Archive for month: August, 2016
The theme picture is just a reminder: The markets do not usually go straight up to the top 🙂
.
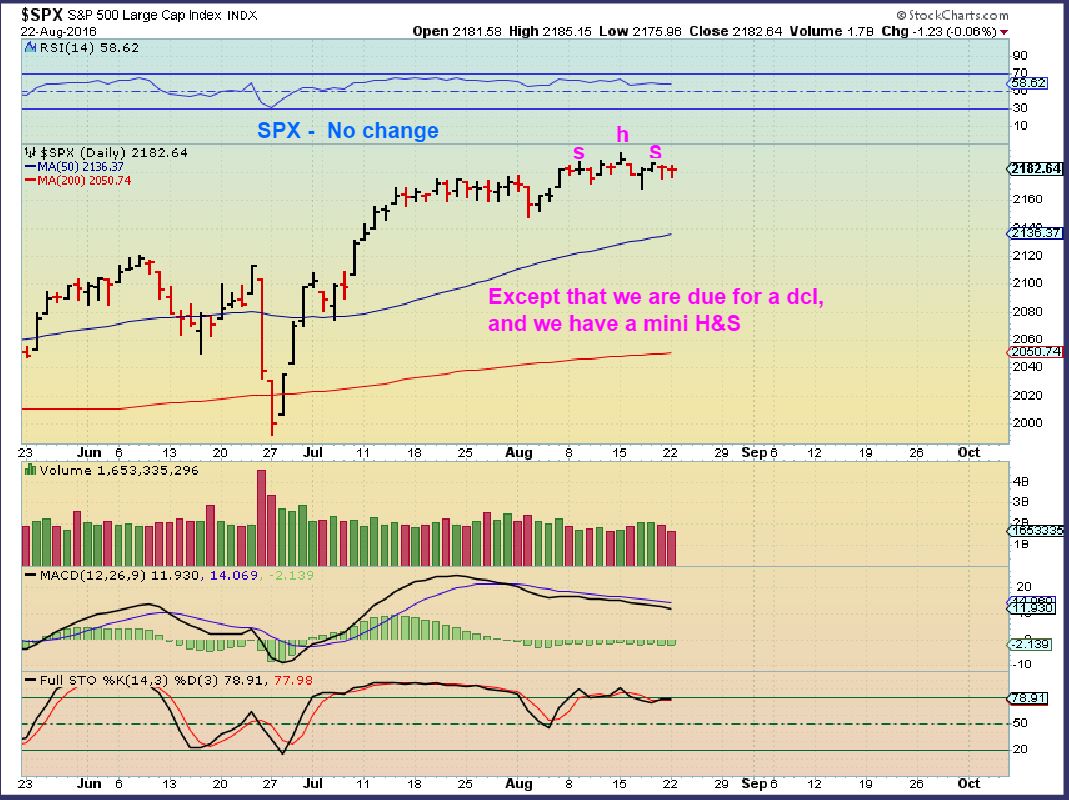
SPX - No change
 Read More
Read MoreMonday didn't bring a whole lot of change since the weekend report, but there are few interesting things to discuss.
.
DJIA - The general markets continue the chop, and as they become oversold, the 50sma continues to rise under price as possible support.
 Read More
Read MoreIt was a week of activity capped off with some Jackson Hole volatility. Lets take a look...
.
