Archive for month: September, 2016
Lets talk about the current window of opportunity
.
WTIC - Wednesday I said that this break out looked legit.

WTIC - And Thursday we saw follow through, but...

This is what I really want you to see ...
Read MoreAfter all of the sideways chop, I think we finally have something interesting to talk about.
.
SPX - If Oil could get moving higher, I think we'll see the markets moving higher too. After all of this sideways chop ( in many sectors), this is a bullish set up with todays strong reversal.
 Read More
Read MoreI've seen choppy markets before, but it seems like Oil and Gold are up one day, down the next , up one day, down the next. It can be very difficult to navigate the choppiness, but Cash is also a position until we get a nice trending market. Other trade set ups are an option too. Lets take a look at the charts.
.
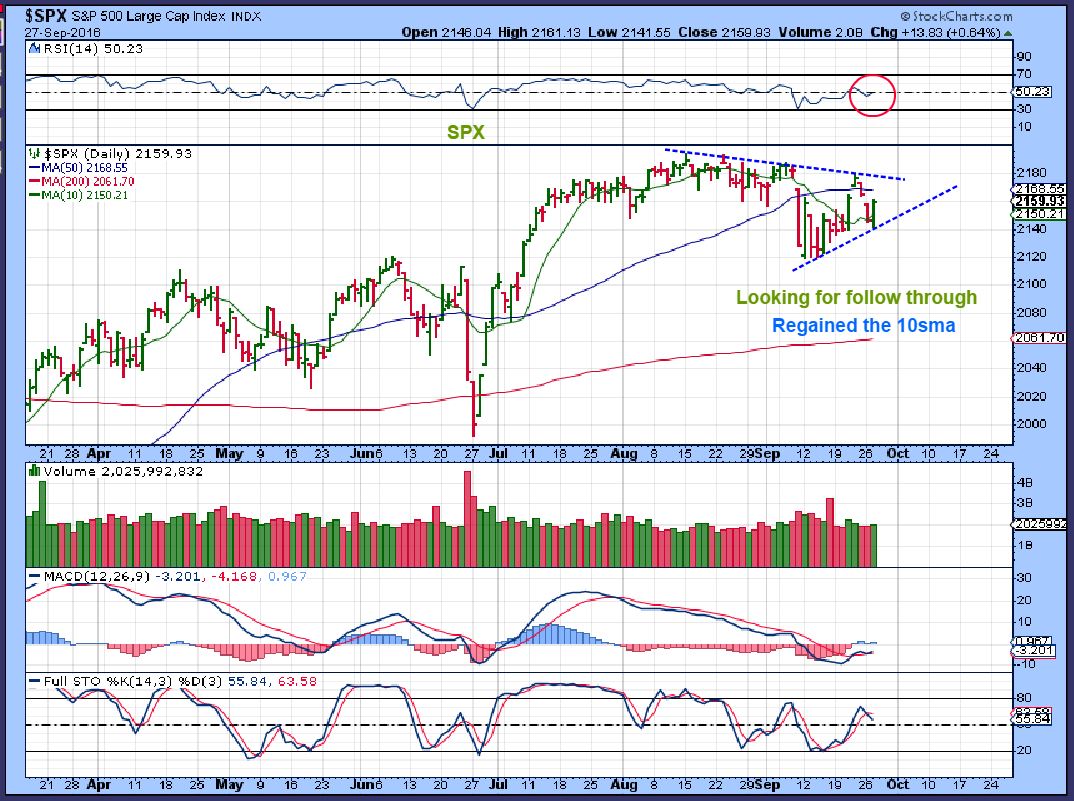
SPX - Short term I see a choppy triangle forming, and the larger picture might be forming a rising wedge. We can look for follow through with a break down or a break out.
 Read More
Read MoreI just want to get right to the point here, lets look at the charts.
Read MoreI mentioned in a few of my August reports that things could remain a bit choppy going forward, especially if we are entering the timing for an ICL in Gold & Miners. We saw this in both OIL and Precious Metals markets in the past, and I will again point that out in this report. That type of price action can be frustrating, because the trade set ups quickly break down and the price action becomes more or less sideways. Lets take a look at what we currently see and discuss what we could expect.
.
SPX - Our daily chart had a possible Island Bottom Reversal, but the gap closed and it lost the 50sma. This is not overly concerning at this point, but I liked the idea of an island bottom.

SPX WKLY - This still looks like a great weekly set up.
 Read More
Read MoreWhat are we watching on Friday?
.
SPX - Yesterday, using this chart, I pointed out that this confirms the daily cycle low, and it is a bullish break.
This could be considered an Island Bottom reversal. It is a bullish break out, especially if that gap doesn't fill.
 Read More
Read MoreMy High School Sociology Teacher used to start his class by saying, " O.K. friends, no fooling around here. I have a lot to cover today, so let's just get right into it." I miss that, and I have a lot to cover too, so lets just get right into it! 🙂
.
