Archive for month: August, 2015
I've been seeing differences between my long term view and my short term view for the markets. This could be indicating that we are seeing turning points. Lets discuss why that could be.
SPX - I've been seeing this longer term. It looks like the markets are acting rather toppy. Monthly charts are now showing weakness quite clearly as well.

Now looking at things from an even longer term view...
Read MoreLets review last weeks market action by stepping back and looking at the bigger picture.
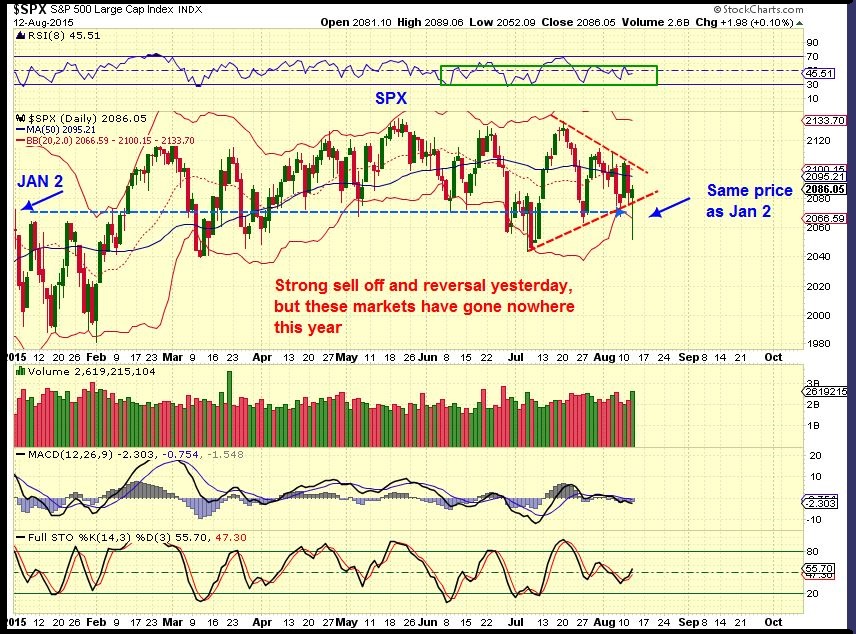
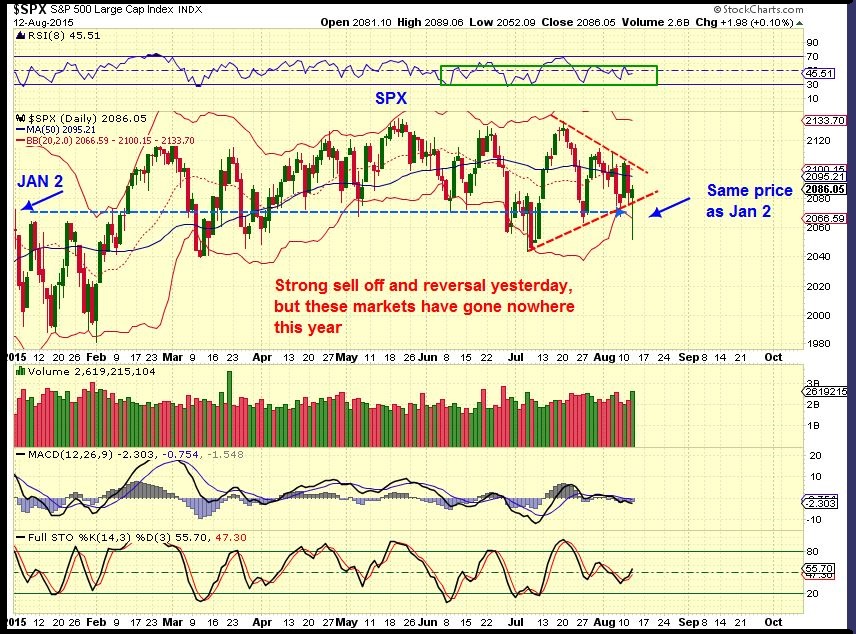
SPX - This long consolidation has left price right where it was in Jan. The MACD is dropping steadily on the weekly. This is a reversal candle so we may see a bounce this week.
 Read More
Read MoreAfter a solid 5 day rally, gold sold off on Thursday, and the precious metals miners were sold-off indescriminetly. Both GDX and GDXJ were down almost 6%, leading many to be shaken out of position on the pullback. For me, these events are expected and become opportunities, so lets examine the charts to see why.
$GOLD - a pullback to the 10 & 20 sma as support is normal.
 Read More
Read MoreThursday saw Gold sell off a bit, but Miners were really shaken. Both GDX and GDXJ were down almost 6% . We were buyers last Friday and Monday, so should we be stirred by this selling? I do not think so. We will honer our stops if necessary, but lets check the charts for confirmation.
$GOLD - a pullback to the 10 & 20 sma as support is normal.
 Read More
Read MoreI have good news and bad, but the bad news isn't really all that bad either. The good news is that we have done a great job of pinpointing and navigating the lows of what appears to be an ICL ( a deep meaningful low) in the precious metals market. The bad news is that we now have to navigate the upside and as you will see, its a bit trickier than many may expect. Lets quickly review the markets first.
SPX- This has been no picnic for investors either. The SPX is basically flat for the entire year. Strong sell off and reversal yesterday, but can it break to new highs? It needs to be monitored. A break below the July lows in the next few weeks would be very bearish in my opinion.
 Read More
Read MoreThere is more than one type of Gold Watch. The obvious one is the one that you carry around to tell you what time it is. The Gold Watch that we have been carrying around here at Chartfreak is the one where you closely watch Gold and gather clues about its next possible trade / rally. We were very prepared for what is unfolding currently. Let me share with you some of the charts I’ve used in the past week to prepare readers in the premium section of my reports this way.
The general markets could be a little “Toppy”, so I pointed this out first.

