Archive for month: September, 2015
As mentioned in last nights report, we saw an explosive move in Commodities yesterday one day before the Fed Decision. That caught a lot of people who were not in front of their screens flatfooted. Last nights report also pointed out that it looks as though what we have been expecting to occur during the Fed Speech is beginning to play out. Lets go shopping and see if we can find some low risk entries developing in OIL and Precious Metals.
Lets re-visit WG. Rather low priced, I recommended this beaten down Energy stock here at $0.80 and $1.00 in early Sept.

It Popped and ran to $1.80 rapidly and now has formed a bull flag type pattern, landing on the 10sma. You could buy this with a stop under the 10sma as a low risk entry.

Lets keep shopping...
Read MoreEarlier this week I certainly thought that the markets were waiting for the Fed Decision on Thursday before making any big moves. Today Oil, Energy, and Precious Metals jumped the gun and were off and running! We'll discuss more than just those areas, but first lets revisit what we were watching for.
WTIC - The set up was a Bull Flag pinched between support & resistance. Normally I would buy this with a stop below support, but I cautioned that the Fed Mtg Thursday may cause whip saw.

Oil is not waiting for the Fed Mtg. Many energy stocks were up over 10% and some were 15-25% today alone.

I will post some charts of energy stocks set up nicely at the end of the report.
Read MoreMondays trading was a little like watching paint dry in the markets and Tuesdays wasn't a whole lot better. You can bet that things will pick up at all when the Feds decision on interest rates is finally handed down on Thursday,and it's almost here. Lets look at what we have so far.
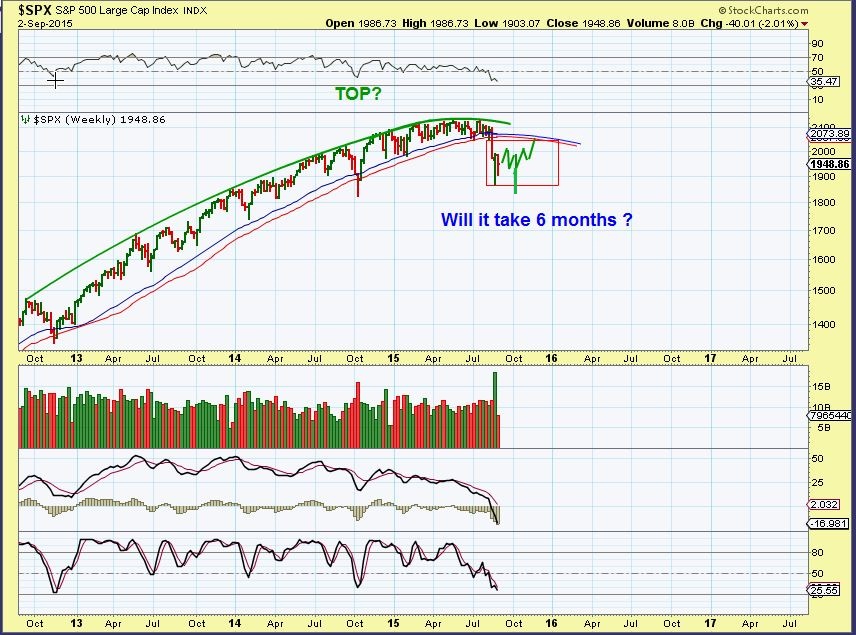
SPX - Tuesdays move gives it the look that it wants to break higher. If it does it may just back test of the break down.
 Read More
Read MoreI'm sorry if you came here hoping to hear an opinion on the FED EX company. I am actually here to point out that I am expecting some strong movements later this week as a result of the FED EXPECTATIONS. Some are expecting an interest rate hike and others are expecting no change. So far we are seeing a sideways move in most markets leading up to that big day this Thursday. I wanted to share some charts that were in my recent weekend report. They may help us to anticipate the reaction after Thursday. Lets look at charts.
.
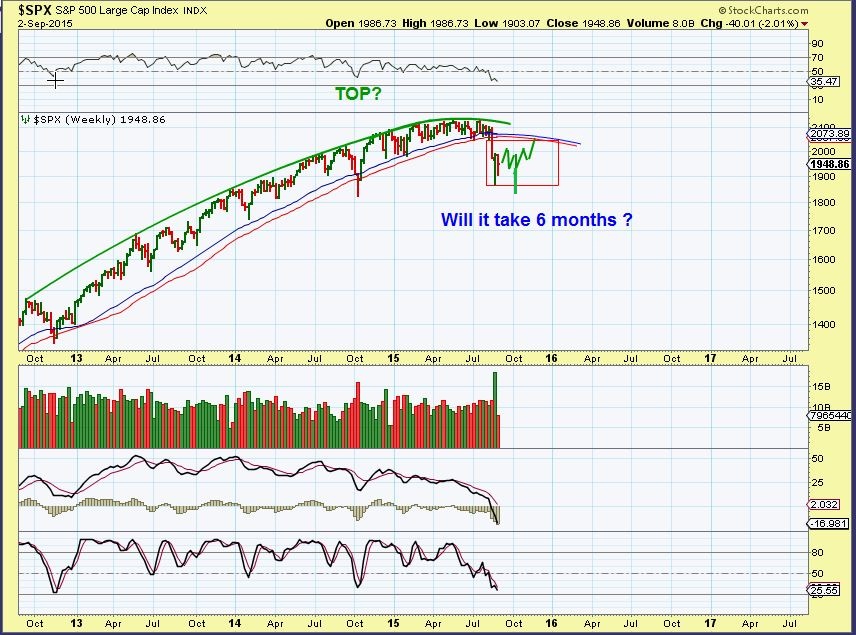