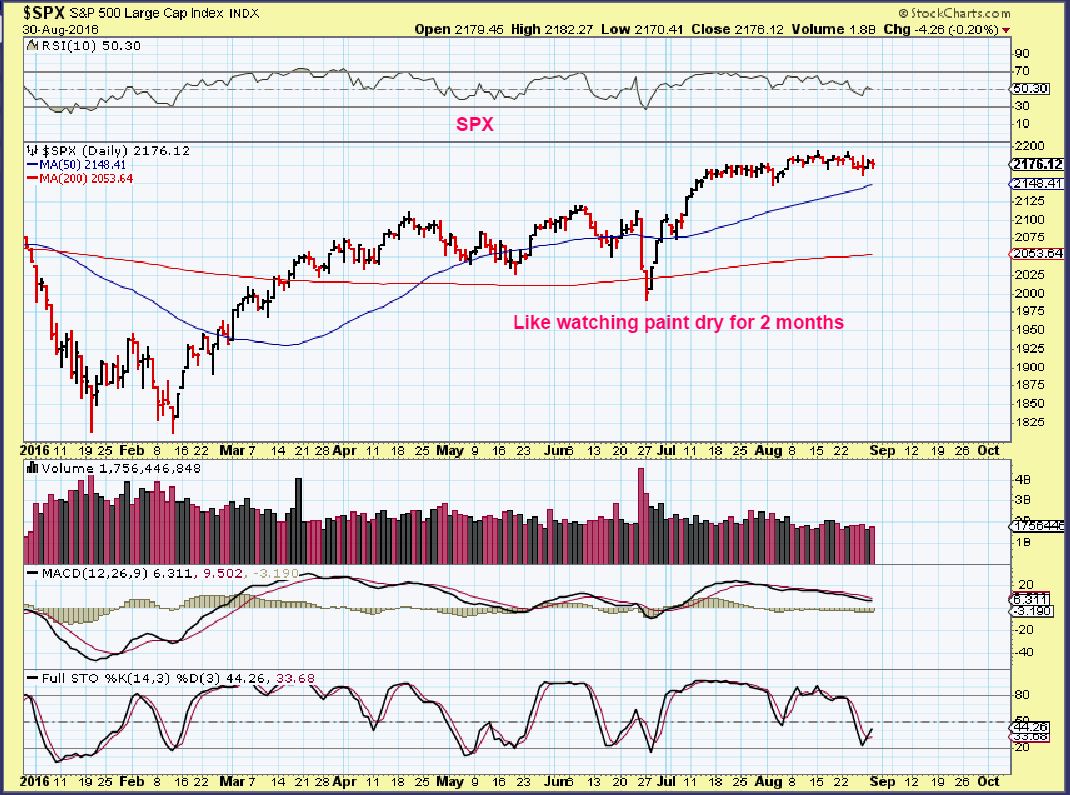
SPX - 2 months of sideways should produce a strong trending move. A dcl could shake traders out first.

SPX WKLY - The weekly shows that we are on week 8 out of the recent lows. The prior move did top on week 10 and dip for weeks before surging and making new highs on week 17, so these markets can be tricky, even when bullishly set up.
 Read More
Read MoreWelcome to Jackson Hole Friday, please make yourself comfortable, we may experience some volatility. 🙂
.
DJIA - I still think that we should get some downside, as we are expecting a dcl.
 Read More
Read MoreThe Bullish love for Miners over the past few months took a bit of a drubbing Wednesday. We didn't see the sellers using the gentle cycle to try to wash away the sentiment, it seems that they may have pulled out that wash board and vigorously scrubbed away at it. Many seemed to be heading for the exits. We'll discuss this further, but first...
The General markets sold down a bit, but we are still within the same consolidation that I've been pointing to for weeks. Any further selling should seek out the dcl that we have been expecting now.
SPX -

.
Read More
At Chartfreak, we were anticipating that a higher low in Oil would prove to be an exceptional buying opportunity after the recent summer sell off. Cycle timing was telling us that it was 'time' for a low to develop, so we began monitoring the charts using technical analysis and cycle timing. Did you buy that dip at the right time? Let me show you what we were watching using actual charts from our August reports. You can ask yourself, if I was a chartfreak member, would this may have helped me with my investing in this sector?
WTIC AUG 3 - Anticipating the coming low, I used this chart to start with. We had a 50% retrace and some Energy stocks were beginning to look Bullish too. I encouraged readers not to buy until we get a break above the tight downtrend.
 Read More
Read More Tuesdays markets sparked my interest in a few ways. Let's get to the charts...
.
