Your past steps have moved you to where you are today, your next steps are just as important. Allow me to walk you through a look at what Chartfreak readers were hearing before & after the Brexit vote. Those steps brought us to where we are now. I’ll also show what we currently see when it comes to Precious Metals.
.
GOLD AND HOW I SEE IT NOW

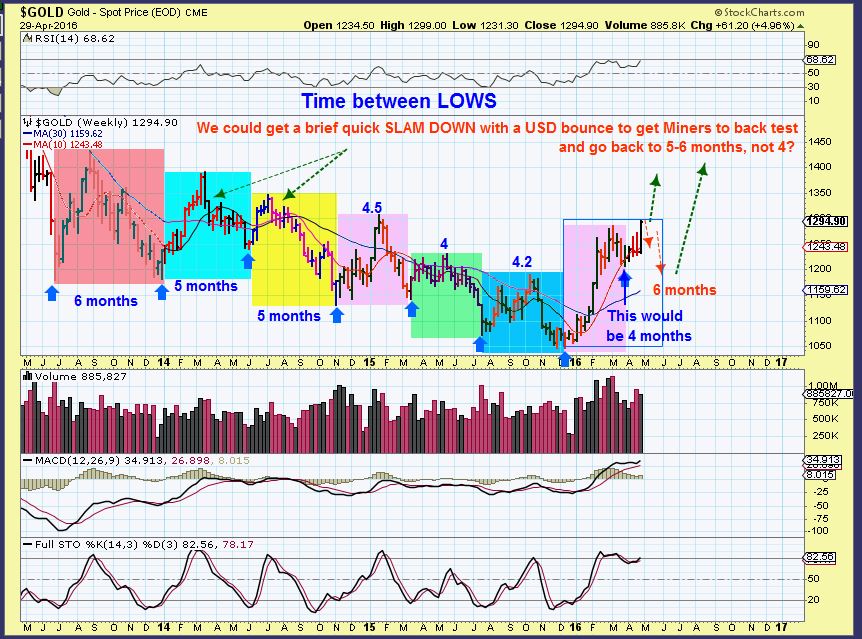
I kept reading everywhere in Late April / Early May that Gold had to plunge down and tag the 200sma before it could move higher. Why? Many thought that Gold was overextended. I agreed that it could, but I also pointed out that Cycle Timing caused me to be looking for a very important low imminently. I drew a drop to $1200 area, but mentioned that $1170 was possible too.
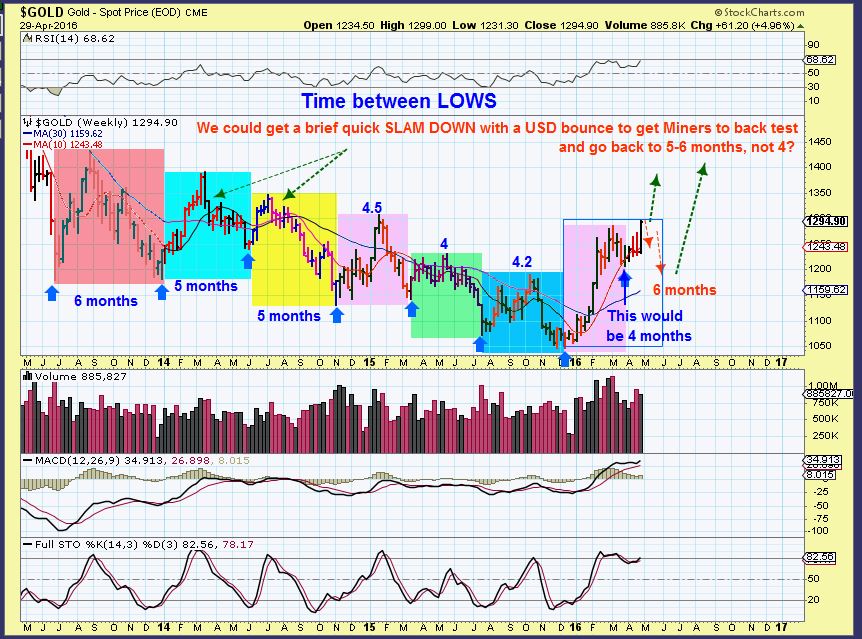
As we dropped to the $1200 area , Fib #’s and ‘ Cycle Timing’ came into play. I was looking for a low.

