Archive for month: July, 2016
We've been seeing some strong Bulls running in 2016, and I dont think that the show is over yet. That is great news, lets take a look in our weekend review...
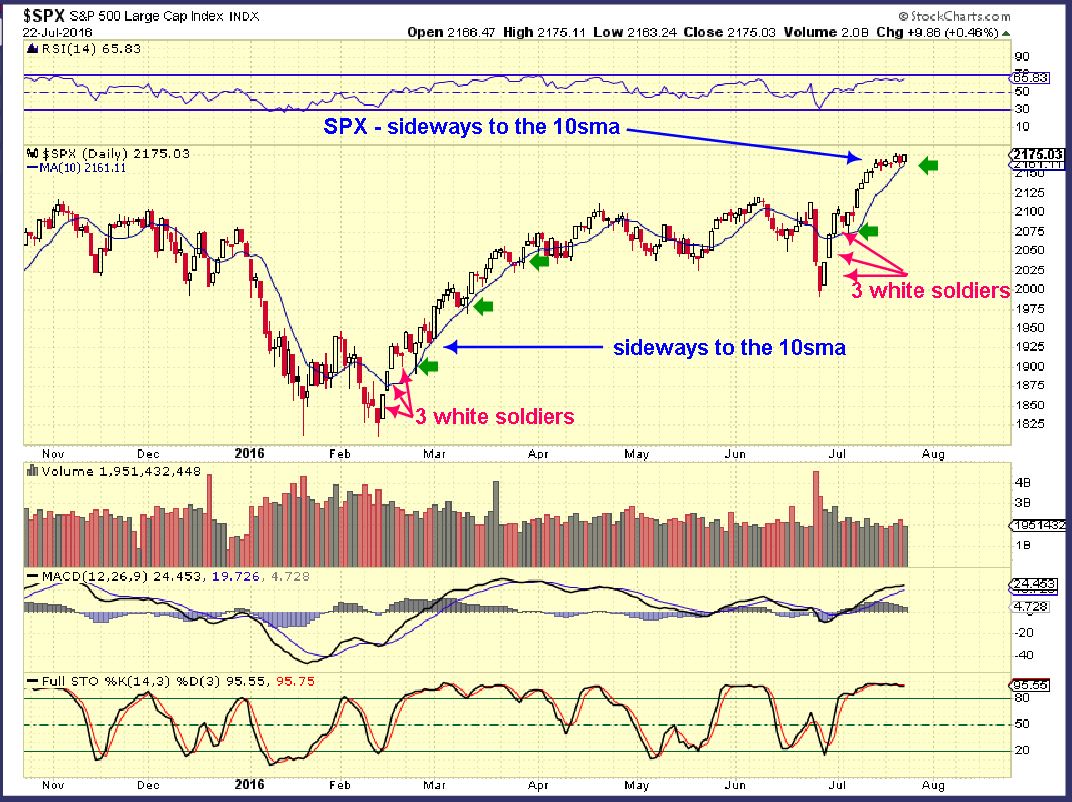
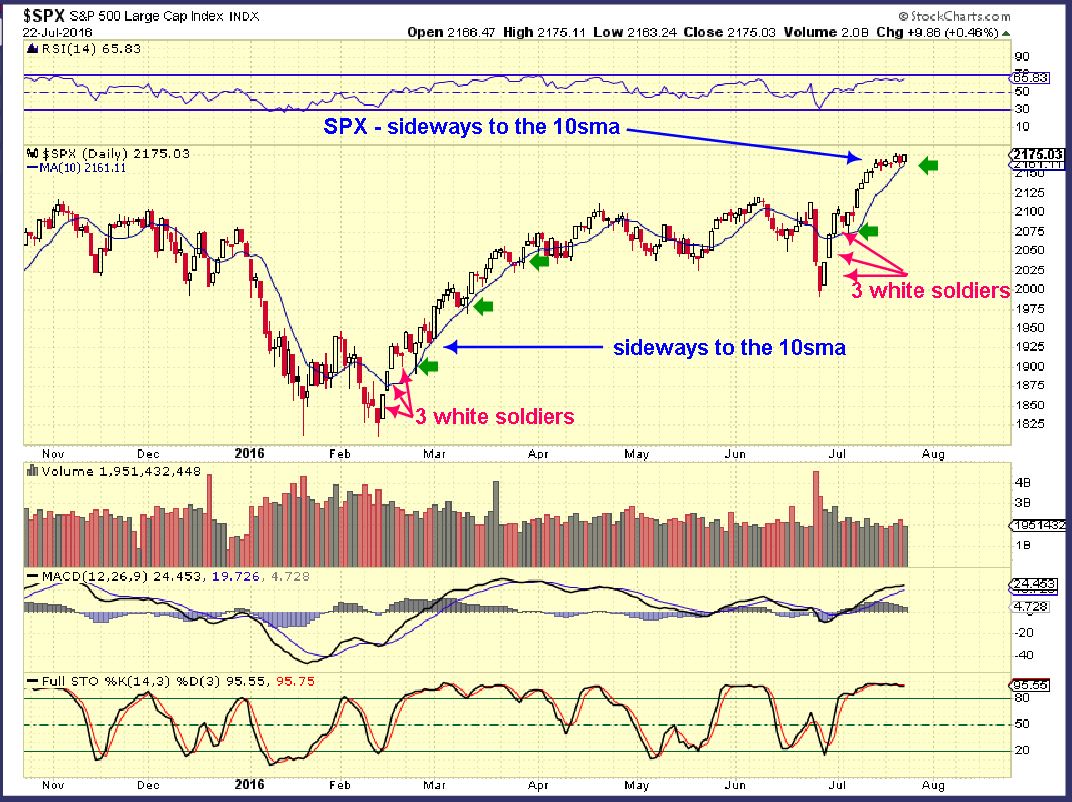
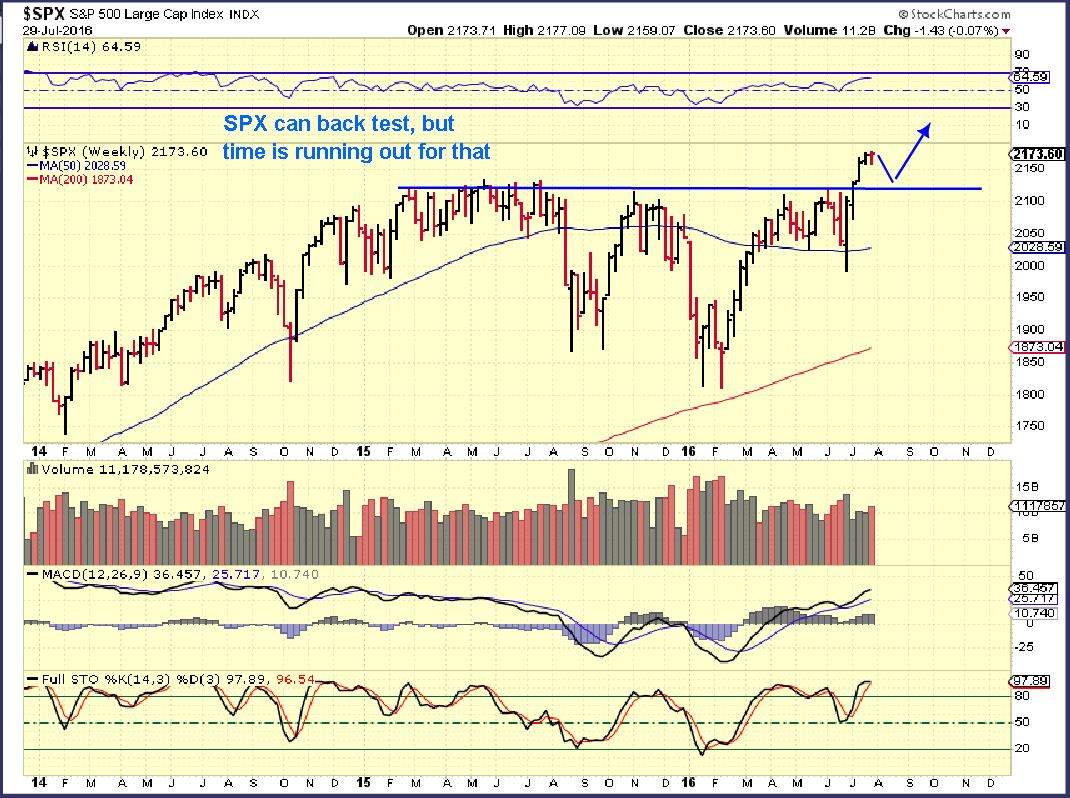
SPX - We've seen a break out to new all time highs and a sideways consolidation for weeks.