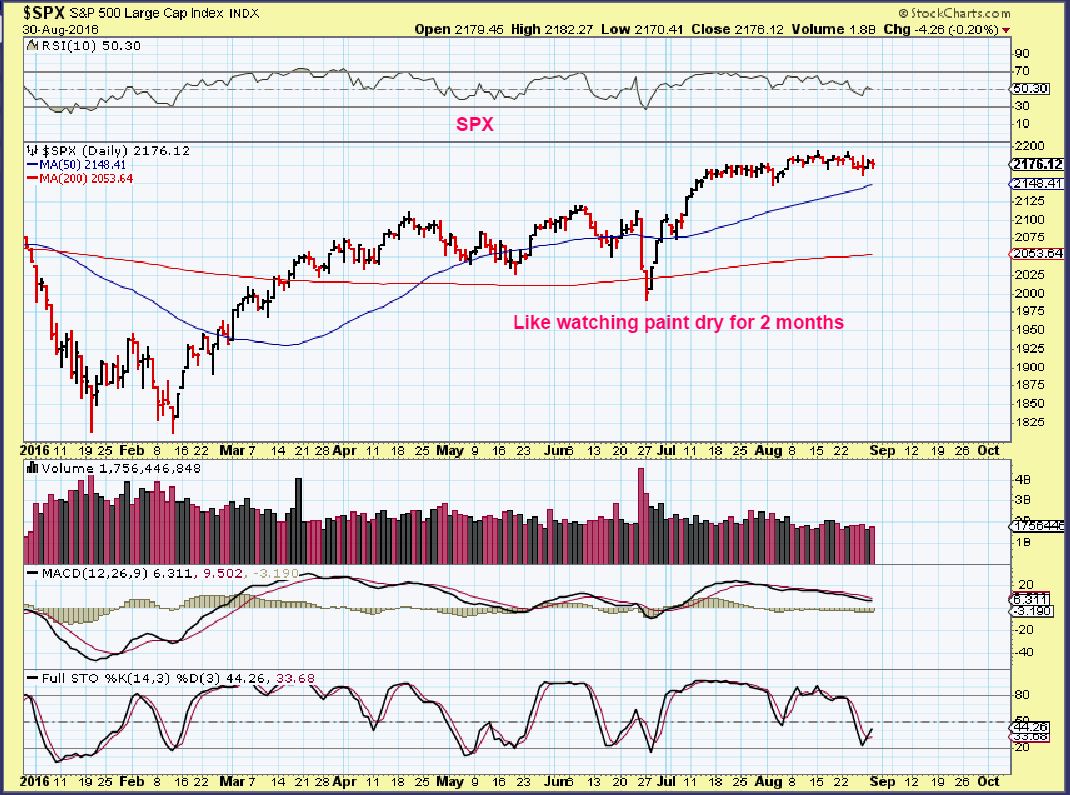
SPX - We've certainly seen this before. Frustrating the longs and the shorts, the sideways move continues.
 Read More
Read MoreAs mentioned in a few prior reports, we are riding through a consolidation zone in some sectors, and now Oil and Energy are experiencing a slight pull back. In Bull Markets, these are healthy events and over time we eventually see higher lows and higher highs. Understandably, these periods where gains are given and then taken back get frustrating for some, especially if they last for long periods of time. With that, I wanted to re-post this recent report from Aug 12th to help us to maintain an unemotional perspective. Please read the article with the link below again, or just skim through it if you have time.
.
CHOPPY WATERS
.
SPX - The set up is bullish, but I am expecting a cycle dip into a dcl, so I am viewing it this way for now. There is a possibility that these markets just remain supported and head upward into a runaway type move. The dips are very muted.
 Read More
Read MoreLooking forward...
.
SPX - The squeeze on the Bollinger Bands usually leads to a strong directional move.
