Archive for month: August, 2015
In last weeks reports, I was pointing out the things that were moving and really catching my interest. Lets review and see how things played out and what that can mean going forward.
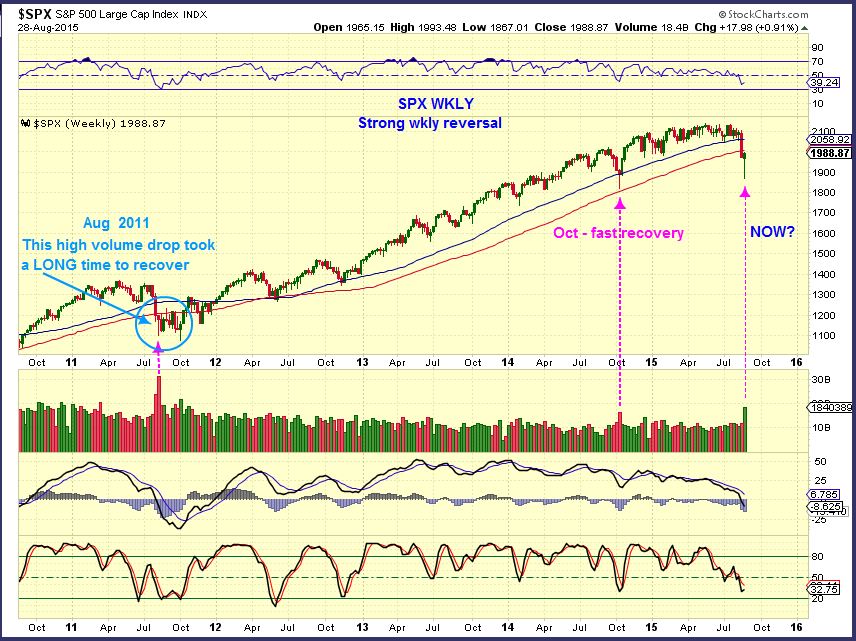
SPX WKLY - We had a very high volume sell off & reversal this week. The last 2 stand outs had 2 different immediate reactions. Aug 2011 just went sideways for weeks, while Oct 2014 recovered strongly.
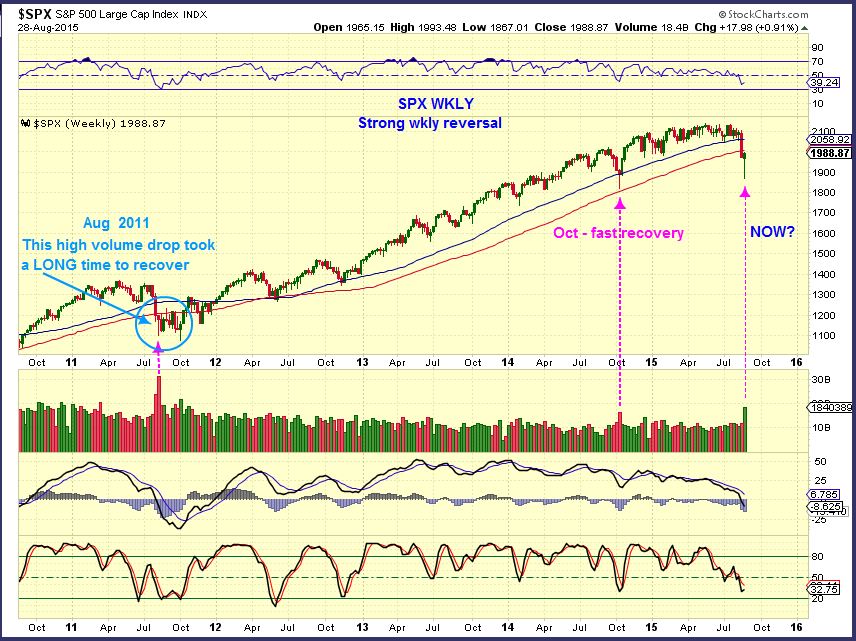
Which one is likely here, or is there another possibility? ...
Read MoreI wanted to post tonight because the action today was excellent. I think we may be getting the FAT PITCH that traders wait for all year. Lets take a look...
Read MoreWe all know that the markets don't move in a straight line, and lately the volatility has made the path to successful investing a bit trickier. At times it is best to get a longer term view of where things are headed, so the wiggles or shake ups don't knock us off course. Lets look at some charts.
SPX - This summer I was looking for that drop in the markets.

