Archive for month: May, 2016
https://chartfreak.com/wp-content/uploads/sites/18/2016/05/TRUST.jpg
518
898
Alex - Chart Freak
https://www.chartfreak.com/wp-content/uploads/sites/18/2019/11/Chart-Freak-site-logo.png
Alex - Chart Freak2016-05-28 15:51:132016-05-28 16:18:06Trust IssuesNot much has changed from Thursdays report. Janet Yellen speaks today and she possibly could shake things up with some dovish or hawkish talk, so we'll see how that goes. And then all then traders in the U.S. will have a 3 day weekend to think about it. 
.
If you are heavily invested and you'd rather not think about it on your weekend off, you may want to lighten up.
Read MoreYesterdays report discussed some break outs that were taking place in various sectors. Wednesday, we saw some follow through in those areas too. Just like a baseball player at the plate, when we get a decent pitch tossed our way, we also need to follow through to be able to possibly score. Some may wait for a pullback or start a small position and add on a pullback later, since it is early in some set ups. Lets review.
.
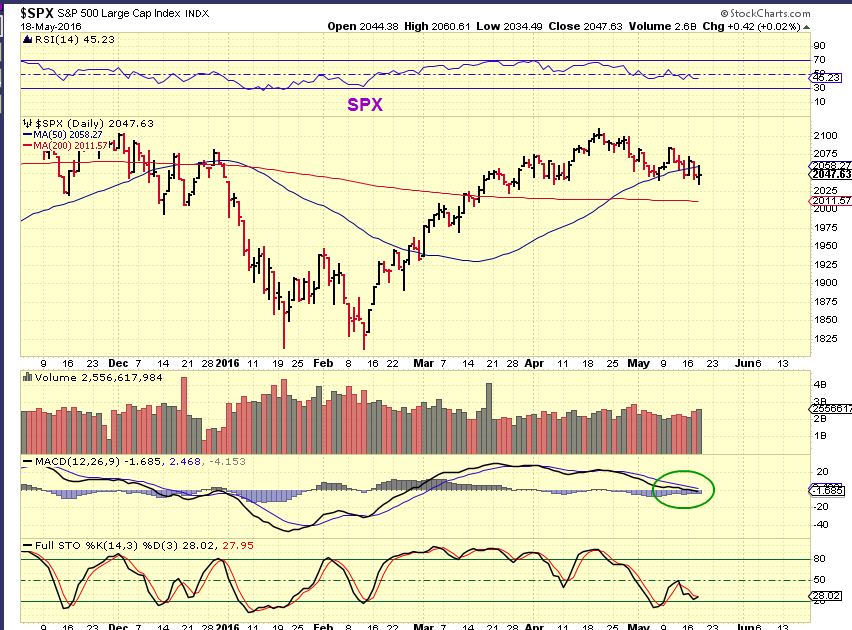
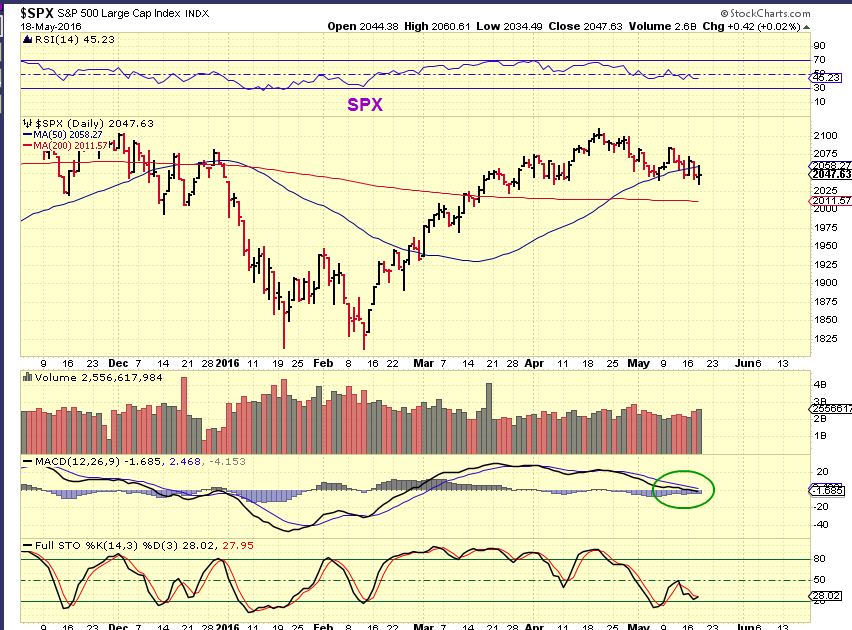
SPX - This is the follow through that we expected. We are only on Day 5 today, of a daily cycle that can last over 30 days.