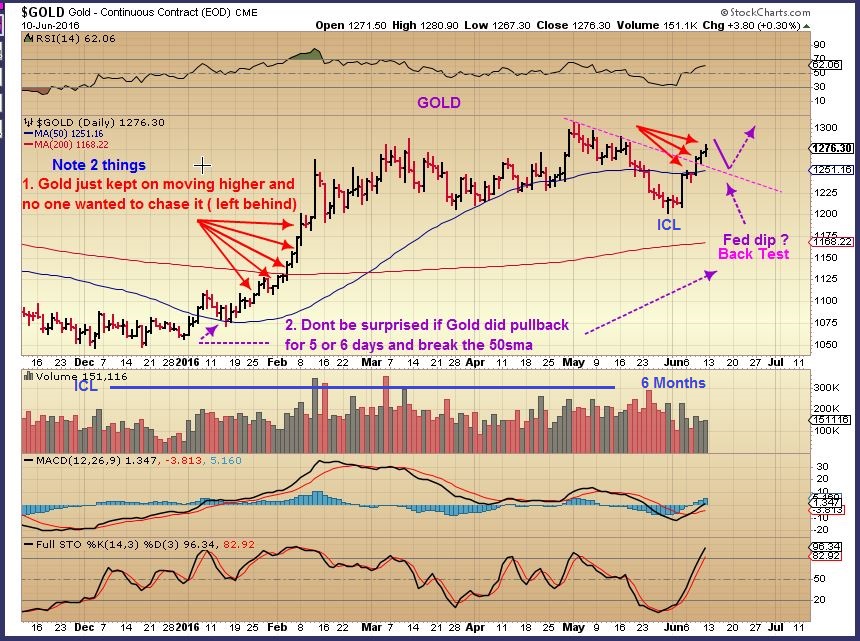
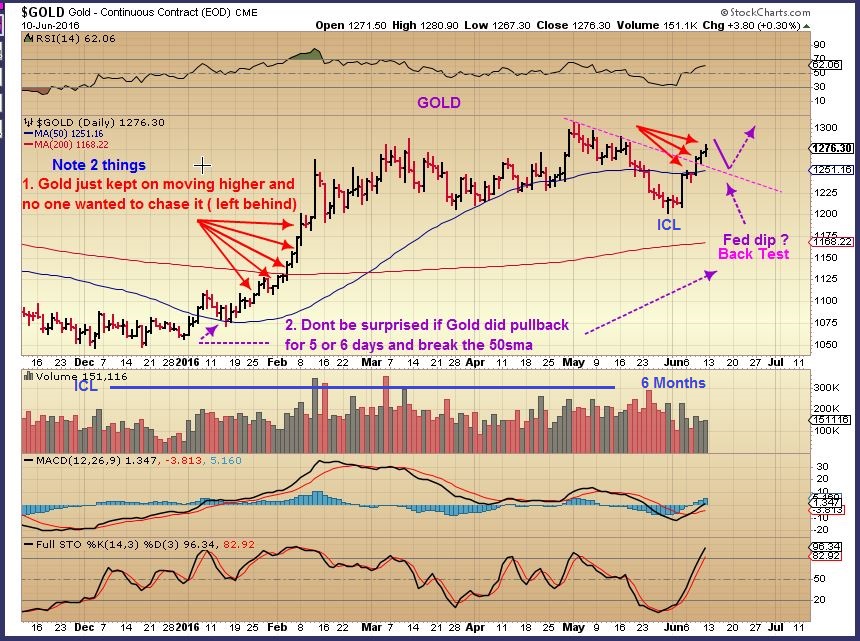
I then called a possible low at the $1205 area with capitulation type selling scaring everyone away and causing a lot of ‘fear’ talk. I mentioned that I couldn’t tell for sure, but I think that the lows were in or at least a buy-able bounce with that reversal. I began buying Miners 4 weeks ago, at the end of May.