The question is , is it done?
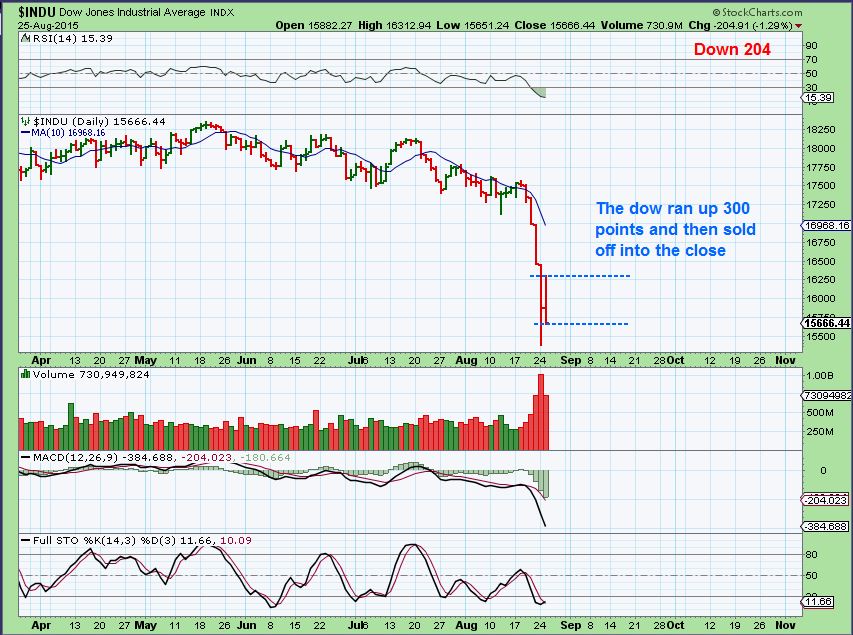
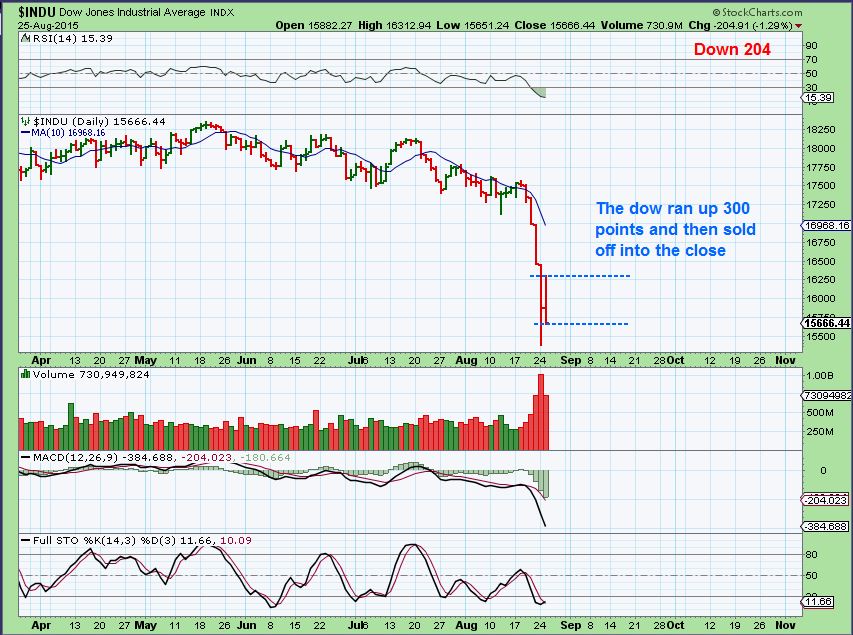
Read MoreAccording to Tom Petty, "The waiting is the hardest part". I do believe he's right, but at times it is the safest thing to do. For example, did you see the futures yesterday in the morning? The Dow was set to open up hundreds of points higher and in fact, most of the day the Dow was up 300+ points. We were putting in a very nice bounce and suddenly going into the close the Dow sold off and closed down 2o4 points. The S&P and NASDAQ did the same thing. Lets take a look.
DJIA - Both Monday and Tuesday if traders entered the markets during the rally, they were stopped out or seeing red by the close. Today the Futures are up big again.

The markets are very oversold. I expect a bounce up to the major moving averages, but that may actually be a shorting opportunity. Now If you look at the Dow this way, you can see that several more days like we just saw and you could make the case for the formation of a bear flag, wearing off oversold conditions.
 Read More
Read MoreAre you ready to make a leap of faith? A buying opportunity is fast approaching in MINERS, whether it looks like they are crashing down or not. Let me show you what I am seeing.
In July I showed that I expected a drop in the USD to the lower support line. This would cause a rally in Gold.

USD – We just had out drop in the Dollar as shown in this chart. Gold and Miners did put in a nice rally. Today the dollar is bouncing ( Up over 1.10 to 94.62) and Gold is pulling back.