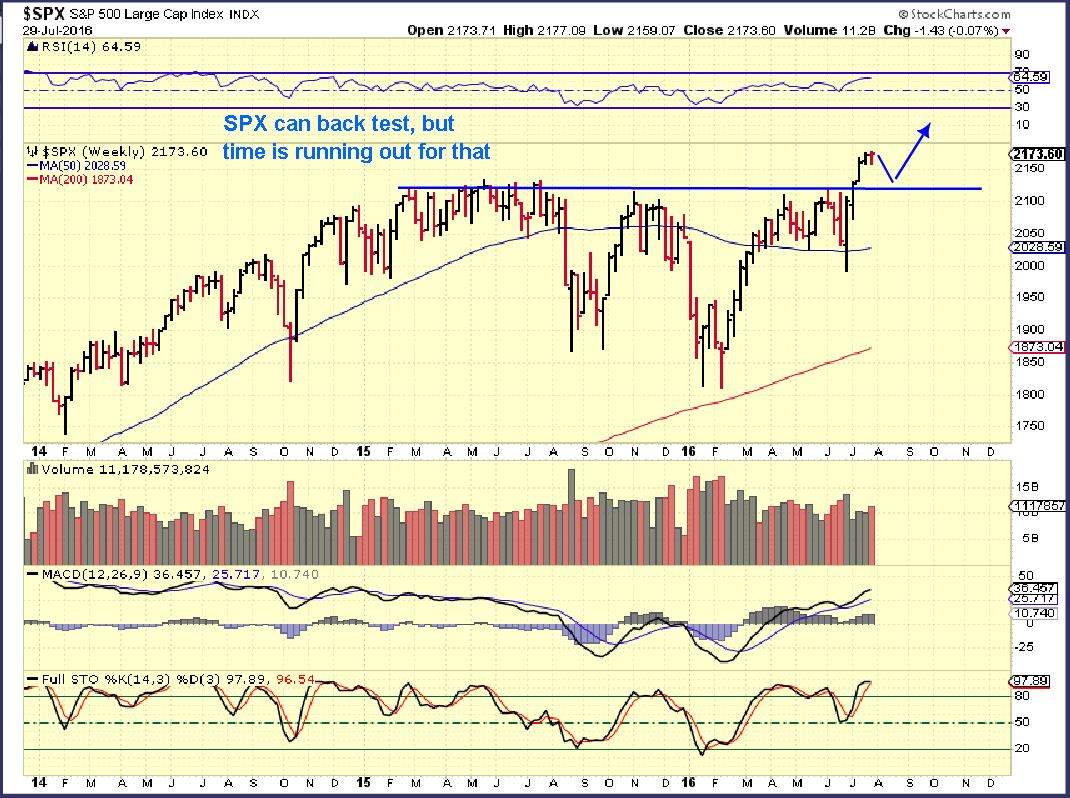
SPX WKLY - Possible back test or it may just break out higher. If it just keeps going sideways and dips down into a dcl, the back test could occur then too. We'll watch it as it plays out.
 Read More
Read MoreYes, I liked that picture so much that I decided to carry it forward to Friday. PLUS, I'm still waiting for the recent purchases to really run strongly 🙂 . Some of our stocks were green Thursday, even though Gold and the GDX sold off. Lets discuss our markets for a brief Friday report and then review Miners. This is the last trading day of the week, so there is not a lot of new things to say.
Read MoreHang on, They're running again!
.
I 'm going to skip the general markets and get right to Oil and Precious Metals. Why? This is a chart from yesterday, and again, nothing has changed.
 Read More
Read MoreWaiting on Fed Wednesday to see if there will be any special reaction is getting old 🙂
.
SPX - This was after Mondays trading, we could see a drop or just continue sideways.