Aug 3 I reminded readers that the Semis were sagging

Earnings were disappointing. If the markets drop , maybe the metals would Pop? I showed charts of DIS, GMCR, TSLA, VIA, etc

AUG 5 – Many thought that the dollar was strong , ready to break to new highs and run to $1.20. I said that the dollar appeared to be weakening internally to me .

AUG 5– I viewed it this way . If the DOLLAR DROPS, could Metals POP? I expected the Dollar to drop.

Back on July 26 – The C.O.T., $BPGDM, EXTREME NEGATIVE SENTIMENT also pointed to lows in GOLD soon.

Though there is risk in all trading, and anything can happen due to geopolitical changes or circumstances, We were being dealt a favorable hand. A strong hand in the Precious metals sector was being dealt.

To help readers to see this as a possibility….
JULY 29 _ Most still calling for a plunge to $900 Gold ( yes it was possible) , but I pointed out that many were saying GDX had a bear flag. I thought it looked a lot like March lows AND I saw individual Miners starting to be accumulated. This added to bullishness. I used these charts below –

NG– running higher with Gold selling off? Bullish.

Gold selling off, but SSRI is not even close to the March lows

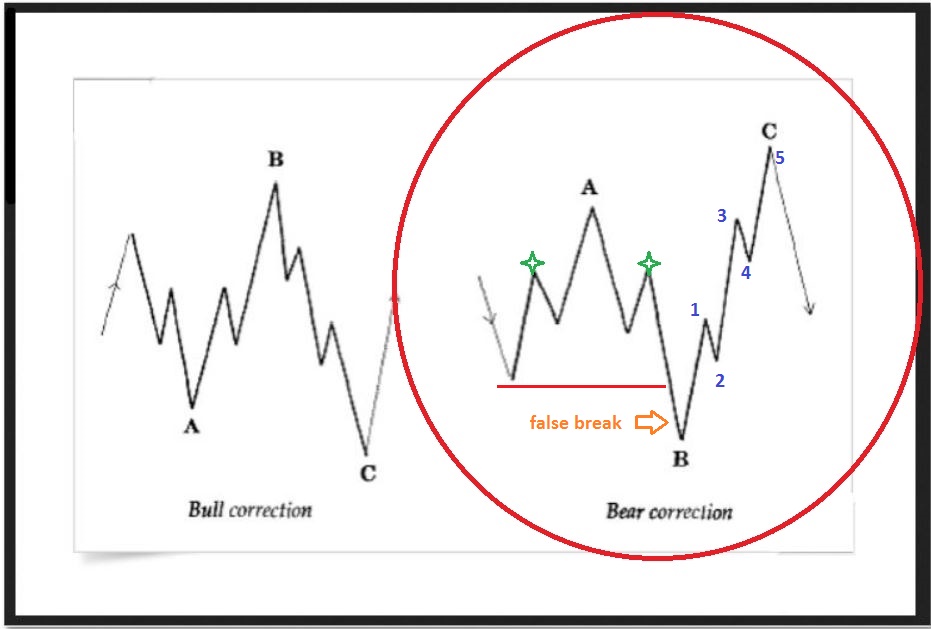
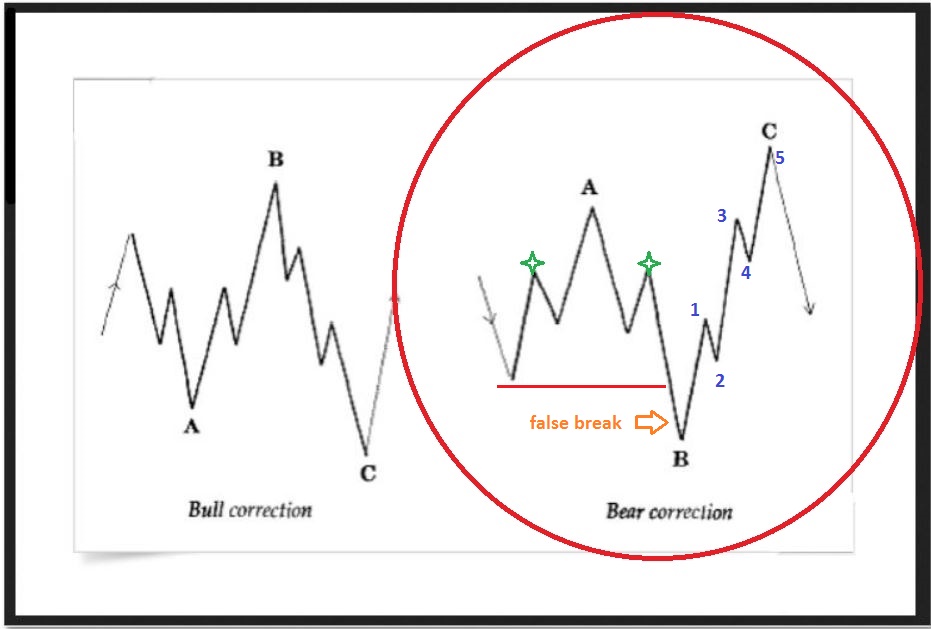
I’ll admit that I’m not a great E.W. technician, but I did think that these patterns fit well for what I was “Watching”.


FAST FORWARD to this past weekend. I showed various charts including this one. HEAVY VOLUME but price couldn’t sell off?? THAT seems like accumulation. At the very least this is a low risk buy at this trend line, because your stop is close below and the upside could be great.

So far Monday and Tuesday have not disappointed, and many Miners are moving higher with good %-Gains . Have you seen SA? Up over 70% from its lows. ( Disclaimer: I didnt grab this one early enough, but there are others set up in similar double bottom fashion).

I believe that this is not a 1 or 2 day pop, I think we are already seeing small bases and double bottom lows preparing to rally higher. I have been telling my readers that this set up is the type that usually runs for several weeks. Of course, they dont usually run straight up, there can be pullbacks in the stair step climb higher that offer buying opportunities… It may help if you have a ‘Gold Watch’ on your side.
