Archive for month: July, 2015
BELOW are clips from my premium weekend report
Seems that lately we've been hearing a lot about "Drops" in the markets. Remember when CNBC was reporting that Shanghais drop may never end until it hits the lows around 2000 again? "Its collapsing!" Well, all drops, no matter how steep, end when selling exhausts. I posted this support for my readers. Would it be a trade-able low?-

It did end there, so far. THAT was a trade-able low

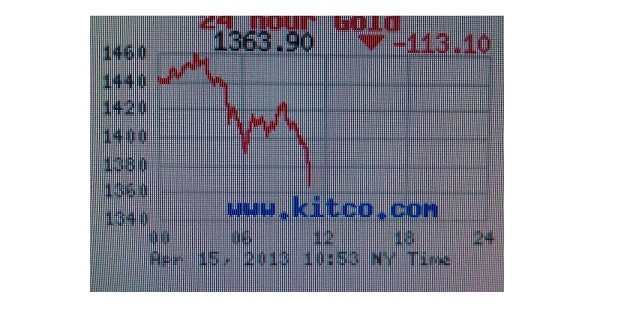
GOLD , SILVER, And the MINERS are dropping, but it too will end. It may become a very profitable trade. It may be not THE LOWS of the bear market, but rallies that come out of these exhaustion sell off s can be very profitable . Lets take a look...
Read MoreThis weekends report talked about "Drops", because many markets like the Shanghai and even our own markets recently encountered them. I mentioned that after a drop, their often comes a great opportunity and now the equity markets were rallying. Gold has entered its cycle timing to put in a low after it finishes its current drop too. What does that mean? It means we should discuss RISK, as we approach what I think is going to be an excellent buying opportunity in the precious metals area. First lets review the markets...
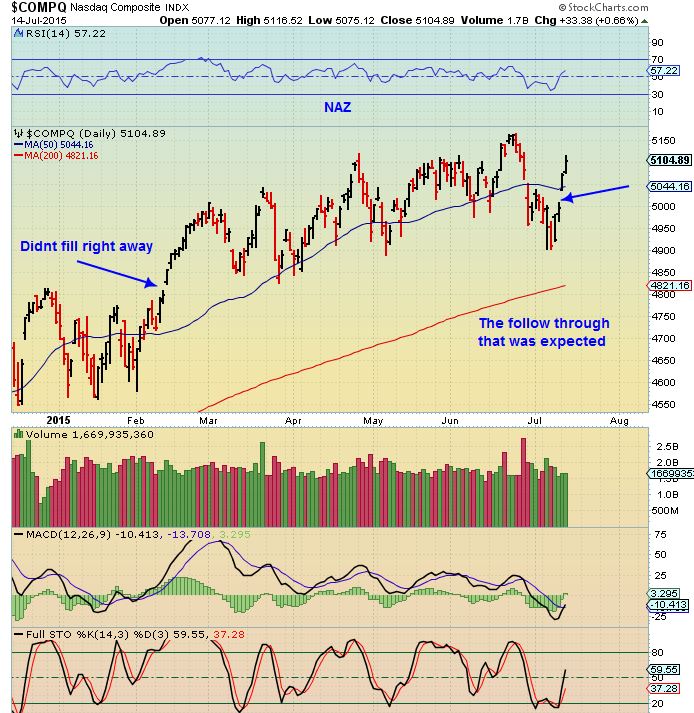
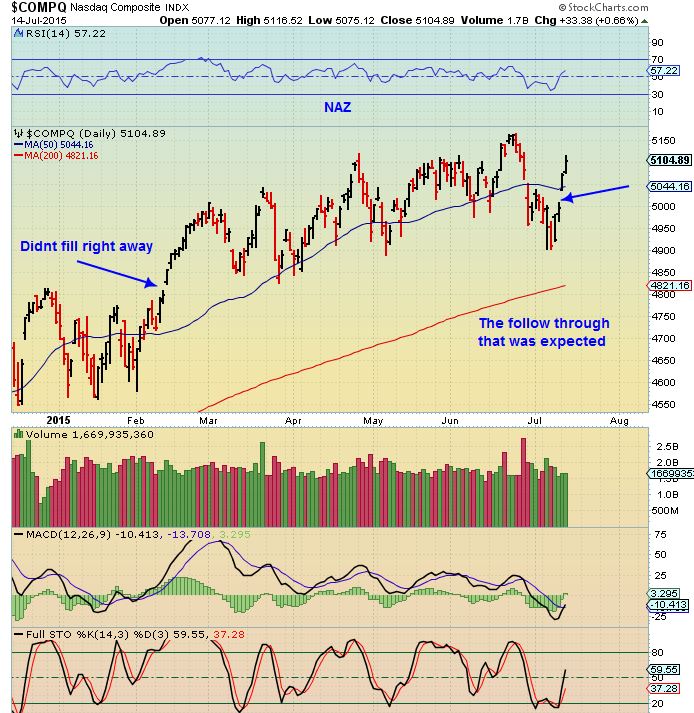
NASDAQ - We have rallied nicely out of the ICL as expected. We are outside the Bollinger Bands (not shown) and we could get a pause here sideways, or even a pullback. Notice that eventually all break outs get tested.