I expect a second leg up in the precious metals to be greater than the first. Lets review …
GOLD, SILVER, MINERS
GOLD – Gold acted the way it should at this point. It rallied about $100 as the dollar dropped. Now the dollar is bouncing and we see Gold pulling back. This is normal activity

I expected this drop . Here are 2 reminder charts from the weekend premium report. Gold can simply drop to the $1130 area and find its support and form a Daily Cycle low (DCL) . It should then rise to new highs.

Gold was at resistance and the fib 61.8% number, so I understand why it didn’t just burst higher Monday. Pullback to $1133 is very normal. See fib lines.

I used this silver chart this weekend to show how silver acts in the first daily cycle, not always participating in GOLDs initial rally until the 2nd leg higher. Then it explodes! Are you ready?

.
Silver got dropped Monday. Silver looks horrible at the lows in every case in the chart above, right? Monday was high volume and looks ugly too . I confess that when I draw this chart, it is with a bit of bullish Bias, just knowing how it acts near lows. Silver can still go lower along that blue trend line.

EVERYONE IS TALKING ABOUT THE MINERS. Disappointing? YES! We bought the strong run off of the lows. The dollar crashed and with Gold at highs and our Miners took a nose dive? I didnt sell the top, just in case the pull back was more of a sideways move. I have sold some since then, but I am looking to re-enter very soon.
GDXJ Monday – We dropped fast , but it looks similar to the March drop. From the lows to the highs, we then fell 61.8% (yellow arrows). As Gold pulls back, I dont expect the lows in GDX / GDXJ to be broken, but if they are, it is likely just a stop run.

Now I want to show you 3 charts of GDX lows ( ICL) where price went up and dropped sharply like we see now. At least it helps to see how things played out then.
GDX 2008 – THE Bear Mkt Lows of October. Notice how price dipped back down to the bottom in Nov. Is that what we are seeing now in GDX, before the next move higher?

GDX Nov 2014 – Who can forget this dip back to the lows? Frustrating! Notice the High Volume plunge that came out of nowhere ( 1st red arrow). It then bounced higher, and dropped back down again. THAT could be what we are seeing now too, right before a strong 2nd move higher.

July 2012- GDX went sideways along the bottom like GDX just did. It also popped higher to the 50sma and quickly dropped right back down. See the high volume drop like we had Monday (red arrows) . The chart should say that we didn’t get the reversal at the close. ( Typo)

Let me show you 2 more important charts.
The purpose of this is to point out that at the Nov Lows and even the March Lows, some Miners that make up a big part of GDX bottomed, rallied , and gave it all up just like we see now. THEN when everyone gave up, they rocketed higher. The 2nd daily cycle can be very profitable.
GG – Last November – December. BOGUS 1st daily cycle! GG rallied and then gave it all up. Notice that the next run higher was great.

NEM – It also Rallied in Nov. and then dropped all the way back in december (It even broke them). Next NEM rocketed higher in Dec-Feb. At the March lows, NEM also lingered 1 month at the lows, then Rocketed higher! I expect that again.

SO I wanted to highlight the reason for Hope here with our Miners. The second daily cycle is coming and in the past it was a great time to make great %-Gains with the miners. We can make good money when its a little clearer that these miners have finally bottomed on their pullback. Here at Chartfreak, I’ve been monitoring this closely in the premium reports. For a small monthly price, you can join us . If not, I will still be posting here from time to time with public updates. You can sign up for free email alerts, so you will know when I do.
Best wishes and thanks for being here. 🙂
~ALEX
We were not long the markets over the weekend, but if you woke up Monday and you were? The above picture is a perfect example of what that probably felt like. Dow futures were down hundreds of points and there was no escaping the bear claws. We expected a drop, but I was very surprised at just how fast and deep things unraveled.
.
There will be a bounce, notice on the left side of this chart that even in Bear market sell offs, there are bear market rallies. Pretty big ones. We want to watch how that unfolds, as mentioned in the weekend report.
 Read More
Read MoreAnother little victory for the precious Metals Sector. I like to enjoy them while I can, since I know how fast these markets can change. We actually saw Gold move higher after the release of the fed minutes yesterday, and that was a small victory. A short term top may be close, so we'll discuss what that may mean.
First , lets review these volatile markets.
SPX- The markets may finally be rolling over.

We've been discussing this for weeks and I have mentioned that topping is a process, but notice these additional signs.
Read MoreToday at 2 P.M. Eastern time, we get the release of the Fed Minutes. Today could amount to a lot of "Hurry up and do nothing!" until then. Lets review and see where the markets currently stand.
.
SPX- yesterday I showed this break out, it looked bullish short term, but I noted that it looked weak internally

SPX - Price dropped back inside yesterday

How did the other markets fair?
Read MoreWanted to mention before the close...
Read More
Scroll to top