Archive for month: January, 2016
We are getting the follow through that we expected in many different areas of the Market. The small pieces of the big picture continue to add up. Will it continue? Lets check the charts! 🙂
SPX Jan 27 - I pointed out that the drop mid week was normal, the same thing happened coming out of the August lows. I still expected a run higher.

SPX Jan 29 - Friday we got our follow through.

Moves higher out of the lows can be convincing, but will it lead to a break to new highs in a bull market, or a bounce?
Read MoreI wasn't planning on a Friday report, but Thursdays action in several areas was important enough that I wanted to share a few charts. Also a reader ( we shall call him D.F.), pointed out an area of interest that I will touch on here too.
.
Lets start with the USD. I saw weakness and have been saying that I expect it to drop. I posted these charts last week.


We have been in Gold & Miners for a while now, but a weak dollar could help Precious Metals and Commodities further. I will cover this more in the weekend report , but for now, what did the Dollar do Thursday?
Read MoreThe markets are always dancing around on a Fed Wednesday, and often the volatility spills over into Thursday. Lets take a look at the charts and see what we can see.
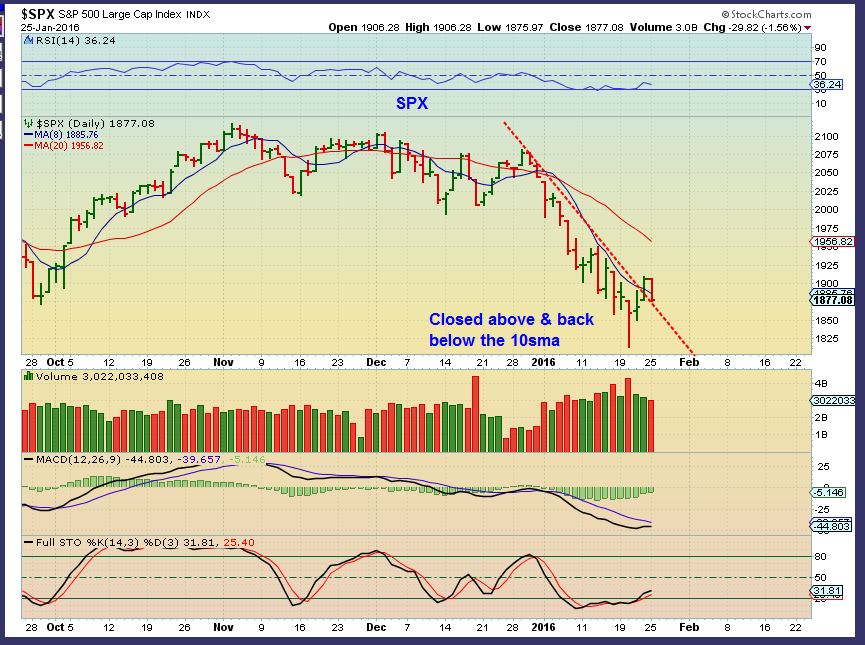
SPX - The markets sold off after the Fed Decision. I called for lows recently and I still expect higher prices to develop from a bounce. You can see that this is how the markets moved coming out of the lows in August too. I do not expect the recent lows to be broken, but a little more downside is not out of the question. Please notice how difficult it would have been to trade the Lows in August/ September.

That being said, the RUT / IWM looks like a bear flag, so lets look at a few other areas.
Lets look at the NASDAQ...
Read MoreSo lets just pretend that today is just a Wednesday like any other Wednesday. Things are playing out exactly as expected. To the charts!
.
SPX Monday - I called the reversal last week a trade-able low, and the Quick sell off Monday just a back test of the trend line.
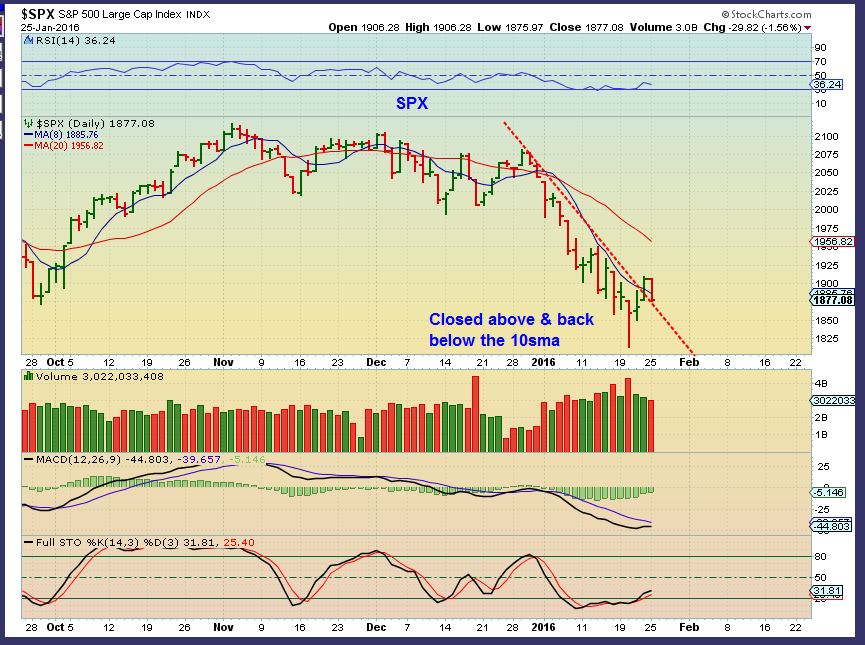
SPX TUESDAY - It's only day 4 , so I expect this run higher to continue.
 Read More
Read MoreMonday saw a little drag on various sectors of the market, but I still expect a bounce before another wave of strong selling resumes. WEDNESDAY is a FED day, so anything can happen, but Cycle timing is right for bounce.
The old saying is that a picture is worth 1000 words, and sometimes I see a chart that's worth a thousand words too. The Banking index, for example , says a lot.
.
This is the Banking Index

