The Gold Bull Market
Do you think the Gold Bull Market has returned? Obviously I do, and have been trading as if the Gold Bull Market has returned. You need to be aware of this opportunity and appreciate that another big move in this Gold Bull Market is again developing. If this next move is anything like the moves seen during past Gold Bull Market's, then you will not want to miss the next buying entry after this current correction winds down.
I was able to successfully guide Chart Freak members through the recent 100% rally in gold miners when we bought the lows back in the middle of January. Those gains were exceptional, to say the least. In some cases, junior miners rose up by 500% off the lows, and are now consolidating those gains in preparation for the next leg higher.
My recent weekend report (
premium version) took a deeper look at Gold's recent correction and how the current action in the US Dollar may impact the precious metals market. However, it is again time to start paying closer attention to the Precious Metals markets, because after-all this is a Gold Bull Market. Let me take you through some of the premium content I shared recently and review what I believe is occurring.
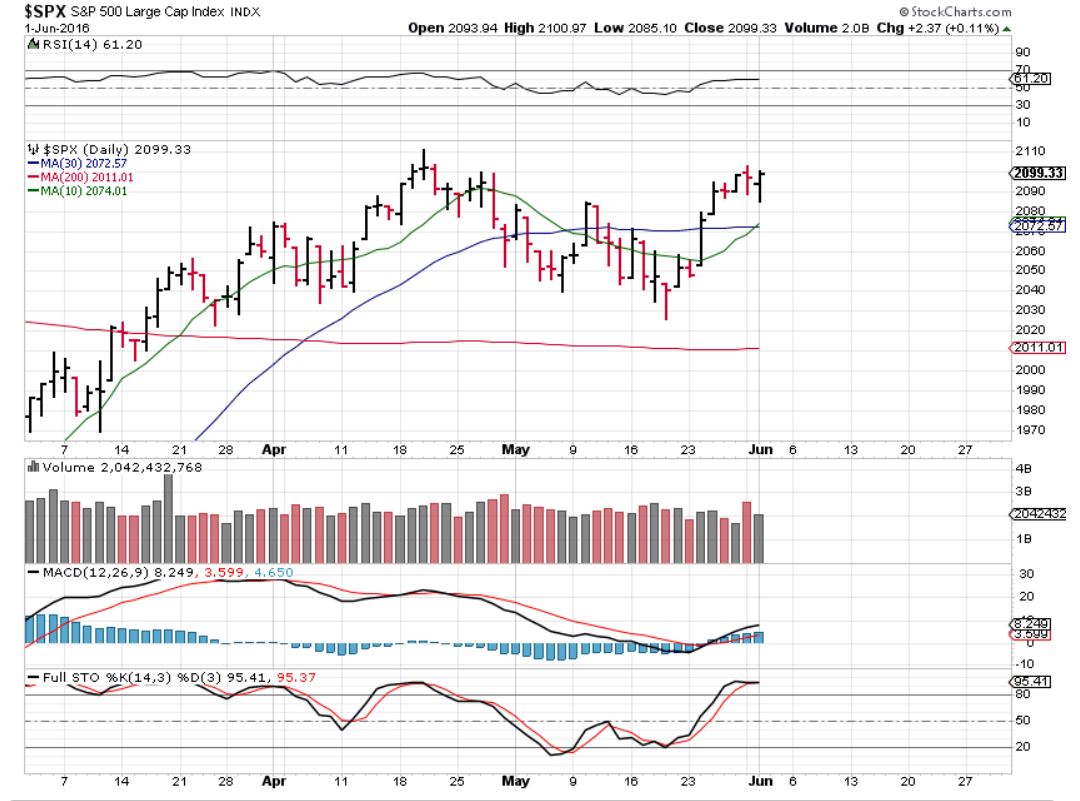
Gold Weekly
Gold has finally started that correction, as seen on this weekly chart.
 Read More
Read More