This was day 3 of the lows, and an extremely low jobs report was released. Gold blasted off higher. A close above the blue line would confirm my idea of deep meaningful lows ( An ICL).

I was asked in an email, “What about all those saying that the 200sma needed to be tagged?” I agreed that that ‘tag’ could come, but did it have to be in May? I said No, and drew this idea.nThe Tag could come later and when the 200sma is actually higher.

Gold was now a bullish set up and was running out from an ICL. We actually had a consolidation from FEB to June, for those thinking that Gold was overextended. It isn’t, it had gone sideways for months.
Silver stocks have doubled and tripled, is the move in Silver & silver stocks done? This is a great looking base if you ask me, and only the beginning in the long run.

And GDX & GDXJ have had great runs higher too, but that may be just the beginning.

Timing a trade is important though. Now I want to walk you through a few trades, and show you a current trade that I think will play out well.
.
I recommended VGZ and MUX before they exploded higher. I didn’t offer an exact entry or exit, just that I had bought them a bit earlier and they were looking at a possible explosive set up.
MUX – I had mentioned to my readers that I had been buying Miners and bought MUX in May at the 50sma near $2.25. June 12 it was now breaking out from a constructive consolidation with great volume. Even at this point it was a buy-able break out.

MUX popped and ran very strongly. It remains near $3.75 consolidating recent gains.

JUNE 13th – VGZ was at $0.97 . I bought this consolidation and mentioned that I thought Golds ICL was in, Miners should be bought. Dont go ‘all in’, but it was a great trade set up as shown. It had a super base.

VGZ at $2.02. Gains of over 100% in 2 weeks.

That leads me to today. When those positions get extended, I like to sell at least 1/2 and look for other similar set ups. I pointed out this stock Monday and even with fundamentals that are not ideal- the set up is perfect again.
.
June 27 XRA– This has had a nice run higher and has consolidated. I bought it near the 50sma and posted this chart as a buy above support. Another 97 cent stock 🙂

XRA – It wasn’t just the recent consolidation and set up that I liked, I also pointed out that another super base adds relevance. Does this base look a bit like the chart that follows it to you?

VGZ as it broke out and ran to $2+

Tuesday June 28 – So again, I had already posted XRA, but I posted it again in todays report. This is an explosive looking set up, even if one just took it for a quick trade on a possible break out.

XRA June 29 as I write this report, XRA is up another 13% today. Actually , it just popped up 20% as I was writing.

THM – I pointed out another one just like it Monday at 75 cents, what a nice set up. Watch these run.

Boom –

I am constantly searching for what I know to be explosive set ups in the bullish market sectors, Right now I am bullish on Precious metals and the set ups look very nice.
So did you buy VGZ, MUX, ASM before they broke out? Are you in XRA today? Not every trade works out with 20% gains day after day, but these recent gains are seriously helpful to the portfolio. For example, I also recommended SAND & BTG over the past 2 weeks and with small gains, SAND backed up yesterday on a public offering. Not a big deal, down 7% and I am actually still bullish on SAND, but I just wanted to point out that not every great set up works right away. A small position in the ones that do make up for any that do not however. Honestly, other miners recommended are doing well too, and still others are currently ‘setting up’ for possible future explosive moves.
I will keep premium members posted when I see these bullish set ups. I do see a few more currently acting correctly. Why not get an extra set of eyes by trying chartfreak for a month? One trade may pay for that month. Thanks for reading along, and best wishes!
.
CLICK HERE AND SCROLL DOWN TO SIGN UP
.
~ALEX


 .
.