Archive for month: October, 2016
Another week that started off a little unclear in some areas, but I think we're starting to see some clarity now. Lets review the current condition of the markets and then focus on Precious Metals sector.
.
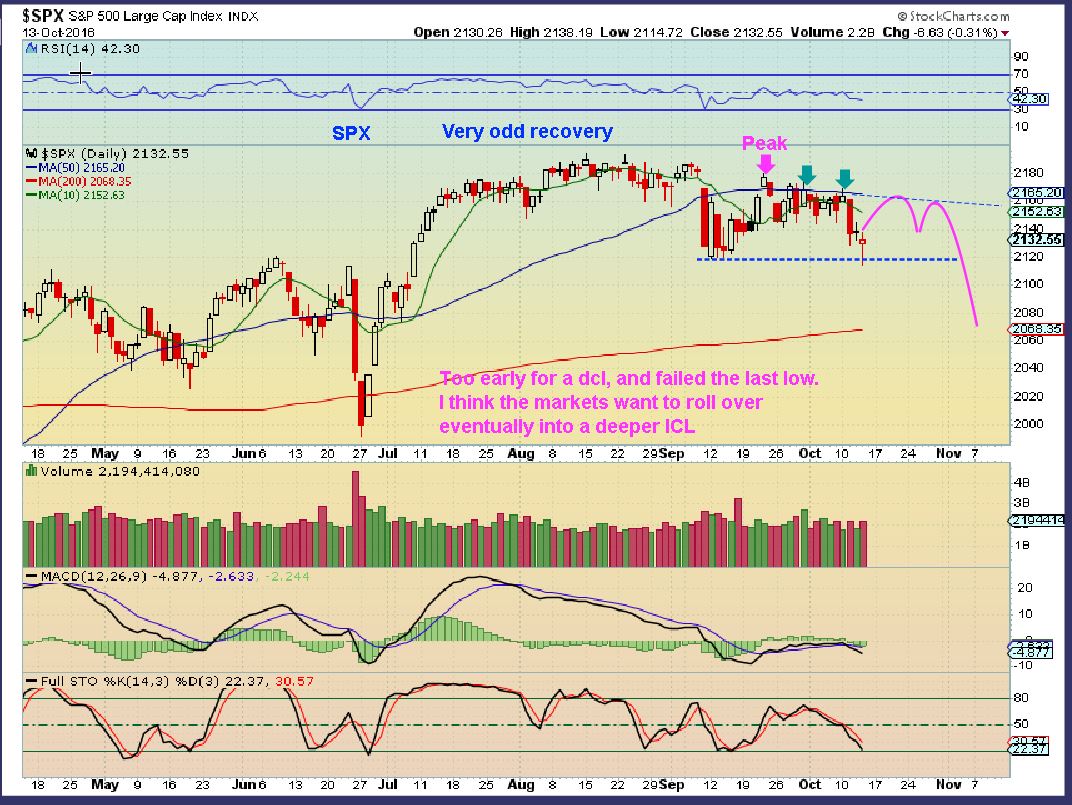
I have been pointing out the potential resistance in the General markets. With the exception of the Nasdaq , which has done a little better, Markets have been rather stagnant. Lets look at the progress over the Month of October.
SPX -This was SEPTEMBER 30th, and the choppiness was making it unpredictable and untradeable.

SPX NOW - 1 Month later and it is a tad lower with a big rounding top. On Oct 13th it broke to a new low and I warned that it now looked like it would NOT go upside until it first breaks to new lows again ( Failed daily cycle). 2077 is currently the 200sma and a possible support.

Lets look at the weekly chart
Read MoreWell, you know the story. I don't usually plan on doing a Friday report. Thursdays report can usually cover what could happen on both Thursday and Friday. We are specifically focused on Gold & Miners , so we should discuss that area a bit before the weekend. Let's start with the $USD.
.
USD Oct 26 - Would the dollar drop into its Daily Cycle Low, or would the 10sma act as suppport? It is overdue to dip down.

USD Oct 27 - It DID use the 10sma as support so far. This Daily cycle rise is longer than normal.
 Read More
Read MoreAt this point in time, we should discuss lines in the sand for protective purposes. First, a quick market review.
.
SPX - No Change at this point. I see a failed daily cycle and weakness so far.

Lets take a look at the USD ...
Read MoreThis report is all about How the internet works, and Gold, Silver and Miners.
.
This is how the internet works...
GDX - This was from my weekend report, and I showed how the 10sma could be tagged by GDX and the drop would back test the trend line. Totally normal, so we were ready.
.
 GDX MONDAY - When it actually happened, this was exactly what we knew should happen. Well, the internet lit up with Bearish chatter. I was hearing that Gold was about to get crushed, Miners were 'crashing' , and the USD was rallying! T-H-A-T is how the internet works now, fear breeds fear. Is this soooooo bad?
GDX MONDAY - When it actually happened, this was exactly what we knew should happen. Well, the internet lit up with Bearish chatter. I was hearing that Gold was about to get crushed, Miners were 'crashing' , and the USD was rallying! T-H-A-T is how the internet works now, fear breeds fear. Is this soooooo bad?

Well lets discuss Tuesday and see ...
Read MoreSo far I think that the action in the markets today basically matched my weekend report, but they were received with mixed fanfare. Lets take a look and review expectations.
.
I was looking at SPX like this, trapped under the 50sma and 10sma.