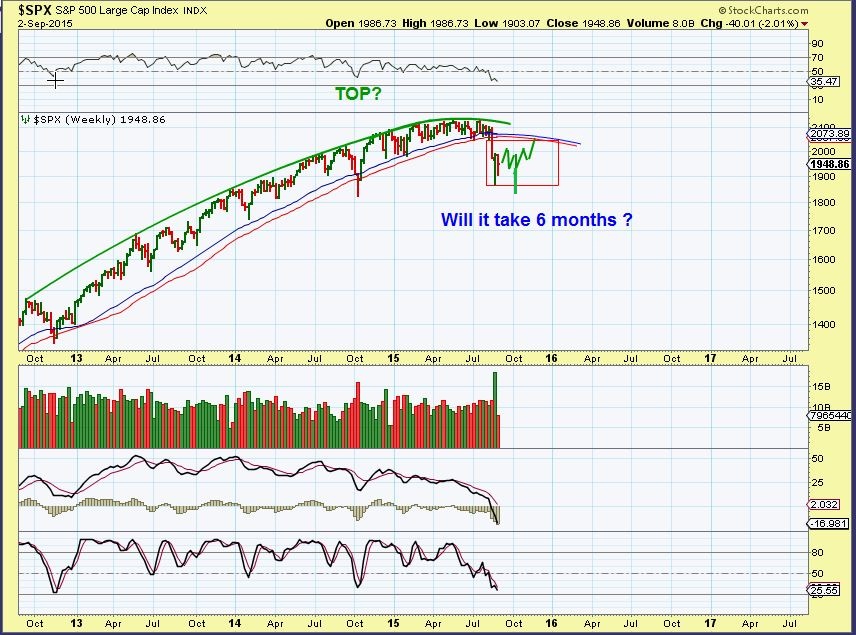
SEPT 2 - I pointed out the topping action in the markets last Spring & early Summer. After the initial drop, it should likely lead us to expect volatility, possibly even sideways for a long period of time. We have that now.
I want to point out what I am looking for next...
Read More
WTIC- Another slow motion sideways move, but this looks like a Bull Flag that wants to break higher. Will it before the FED Decision? Maybe.
Read More After watching the markets yesterday, I get the feeling that this week may be a sideways slow motion move that goes nowhere fast...until after the Fed Mtg. Lets review some charts.
.
SPX - You can see the same sideways move that has been playing out for weeks.
 Read More
Read MoreIn an earlier report I asked, "Are we still on track?" It would take time to know for sure, but things are still playing out well in some areas, yet a little trickier in others. Lets look at charts.
SEPT 2 - I pointed out this topping action and said to expect volatility, possibly even sideways for a long period of time.
I want to point out what I am looking for next...
Read MoreI wanted to post a picture of something where glue was just melting and everything was becoming unglued, because Wednesday morning I saw quite a bit of Green on my screen and by the close things become a little unglued. So it raises the question, "Are things still on the right track?" Lets look at the charts.
DJIA - Wednesdays rally hit the 20sma and back tested that down trend line, and then promptly gave it up. I actually think this type of action could lead to a nice post Fed rally next week. For now it is difficult to trade.
 Read More
Read MoreNow that we have seen some steady selling in various areas of the markets, some set ups look ready to buy again. Before discussing these set ups, lets review the markets in general.
.
NASDAQ - After the steep drop, we usually see some consolidation and chart repair under the 10sma. Eventually if you get a break back above that 10sma, price often continues higher. We could break back inside this channel, but it was the start of a downtrend. Trading is no longer buy & hold for many.

Lets see how the various market sectors continue to march toward their next big move.
SPX - Many thought that the recent sell off would recover straight up like the one on the left last October. Did you notice the back tests recently? These are acting like resistance points.

Lets look closer...
Read More
Scroll to top