 Read More
Read More
Market Turning Points And Trading
In a recent premium report, I reviewed interesting Market turning points that are showing up across various sectors. I'd like to share some of that with you now. Please note that most of this information was released in the weekend report of May 21st or within previous reports.
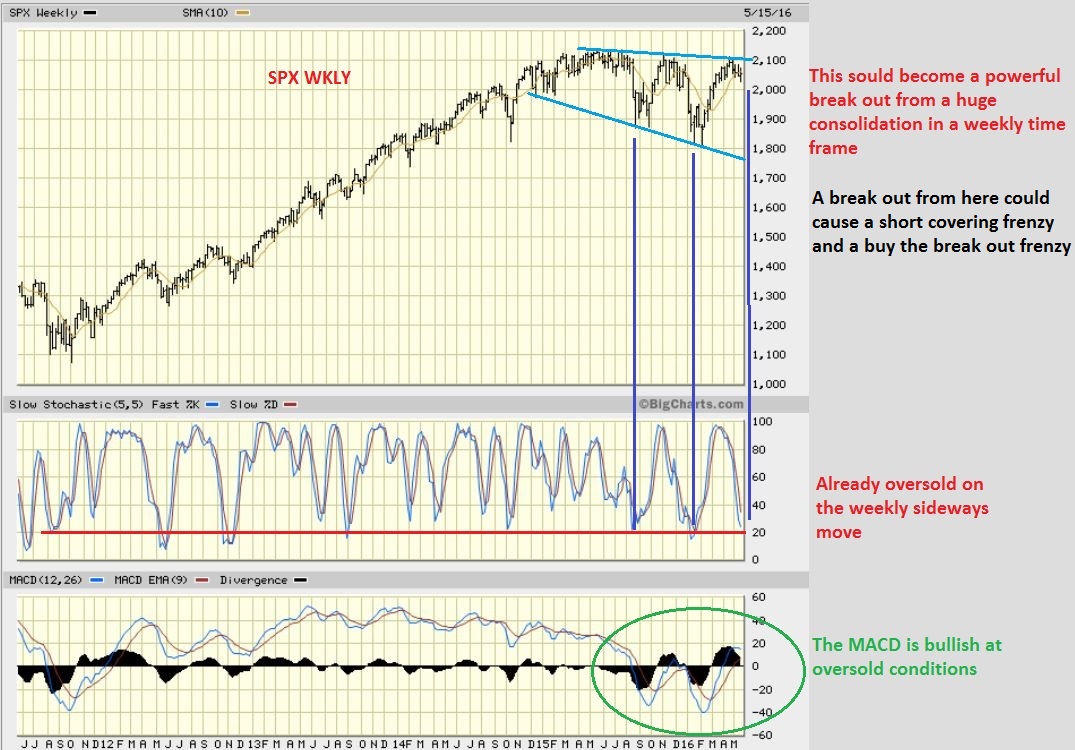
S&P 500 - SPX - We see a mild pullback in the General Markets after a strong rally. Not even a 38.2% retrace yet. Many advisors were becoming very bearish and pointing to a possible H&S pattern, with a big drop to come. I see that H&S pattern, but they often fail, as I was more focused on a few other areas that indicated the markets were going to break out higher, not lower.
 Read More
Read More Tuesday was a Break Through in a several ways. Let's take a look.
.
SPX - From the weekend report. For many reasons, we were waiting for a break out higher ( not lower like many other analysts).
