Archive for month: November, 2016
It seems that many things within the market structure are lining up again. Let's take a look...
.
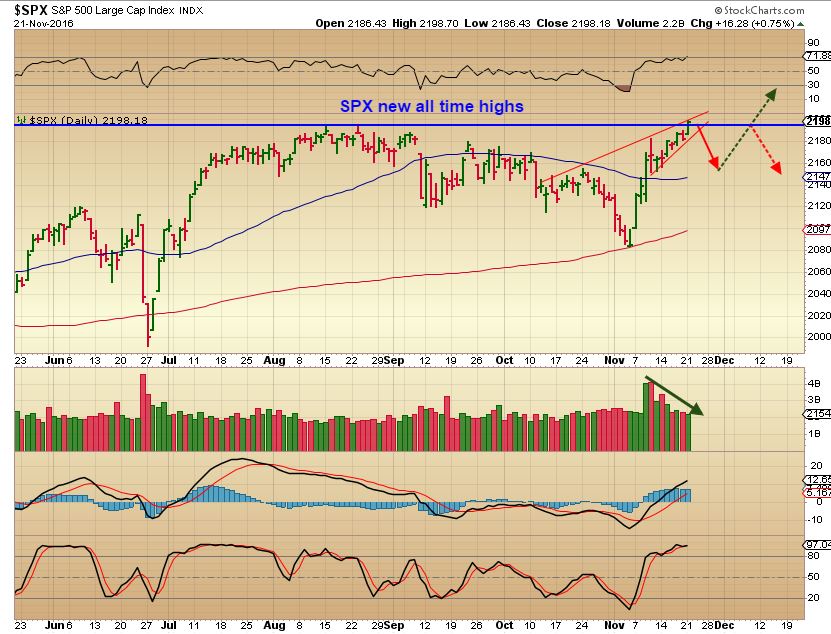
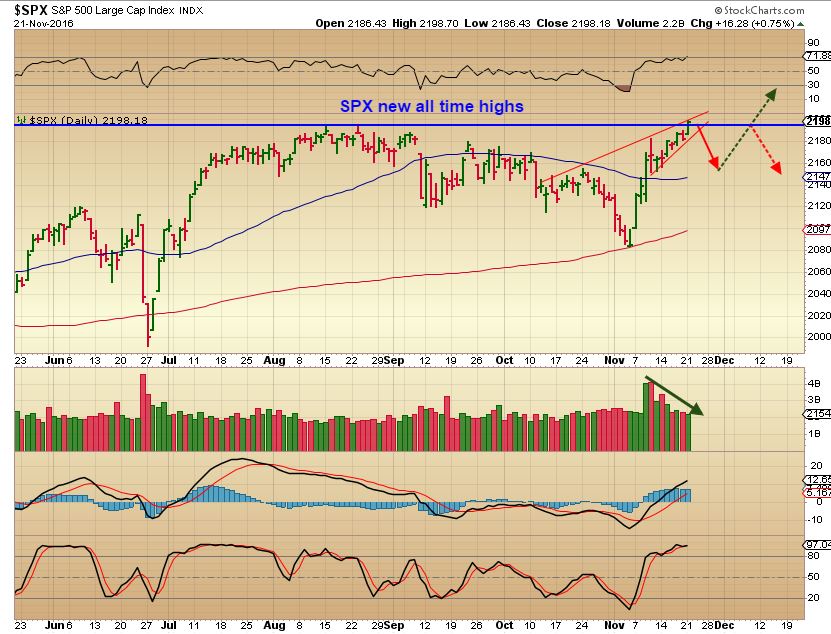
SPX - We did get our initial burst higher out of the anticipated lows as shown on the 2 charts below.
.
This was Oct 31 - Anticipating the trade-able low

SPX now - We got the lows and the initial run higher, but will it continue? Notice how the 13 SMA affected the first run. The 2nd run tagged it and then crawled sideways for weeks. No good trade resulted Long or Short for months last summer, and that may happen again. It can still be bought or held above that 13 sma.
 Read More
Read MoreWhen you look at the flowers in the above picture, you cannot really tell what the future will hold at this point. It is hopeful as we begin to see growth, but the surrounding conditions are difficult. Will it remain too dry for growth or will some refreshing rains begin to nurture it? And even if all of the conditions exist for solid growth, will it avoid being trampled on?
What does this have to do with the Precious Metals market? We'll compare this flowers future with the dry conditions that we've seen in that sector lately and discuss future prospects.
Read MoreThere are many things to keep an eye on going forward, lets take a look.
Read MoreThis is a Friday update on the Precious Metals Sector
Read MoreSometimes things are moving so slowly that you can't believe that they are even moving at all. Well, We've seen this in the Precious Metals Sector over the past few days, but with the release of the Fed Minutes Wednesday, that just might change.
Read MoreIt's a holiday week in the U.S., and Monday didn't bring much in the way of change since the weekend report. On Wednesday we do have the release of the Fed Minutes however, and that may be the catalyst that we are looking for in one area. 🙂 To the charts...
.
SPX - The S&P broke to new highs. I was thinking that it will take a rest, but have you seen the IWM? It looked similar to the S&P now, but it is just continuing higher each day. We may pull back soon, but it is also possible that light holiday trading may just keep it floating higher ( See the IWM). If that happens, it may be on the following week that we see a consolidation or a pullback.
 Read More
Read MoreJust a short report for Friday, where we're discussing a leap of faith 🙂
Read MoreLooking for some change ...
.
SPX - No real change from yesterdays report 🙂
Read MoreHave you ever been driving along using your GPS and you decide that maybe you're going to take a short cut to your destination? The GPS detects that you have left the designated course and immediately needs to compensate by announcing, "Recalculating Route!". Well last week sectors of the markets took sharp detours right after the elections. Using over 50 charts, this weekend report will discuss the road we find ourselves on now.
SPX - Nov 1st , Expecting a trade-able ICL, maybe in the 2070 area.

Read More
Scroll to top

 Read More
Read More