Maybe you’ll consider signing up for a month and see if you like what we have to offer here? Todays report alone will have over 20charts. We also have a small chat section/ comment section under each premium report where some of our experienced traders share their ideas or questions too. If you’re not able to sign up at this time, I still want to thank you for reading along here at the free content section of the website.
Happy Trading!
~ALEX
.
P.S. I have been preparing readers since this spring that a nice summer rally would arrive this summer. The potential %-Gains could become the best short term trades you make this year. Best Wishes 🙂

Gold, Silver, and Energy stocks have been bottoming and some have begun adding nice %-Gains already. I had warned that if we didn't take a position, it might get very hard to do so. Why? We might see what is known as an Island Bottom. A Gap open higher that may not fill. I used this chart yesterday to point that possibility out.

Lets review some charts of Gold, Silver, and Energy stocks for potential entries...
Read MoreMid day thoughts...
Read MoreI was very happy to see the steps that the Metals and OIL markets took as the day went on. We will discus those steps in detail further on in the report, but first lets take a look at one of the major players in todays movement.
USD - many were saying how strong the DOLLAR was looking, but I was writing that it looked weak internally, since mid July. This should bode well for Commodities.

Notice the next chart of the Dollar...
Read MoreFor quite some time I have been pointing out things to take note of that are a little different than many others saw things. I think others are starting to see what we were pointing out here months ago. I was mentioning a bearish rising wedge pattern in the spring, and in June I looked at the SPX this way.

JULY 24, the SPX had not broken out from that toppy looking curve.

Would the BULL MARKET break higher soon?
Read More
Scroll to top