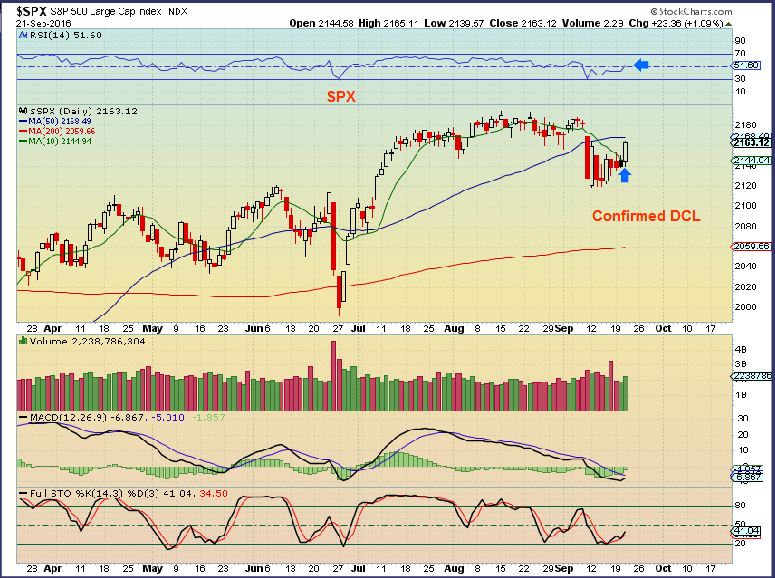
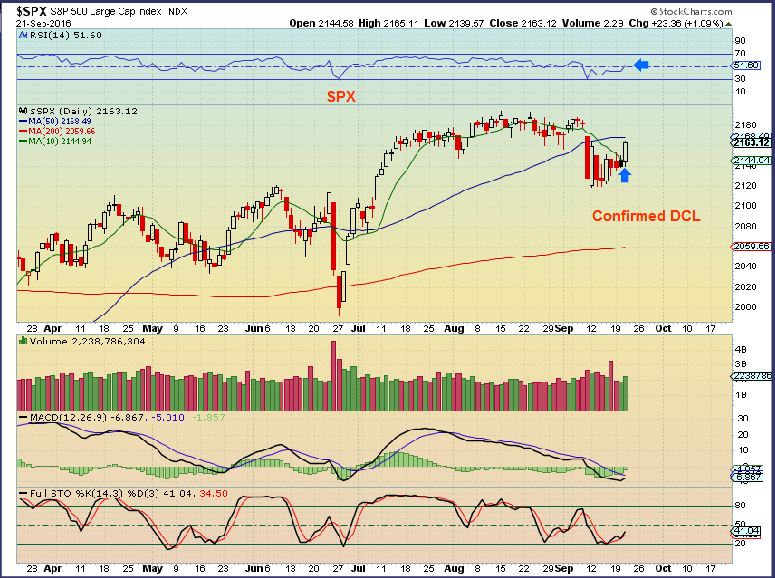
SPX - I discussed that the NASDAQ, IWM, SOX, XBI / IBB, and so on had already made the break higher, as the SPX lingered. The Fed Decision gave it a good push and we have a confirmed DCL and we're on day 7. It is still oversold , and I would expect a break out to new highs sooner or later.
 Read More
Read MoreLets discuss Fed Wednesday
Read MoreI have a core position in Miners that I started early in 2016. As a trader, I have sold most of my shorter term trading positions and I am waiting for the fat pitch to reload. Are we there or is there further selling likely? I believe that we are very close to another run higher in the Precious Metals sector, but we also have the Fed Mtg on Wednesday that could affect things short term. Are there any clues pertaining to short term direction? Please read on...
Read MoreI am fairly heavy in cash in my trading account and with cycle timing being where it is in Precious Metals, I am trying to stay that way going into the Fed meeting.
( I will always have a core position in Miners since admonishing that in early February). We get up each morning in North America and Gold is higher, but as they day progresses, it goes nowhere really. Lets take a look and discuss we we can expect.
.
SPX - We have a swing low in the NASDAQ, RUT, IWM, etc., but we still do not have a swing low in the SPX yet. That DOESN'T mean that the low isn't in place, it just means that it hasn't confirmed itself with some follow through. This has the look of a bear flag, but I would expect a move higher soon with this set up.