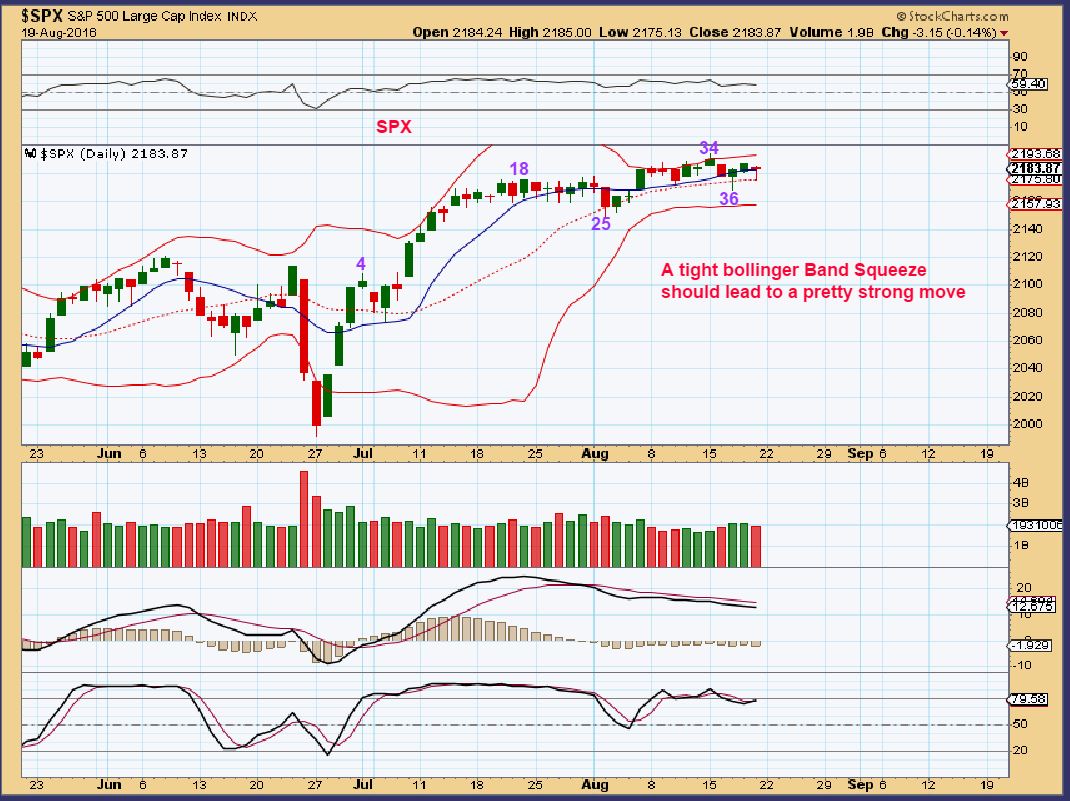
You can see that we are consolidating in a bit of a triangle / wedge and heading into the apex. A break out 1 way or the other should occur soon. A break out higher could lead to a runaway move ...
 Read More
Read MoreAnd as predicted, it is a force to be invested in 🙂
.
WTIC - Many doubted that Oil could come back so quickly, some on CNBC were saying that it would not make it past $44. With an ICL in place, there is no doubt that this chart shows us....The Force Awakened.

We have been investing in Oil/Energy since I pointed out some nice set ups over 2 weeks ago. Some of these gains are already satisfying. Is this it? Will Oil only double top like I hear some saying? I will discuss the potential briefly here and in the weekend report.
