Archive for month: February, 2016
Public Report – Bull Flags
/53 Comments/in Public /by Alex - Chart FreakI wrote a report about Bull Flags for the premium members last night. Why? Questions have been raised.
.
On Feb 17th, after the recent run up in Gold, I mentioned that Gold could Pause and form a Bull Flag. These are often just a pause along the way (although they can fail).
Feb 17 - I discussed a possible Bull Flag forming after a strong run higher.

Feb 24 - We have the Flag and as mentioned, it is often just a pause before continuing to run higher.

Well on Friday Feb 24 Gold broke out and dropped. Many said Gold failed at the Bull Flag. Friday Feb 26 ( Today) Gold dropped down to $1212. Does that hurt the Bull Flag and prove it is a failure, like some are saying?
No- Let me show you 2 ideas that are not a stretch or grasping for straws. These are legitimate patterns playing out .
Read MoreIs That A Bull Flag?
/88 Comments/in Premium /by Alex - Chart FreakOn Feb 17th, after the recent run up in Gold, I mentioned that it could Pause and form a Bull Flag. These are often just a pause along the way (although they can fail). So lets discuss the last few days and discuss Golds Bull Flag and other important implications that I am seeing.
.Feb 17 - I discussed a possible Bull Flag forming after a strong run higher.

Feb 24, We have the Flag and it is often just a pause before continuing to run higher.

Then I started seeing similar bullish formations in various Miners, like TGD. This is an ascending wedge or ascending triangle, and usually plays out in a bullish break higher too. Hmmm.

Lets discuss chart patterns and look at some more Miners...
Read MoreQuite A Ride
/84 Comments/in Premium /by Alex - Chart FreakThere were reversals all over the place yesterday. From the Market sell off and Oil reversing higher, to Gold and The Miners breaking out only to turn lower. What can we expect going forward?
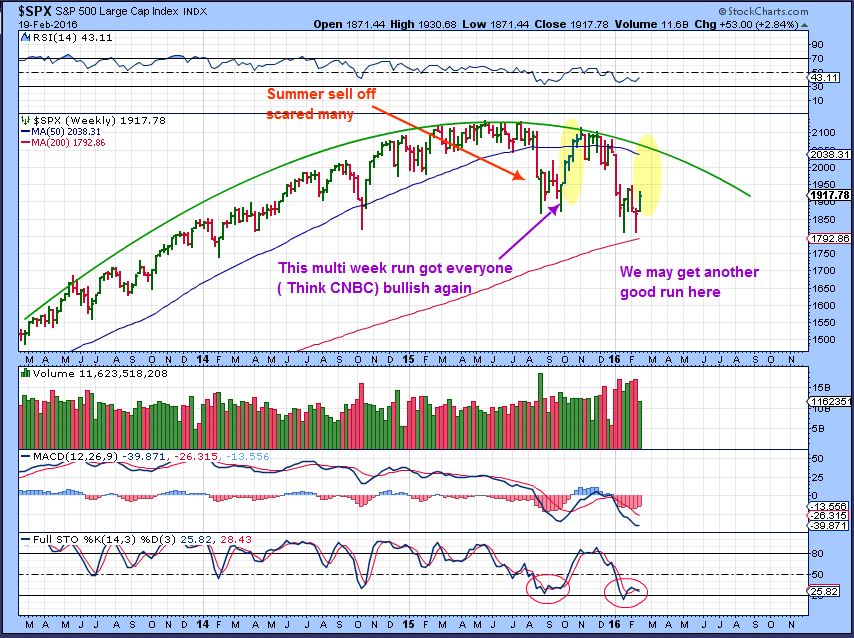
.SPX - Volatility has produced many reversal here at the lows, but I think they were just clearing everyone out before a run higher.

In an earlier report, I pointed out this possibility, and we see it playing out...
Read MoreBuy Sell Or Hold
/82 Comments/in Premium /by Alex - Chart FreakI've been expecting a multi week rally in the markets since Feb 11, and so far it is pretty lack luster. I noticed weakness in the SPX on Monday and mentioned that I thought this would cause the 'rally' to stall.
I posted this chart, read the writing.