Today the Markets gapped open higher and the NASDAQ was up near the 2016 highs. Lets take a look.
Read MoreCAN GOLD CONTINUE TO RISE, SINCE THE USD IS MOVING HIGHER TOO?
.
That question and other ones similar to it keep coming up lately and understandably so. Gold usually drops when the USD rises, but lately we do see both rising at the same time. I called a low in Gold recently and have been trading in the Precious Metals sector, but some are having a hard time believing it when they see the USD rising too. Allow me to share my thoughts on this. The following 4 charts are from the weekend report, where I tried to help my readers see the answer that question.
GOLD AND THE USD
CHART #1 -The USD has slowly been approaching the Highs of 2015. The chart does look quite bullish, but it does also show prior lows being taken out and lower highs so far.
 Read More
Read MoreLets get right to the weekend review.
.
SPX 1 week ago - It was struggling to move higher. Not a 'long' or 'short' play going forward, just sideways chop again.
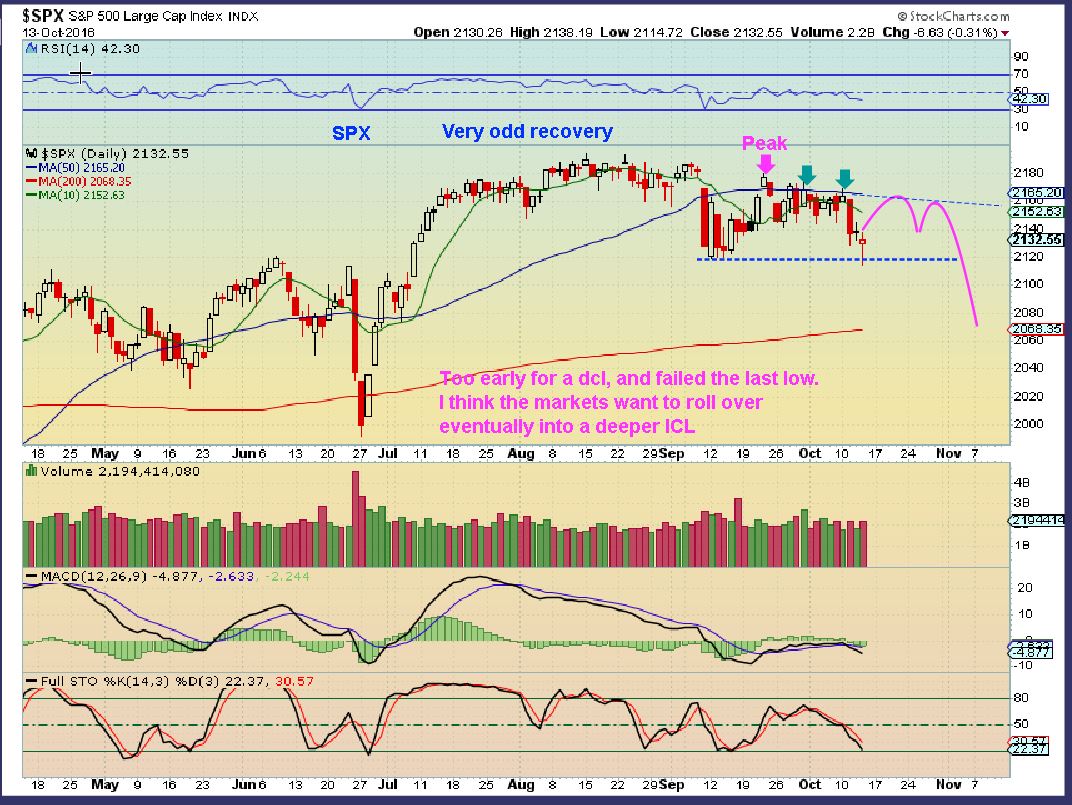
SPX WKLY - No change, still looks weak.
 Read More
Read MoreThere was a time when I only released reports Tuesday , Wednesday, Thursday and the huge weekend report would cover Monday. I felt that the Thursday report would cover both Thursday and Friday and that the weekend report caught us up for the Monday trading. With the Bull markets of Precious Metals, Oil, and Commodities coming alive this year, I have released at least a small Friday report almost every Friday in 2016. Why stop now? 
.
So this is just another short ( short? 13 charts ) report to point out that Thursdays dip or slam down in Gold , Silver, and Miners actually may hint at some underlying strength, and that may be enough to encourage anyone that is a little too light to buy these dips. Lets take a look...
Read MoreThings have been falling into place step by step this week. In this report, I just want to point out a few things that I am watching when it comes to our positions in Miners after a brief review of the Dollar and Oil.
.
USD - This looks bullish really, but it is very stretched according to cycle timing. It should roll over into a dcl soon. The Precious Metals are ignoring the USD when it rises now, possibly a sign that the Dollar is ready to dip down.
 Read More
Read MoreI wanted to title this report "We got it!", that was by request actually, but you will see as we go through the charts that I cannot say that quite yet. Dont get me wrong, I believe that you will like the ingredients of this report, so let's get right to it...
.
SPX - The SPX failed when it dropped below the Sept 12th lows, and has struggled under the 50sma and even the 10sma. It needs to prove itself, but it is struggling. The NASDAQ stocks GOOG, NFLX, AAPL, and others do look bullish, so I am just watching how this plays out over time. I am much more focused on the Gains that can be made in Miners.
 Read More
Read More
Scroll to top