Read More
Scroll to top
 Read More
Read More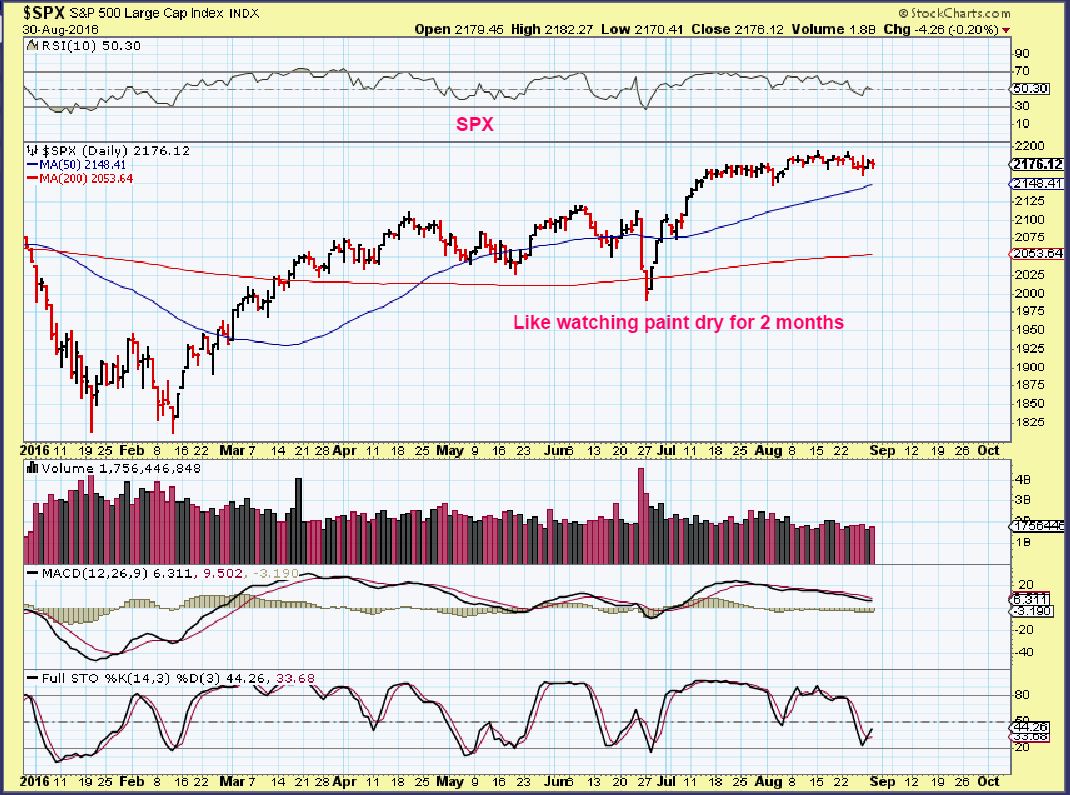 Read More
Read More Read More
Read More
 Read More
Read More Read More
Read More . Read More
