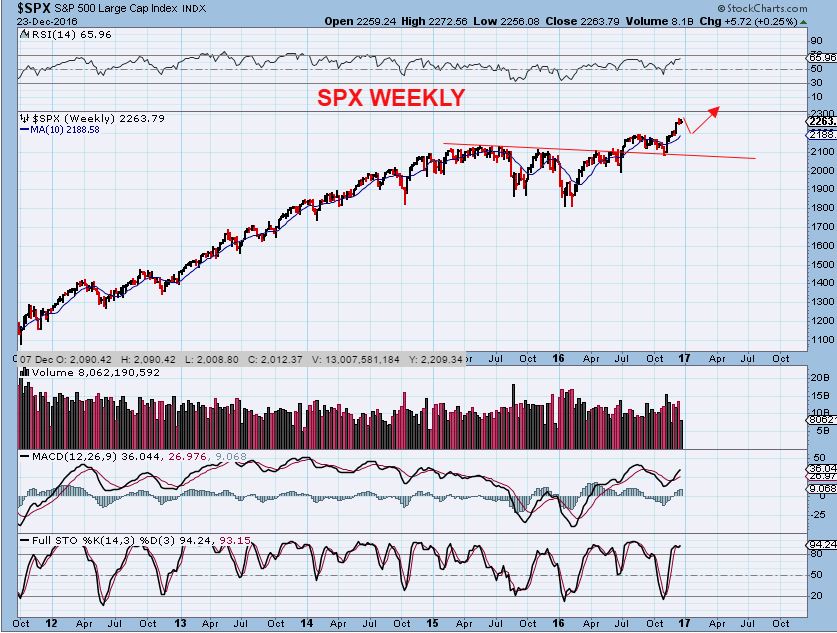
.SPX - Though this looks like a bull flag, it also now looks ready to dip down into a dcl. The red line is the 50sma, near 2188, and would be a normal downside target. The Vix dropped very low last week, and a pull back is due.

SPX WKLY - The blue line is the 10ma on a weekly basis, at 2188. Again, a possible target for a normal healthy pull back.
 Read More
Read MoreDec 23 – Stock Picking
/55 Comments/in Premium /by Alex - Chart FreakNo doubt you've seen someone in the produce section or even out in a field picking apples, strawberries, or some other food product. They usually wont just grab the first one that they see, but instead they will compare one piece of the fruit side by side with another piece of fruit. They are looking to see which one looks healthier, or possibly which one might be flawed, so that they can choose the one that is best for them or their family.
Read MoreThursday – Dec 22 – Day After Day
/98 Comments/in Premium /by Alex - Chart FreakYesterdays reports called 'Baby Steps' discussed how the markets have been moving slowly along, and how that can eventually lead to a particular outcome. Well, most areas of the markets continued that slow crawl yesterday. If you read yesterdays report, nothing has really changed in many areas, except for Natgas. Today we will briefly review and discuss a few of these areas again.
.
Did the Dow hit 20,000 yet? It was only 13 points away when I pointed out this chart
 Read More
Read MoreWED Dec 21- Baby Steps
/86 Comments/in Premium /by Alex - Chart FreakOn Tuesday, the markets continued to take some baby steps. Not only did we see The DJIA take more baby steps toward Dow 20,000, but the VIX took baby steps toward the lows of the year. Add to that Oil, Gold, and the Miners taking baby steps of their own. Lets take a look and see what direction things seem to be heading in.
DJIA - The Dow was only 13 points away from tagging the big round number 20,000. Since the VIX is below 12, we would usually expect a top to be forming, so the big party may be short lived once the Dow achieves that goal.

Read More
Tuesday Dec 20th
/100 Comments/in Premium /by Alex - Chart FreakNothing has really changed since the long weekend report, so lets just review what has happened on Monday.
.SPX - We are due for a pullback into a dcl soon, but this looks like a bull flag forming, so one more pop higher could be in order first. A pop now could help the DJIA to reach 20,000 ( And then a drop would be expected).
 Read More
Read MoreDEC 19 – MORE STOCK PICKS
/99 Comments/in Premium /by Alex - Chart FreakI wanted to share a couple of trade ideas that would be considered low risk , since a stop can be placed just below the purchase price.
Read More
Dec 17 Weekend Report – Precedence
/14 Comments/in Premium /by Alex - Chart FreakWe have seen some unusually deep selling in the precious metals sector, so I do want to discuss whether or not there is any past 'precedence' in this area later in the report. First let's discuss what has happened in just the past week. To the charts...
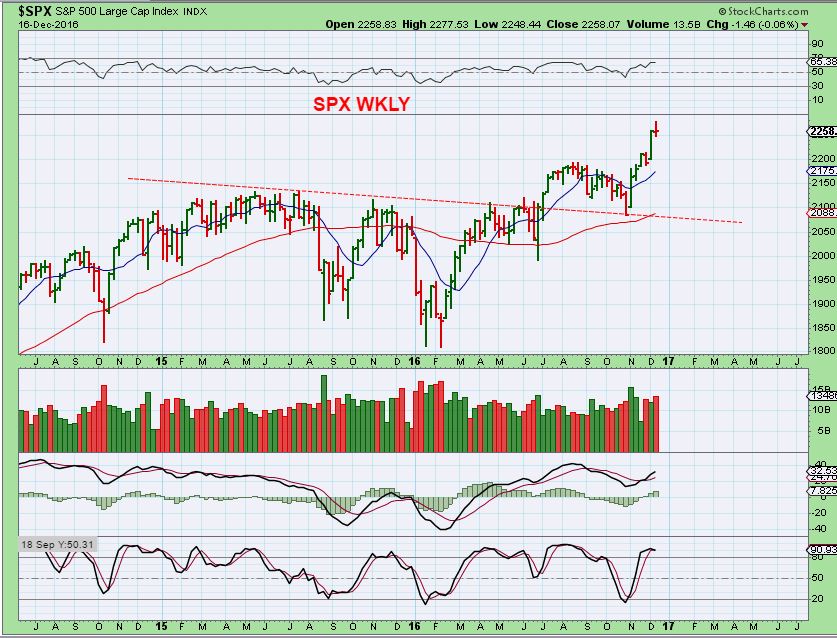
.SPX - Dec 12th, I was looking for the run to stall, and we should see a pullback.

SPX - We have stalled and pulled back a little. A break of this trend line could bring a little more selling, but this will likely be a right translated daily cycle and we can expect higher highs on the next one too. The red line is the 50sma.

SPX WKLY - And we do see a form of topping candle on the weekly. Falling to the blue line at 2200 would also back test the break out.
 Read More
Read MoreContact Us
26 Broadway,
8th Floor
New York, NY 10004
admin@bigleaguefinance.com
admin@bigleaguefinance.com
Latest Blog Posts
accelerator diet pills goji berry diet pills ultra 90 diet pills keto meal replacement bar top weight loss diet pills for thyroid patients where to buy t lite diet pills keto friendly thickener diet fuel diet pills peanuts keto friendly rite aid diet pills that work envy diet pills diet pills for breastfeeding moms belique diet pills perfect slim weight loss pills calories in a bottle of white wine