The above chart is quite oversold, but it is also quite unhealthy looking...
Read MoreHere at Chartfreak , we've been looking at the short term moves for traders that are likely to occur as well as The Big Picture that may be changing. I expected changes, and that is what we have seen developing already in 2016. The weekend report had over 30 charts, so I thought that I would share a couple here with the public readers.
.
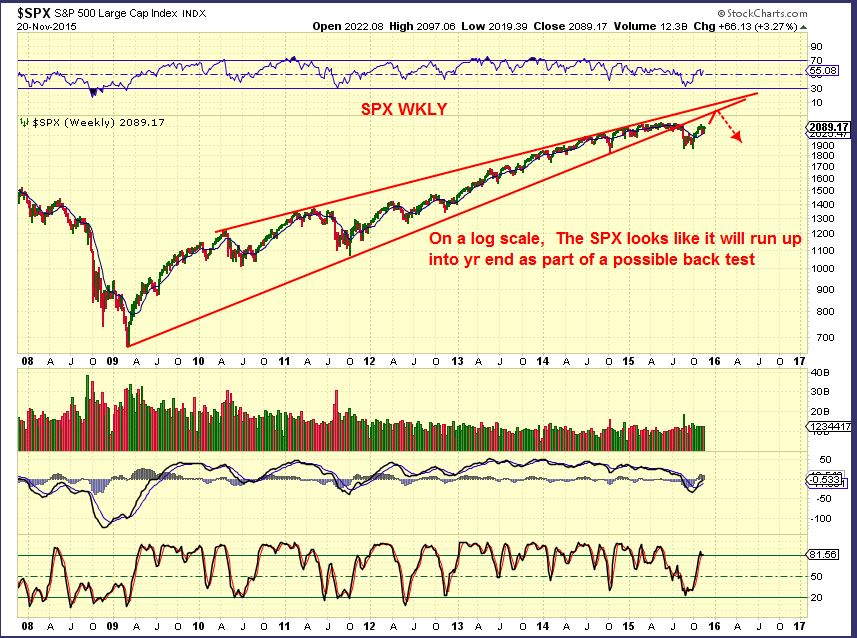
SPX QUARTERLY - They say that a picture is worth 1000 words. This speaks volumes if things dont change in a big way.

Lets look at a few other areas...
Read MoreThe weekend report will discuss the changes that we have expected for months, and how we now see those changes taking place. Also, as mentioned in the last report, the recent sell off is now changing into a Long position, but for how long? To the charts! 🙂
.
SPX - On Thursday, Jan 21st I mentioned that a swing low was in place ( Bullish for going long). It is safer to wait for follow through with a confirmation break above the 9 sma.

SPX - We had that confirmation on Friday. For traders, going long SSO, TQQQ,IWM, and various stocks was in place.

But please, lets not forget the Big picture too...
Read MoreJust a Quick market review and then I want to discuss some fast trades for those that like to trade, but aren't ready to buy & hold quite yet.
.
SPX - I discussed the reversal and likelihood of that low to be in place for a bounce / rally. Thursday did put a swing low in place and the timing is right for a low. We do not have a break above the 10sma as confirmation yet , so the safer trade lies ahead, but some may have wanted to buy the swing based on timing, and place a stop below the Wed lows.

SSO, TQQQ, etc can be traded coming out of the lows, with a stop just below recent lows.
Read MoreThe Dow Jones Industrial Average was down over 550 points yesterday and then rallied back into the end of the day, putting a form of reversal candle in place. Thursday morning the futures are RED, but we are at an extreme point that calls for a bounce/ rally. Yes it could last for days and weeks, but is the selling over? Lets review the markets and some stocks.
.
The SPX put in a large reversal candle too, after breaking below the August lows. 1730 is a normal downside target, but I think we rally first. It should be easy to get a swing low. A move above yesterdays highs begins the process.

What do I expect from this move higher after it starts?
Read More
Scroll to top