Not much changed , huh?
 Read More
Read MoreSometimes what looks and feels like a big drop turns out to just be a small dip in the action. I think that we are seeing that in Gold and Miners now. We'll discuss that after a brief market review.
.
SPX - I've been expecting a small dip here, possibly back testing the break out after a measured move finishes. That may or may not happen. A sideways consolidation can also act as pause before continuing higher.

SPX - Holding the 10sma is bullish in a run out of the ICL. Temporarily breaking below it and recovering is fine too, I'm just pointing out the recent strength here.
 Read More
Read MoreI hope everyone is enjoying a nice relaxing weekend, lets review the markets and discuss our expectations for the coming week.
.
SPX - The break out that I expected after seeing the 3 white soldiers pattern is in play. Breaking to new all time highs get price above resistance, so a small sideways consolidation may be all that is needed before price continued higher. I expected a back test of the break out based on the VIX being below 12, so that still may happen.
SPX WEEKLY - I know someone that is trading ( holding) UPRO and TQQQ as a result of me pointing out the 3 white soldiers, and they are doing very well. Congrats! I didn't take that trade. The VIX is quite low at 12, leverage at this point may be a bit too much. Use caution.

Lets look at the NASDAQ...
Read MoreTonights report is going to be a great lesson on how we can view things as the markets ebb and flow , breathing in and out. We're at the end of the week and we saw a little selling in Precious metals Wednesday followed by an immediate reversal Thursday. Does that reversal mean that the selling is over? We will look at a number of things that help to give us confirmation as to whether a short term low is either in, or may not be in place yet. Also buying the dips tips.
.
WTIC - First a chart of oil, since many do ask about the energy sector that we were trading over a month ago. We had a reversal Wednesday, but I pointed out that I still see weakness going forward. Patience is needed here.

WTIC - That reversal vanished on Thursday. This needs to prove itself, and it is still proving to be weak.

Now on to Precious Metals...
Read MoreWednesday we saw the Miners (GDX, GDXJ) gap down and close near the lows on fairly high volume. What can we expect going forward? We'll discuss that after a quick market review.
.
SPX- The general markets broke to new highs and since there is no resistance here, they have just continued higher. I do expect a dip soon, maybe this measured move will be close enough?

3 reasons that I am expecting a dip...
Read MoreI want to FOCUS on a few things in this report
.
Read MoreNot a whole lot has changed since the weekend report, so lets just do a quick review and then discuss our expectations.
.
SPX - As expected
 Read More
Read More
Scroll to top

 Read More
Read More