 Read More
Read More
Scroll to top



 Read More
Read More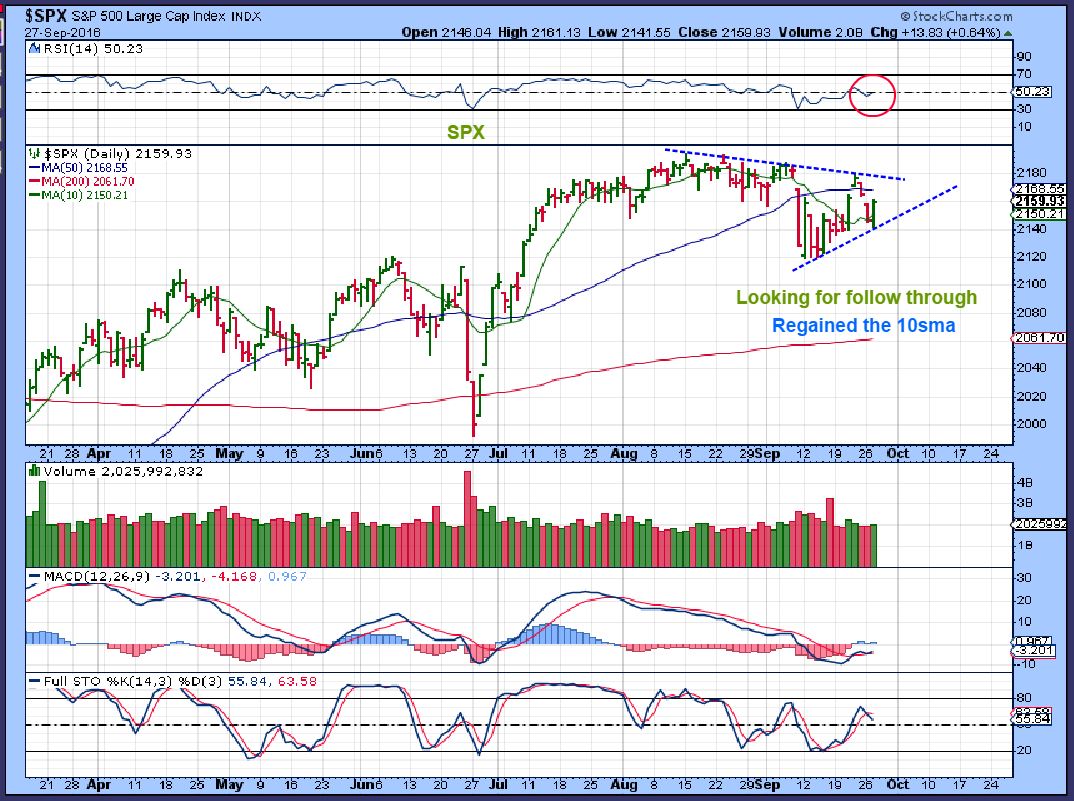 Read More
Read More
 Read More
Read More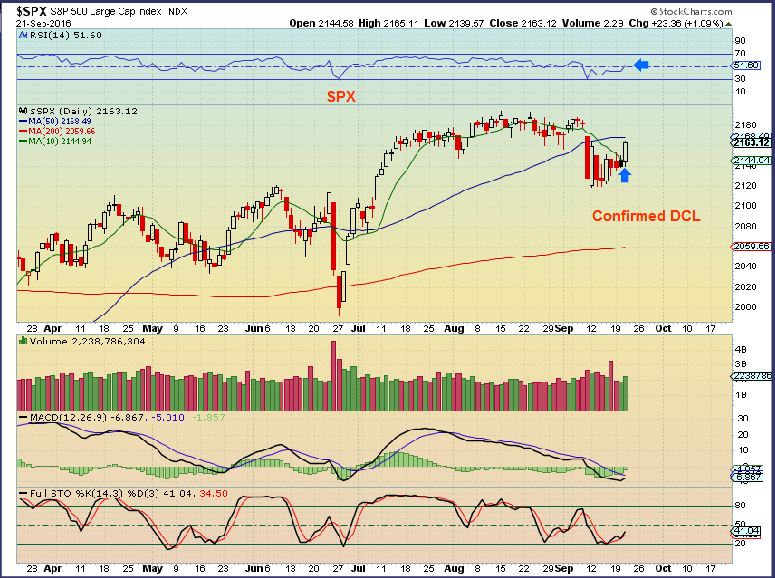
 Read More
Read More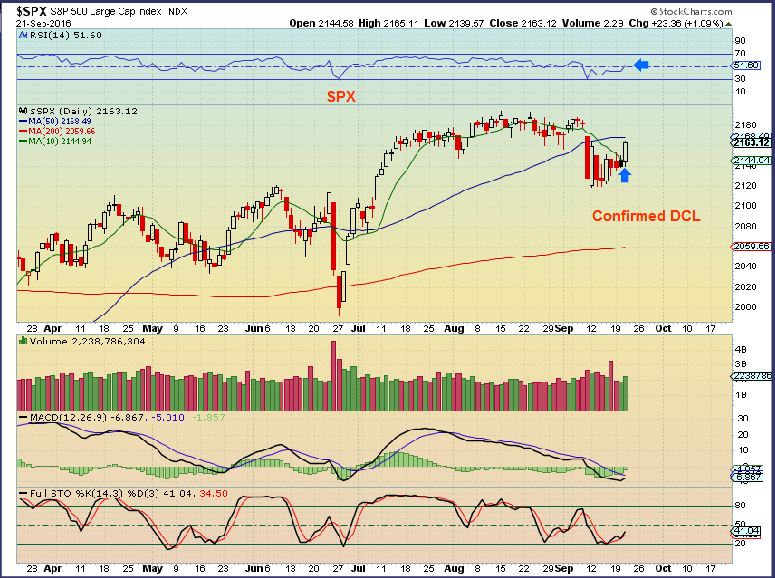 Read More
Read More Read More
Read More