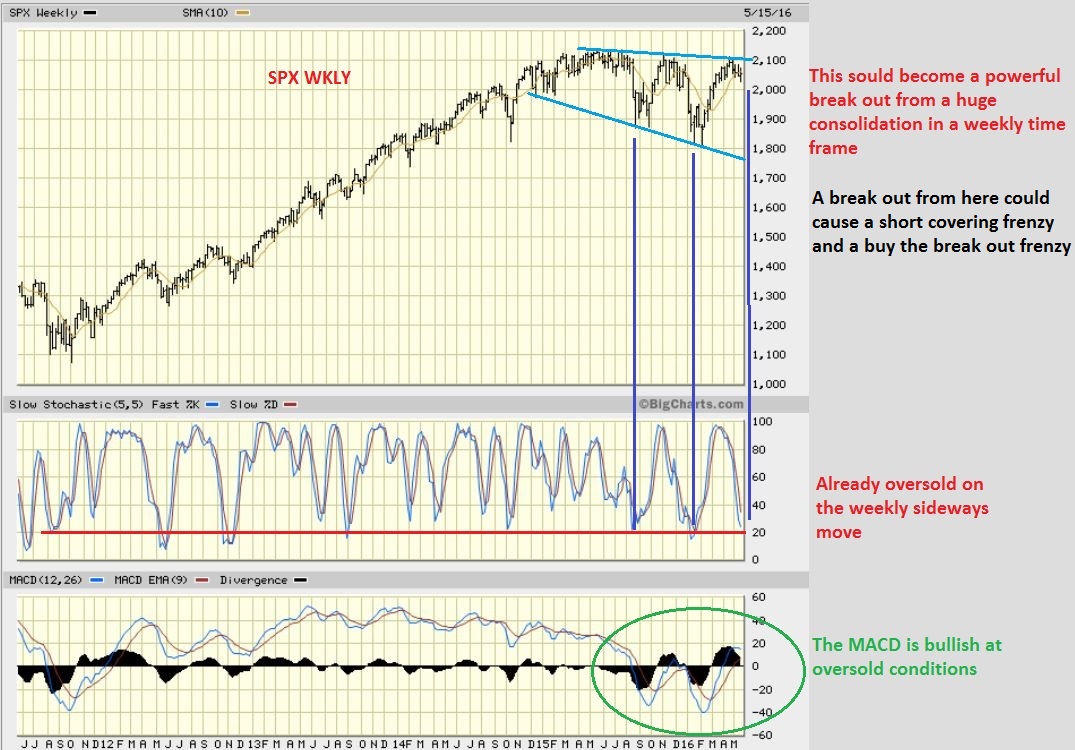
SPX Tuesday- We see a Break through. This is Bullish. Today is only day 3 of the 2nd daily cycle, following a R.T. Daily cycle. That means that we could really see this move higher over time. Picture this : Many were shorting what appeared to be a H&S, and they may now start covering and cause a buying reaction.

And the NASDAQ?
Read MoreWe didn't really see a whole lot of change on Monday, but as mentioned in the weekend report, some areas could be setting up. Some setting up for a run higher, others setting up for a fall. To the charts...
.
SPX - No follow through yet, but I am expecting higher prices soon.
 Read More
Read MoreIn this weekend report, I want to review the markets as usual and discuss where they are at. Things look very interesting in many ways. I also wanted to discuss a few things about my personal view of trading around cycles. In my analysis, many are aware that I incorporate a variety of helpful techniques. I Mainly use various forms of Technical analysis, and along with that I add Cycles, Sentiment, a little Elliot Wave and so on. In this weekend report, I want to also briefly discuss a few things regarding Cycles and some of the trading that goes on around them. To the charts...
.
SPX - As mentioned in a prior report, for the amount of time that the SPX has rallied out of lows and moved to oversold, it has had a mild pullback. Not even a 38.2% retrace yet.
 Read More
Read MoreLets do a market review and then I'll discuss what will be in the weekend report.
.
SPX - We've been looking at what looks like a H&S. EVERYONE is looking at it and the group think is seldom correct, so I have to wonder if it'll play out. The reversal could be a DCL and may be setting up for a rally back to 2100.
 Read More
Read MoreWednesdays release of the Fed Minutes certainly caused a 'reaction' in the various sectors of the markets. It falls in place with the timing of certain cycles, so lets review the action and what it may mean moving forward.
.
SPX - The General Markets sold off with the Fed minutes. They recovered into the close. This still looks like a H&S and has yet to recover the 50sma.
Something that I find very interesting happened on Wednesday, I'll discuss it later in the report.
Read MoreFOMC MINUTES RELEASED TODAY, that can affect the markets , since they seem to be at pivotal points. I have a lot to discuss for a Wednesday, so lets get right into the report...
.
DJIA- I usually use the SPX, but they are similar right now. POssibly dropping to the 200sma, but 'time' is important here. It really needs to move higher sooner than later cycle -wise.
 Read More
Read More
Scroll to top

 Read More
Read More