The SPX was rejected at the 50 sma.
 Read More
Read MorePublic Post – A Trading Paradise In Metals And Miners
/39 Comments/in Public /by Alex - Chart FreakAre you basking in the Traders paradise? At Chartfreak, trading has been good in Precious metals and Commodities. Lets take a look at a few of our expectations going forward and review some trade set ups that are still working out favorably.
.
SPX WKLY – After warning that there were signs of another sell off coming in November,I have recently been expecting a rally to draw the bulls back in. I expect that we could see a repeat of the run up last September, as highlighted.
OIL REVIEW
Back on November 13 , I had a $26.09 Target for Oil on a weekly chart. I also pointed out a $24 target later , if the selling reached extremes.
Last week the XLE didn’t make new lows, but Oil did, dropping to $26.05. That along with cycle timing caused me to look for Oil to possibly see a temporary bottom here.
I used these charts in my February reports.
Oil gapped up recently , so I drew my expectation of a gap fill and a tag of trend line. Then the move higher.
We got a perfect tag of the trend line. I still believe that Oil may be finding a bottom unless this trend line breaks?
Notice that Some Oil Stocks bottomed last summer, well before Oil.
.
GOLD SILVER & MINERS
GOLD– We caught the strong run up in Gold and Miners right from the shake out lows in GDX. On Feb 17 I thought that a FLAG could form to consolidate recent gains, while individual Miners may still rally or play catch up, so I presented this idea and a few alternative ideas as well.
You can see that the Bull flag is almost complete.
SILVER – Silver never broke out, so it may do that this week or it may just continue to consolidate.
I definitely believe that we may be seeing the next phase of the Bull Market in Precious metals starting, as we surge out of the lows. Nothing goes straight up though, so lets also discuss what an eventual pull back could look like, as it may present another buying opportunity.
.
This is one that would shake many people up. I don’t think that it is the most likely path, but it needs to be viewed to prepare us for any possibility.
These 2 charts were in my last public report. I favor these views.
#1
#2
.
What about this Traders Paradise? Past public reports have pointed out some of our trades in Miners and commodities. Lets review a couple more here.
.
SWC – This stock was pushing on the 50sma and was a good set up last week.
SWC – SWN has broken out after reporting earnings. I expect higher prices.
MUX – We recommended a 2nd buy on Jan 26 at $1.17
MUX – today it is at $1.75. If Miners pull back in a significant way, I can see a test of the 50sma as possible.
ABX – $ 7.65 inverse H&S with good volume pops.
ABX currently at $13.42. This may just form a handle, before another strong mive higher.
.
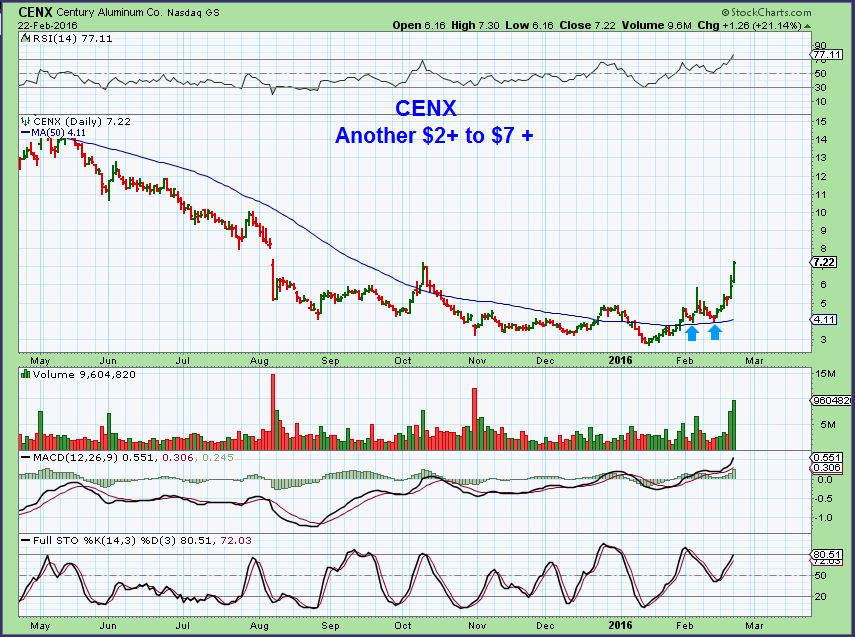
Here is some good news too. Some of the commodity stocks presented in past reports as ‘trade set ups’ now appear to be breaking from their bases and could have great upside potential for the long term.
.
CENX – Feb 3, nice long base with a shake out, ran and pulled back to $4 at the 8 ema.
CENX Has moved from $2.63 to above $7. A pullback may be another buying opportunity. Look back at how ABX and NEM ran from their long bases.
.
FCX was mentioned as bottoming near $4, and then a 2nd buy was at $6 as it broke above the 50sma. FCX is near $8 today. This also may be bought on the dips if it remains healthy.
.
Feb 3 – VALE at $2.32 , this was a low risk entry, since your stop would be placed below the lows. Price is now trading above that blue triangle.
.
X Daily– Notice that US STEEL is forming a multi month base with divergence. This has a lot of upside potential if it recovers from here.
Recent reports featured AA, AKS, STLD, TCK, VALE, FCX , etc., and most of them now look like bases that may become longer term bottoms.
.
I’ve been discussing the possibility of the Equity Markets topping and the Bull returning in Precious Metals and Commodities for a while now. Many public reports have been posted at Chartfreak.com to highlight these events. I liken it to a large freighter ship turning around in the ocean. They can’t turn on a dime, but gradually they will reverse course and head in the other direction. Is that what we are seeing here in the markets today? Many Miners and commodity stocks look to have built their bases, and they could even become buy & hold investments longer term if conditions remain this way. Why not join us as we continue to monitor the situation? Chartfreak.com
.
~ALEX
Wash Rinse Repeat
/71 Comments/in Premium /by Alex - Chart FreakWell, I had a weekend report with 32 charts and not much has changed in one trading day, so lets do a little review and then look at some trade set ups.
.Last week we saw a healthy set up for a move higher