. Read More Read More
Read More Read More
Read More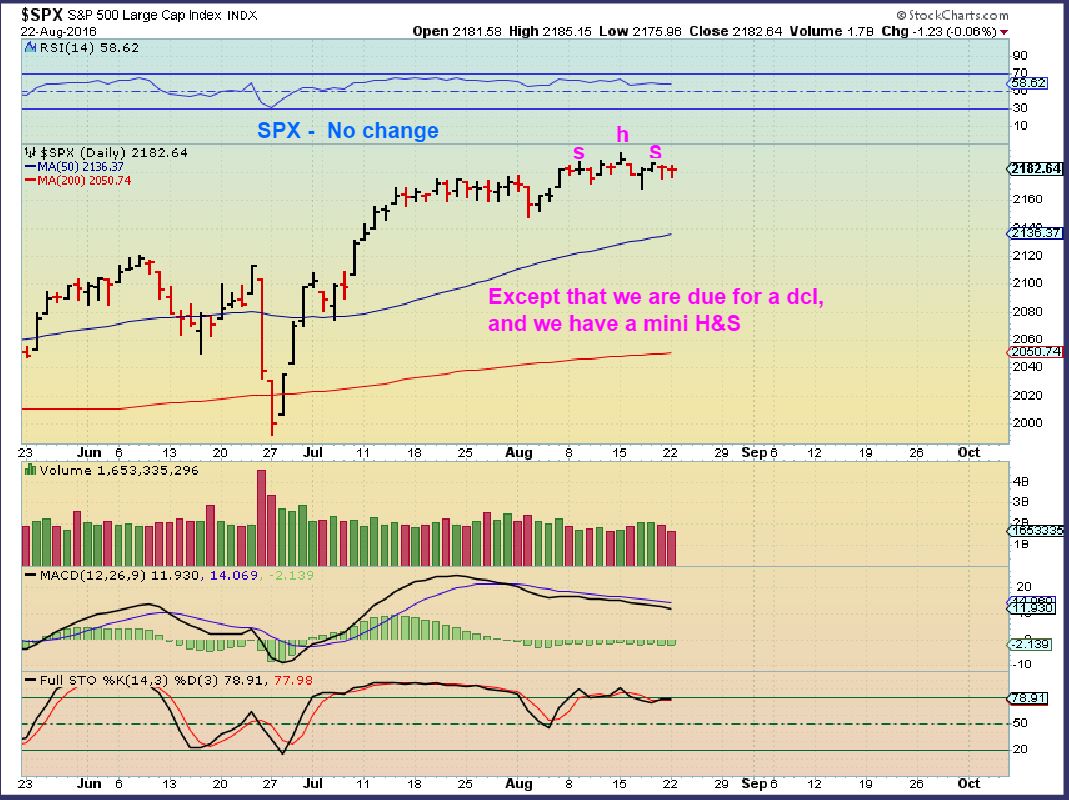 Read More
Read More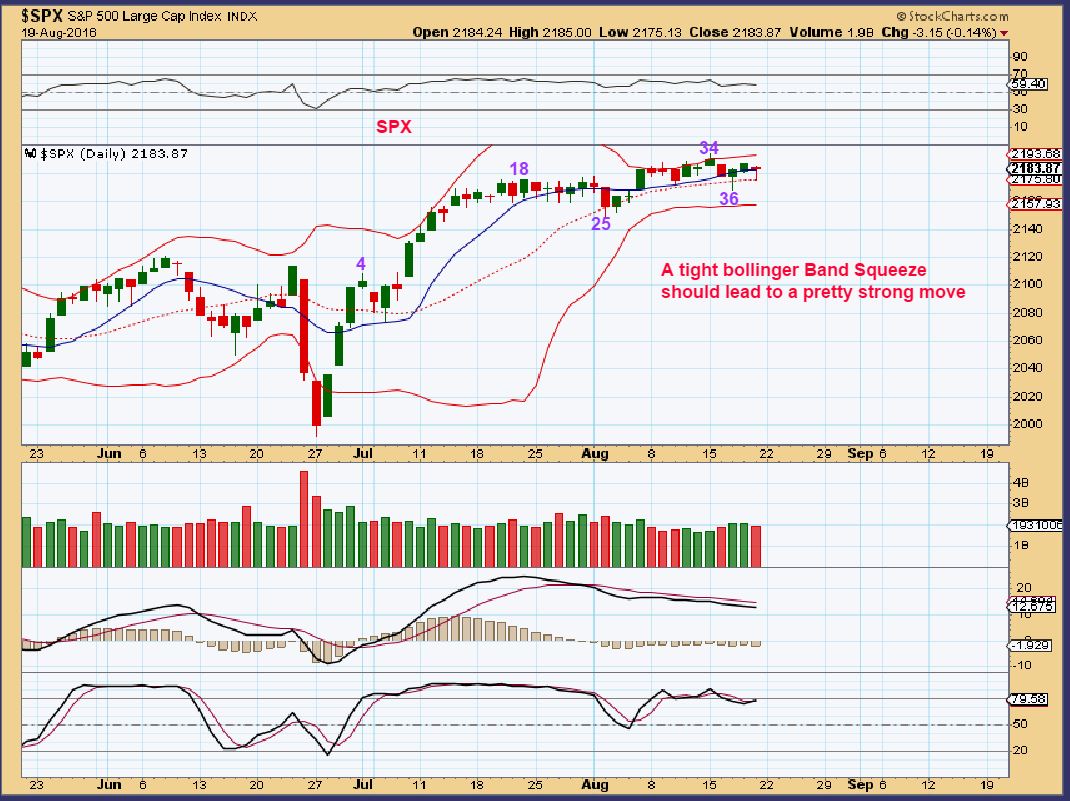
 Read More
Read More