This week...
Read MoreRockets
/34 Comments/in Premium /by Alex - Chart FreakWe have been on a rocket ship ride for a month now in Gold & Miners. Whenever someone posts a "Rocket" as a headline picture in their report, we usually immediately get a pullback. I'm ready, so I thought that I would give it a try 🙂
.This is the rocket (this was my chart from Feb 16).

We will discuss Precious Metals in a moment, but first lets do a complete review starting with the SPX...
Read MoreStill Climbing
/35 Comments/in Premium /by Alex - Chart FreakPrecious metals and especially individual miners keep climbing higher. Wave after wave, the dust buyers and shorts are getting hammered. This wasn't entirely unexpected, that is why I mentioned taking some profits and letting partial positions ride. This runaway , melting upward type of move can be rewarding, but cycle wise, it is will pause or pull back soon. We'll discuss that. The markets were moving up off of their lows too, but they stalled on Thursday. Oil turned back down too. To the charts...
'It's Friday, so there isnt much to say with only 1 trading day left, but lets take a look and see what we can learn.
This was 1 of my 2 Gold charts from Thursday mornings report. Gold actually hit $1240 as the day went on, so it looks like that flag pattern could form. While it does look like that Flag pattern could form, I actually think we may see something else too.

Let me show you what I think is happening now...
Read MorePublic Post – OIL & GOLD
/in Public /by Alex - Chart FreakI'm going to share a portion of the premium report from Tuesday. We had been invested in Miners from the shake out lows, but most of what was bought has had a spectacular run higher. Now that there could be a consolidation phase in precious metals, does anything else look interesting? Have you seen VALE, FCX, CENX, etc? Commodities are making some nice steady gains. I'm also looking at The Energy Sector among other things. From Tuesdays report...
I think OIL is putting in lows (temporary or permanent remains to be seen). Lets discuss a few ideas as to why I think we are at lows in Oil.
.On November 13th , I said that my OIL WKLY target was $26.09

Did we hit $26.09?
Read MoreContact Us
26 Broadway,
8th Floor
New York, NY 10004
admin@bigleaguefinance.com
admin@bigleaguefinance.com
Latest Blog Posts
accelerator diet pills goji berry diet pills ultra 90 diet pills keto meal replacement bar top weight loss diet pills for thyroid patients where to buy t lite diet pills keto friendly thickener diet fuel diet pills peanuts keto friendly rite aid diet pills that work envy diet pills diet pills for breastfeeding moms belique diet pills perfect slim weight loss pills calories in a bottle of white wine