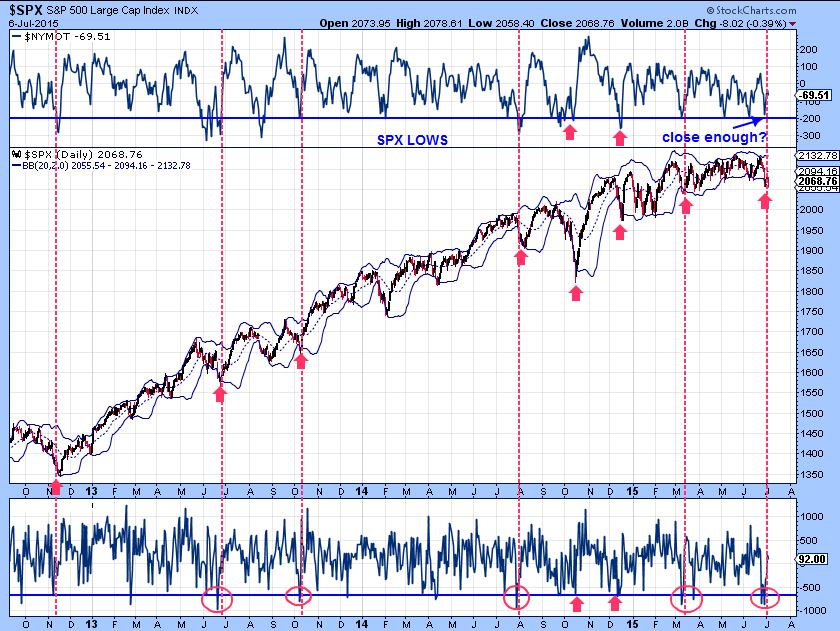
Interesting thing about the chart of the SPX...
Read MoreSeems that lately we've been hearing a lot about "Drops" in the markets. Remember when CNBC was reporting that Shanghais drop may never end until it hits the lows again? Its collapsing! All drops end, and this one looked like it may just return to the break out.

It did..

And the stock market itself just had a drop, blaming the concerns of China, Greece , etc as the problem. Lets discuss these drops since GOLD / MINERS starting dropping rather rapidly last week too. Will it end? Of course. Where and when ?? Lets discuss drops ...
Read MoreJust a quick note for today ...
Read MoreLets talk about timing.
So far the markets are acting as expected for an equity market that has found its ICL. The Excessive Bearish sentiment , Put / Call Ratio extremes , the Vix and Various set ups pointed out here in early July were all calling for a contrary reaction. Not what the crowd would expect. I expected a rally, but waiting for it each day seemed like time was being warped. I still see the Precious Metals under similar circumstances, but as you wait for an inverse reaction , it seems like each day is a week. Lets review this thinking.
Here is one of the many charts that I used to say that I expected a meaningful low in the equity Markets. This was July 6th. Extremes comparable to OCT & Feb lows were in place, but when would we see a rally?
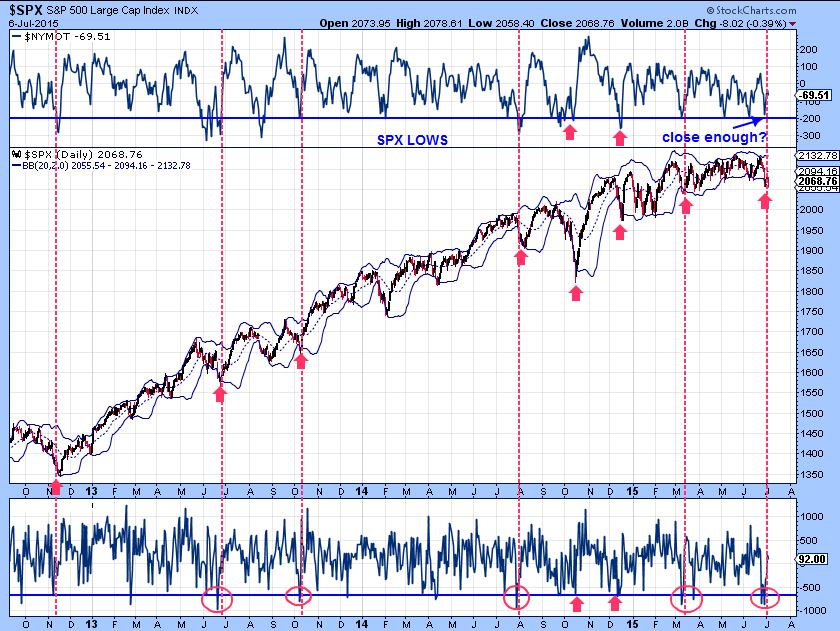
SPX July 15 - Notice that after July 6th, we dropped to new lows July 7,8,9. Three days felt like forever, but now they are forgotten. The rally continues to have follow through.

Keep the above in mind, and we'll discus it further in the report.
Read MoreBelow are just a few trade ideas.
We try to find low risk set ups and entries. To ensure that the risk remains low, we use reasonable stops and honor them if the trade goes against us. Being wrong is OK, it will happen from time to time. Staying wrong can damage your account.
WIX - Just broke back above the 50sma again. Your stop would be under the 50sma.

GPRO - re-gained the 50sma, but gapped open. You may want to wait for a break out above the blue dotted line

Continue on...
Read MoreHey, it did happen a few yrs ago, but now that I have your attention 🙂 I need to review something in the GOLD - SILVER - MINERS section of this report. First a quick review of the markets.
As expected , Follow through in the DJIA, SPX, NASDAQ, etc
 Read More
Read MoreWhen the markets are volatile and choppy, it can be difficult to buy and hold a position for anything more than a day or two. We have had some very choppy markets lately. The good news is that the current set up that I am seeing in the markets currently may provide an opportunity to 'SHOP' with a little less "CHOP".
SPX - The blue lines point to the type of run I think we will see. We may have a pause or two, but I expect higher prices.
 Read More
Read More ** This report contains excerpts from the GOLD & SILVER section of my premium report this weekend.
After doing a lot of research last week and this weekend, I am thinking that we could see a very trade-able low in Gold & Silver, and very soon. Almost all of the letter writers and gold reports that were out there were saying that Gold would crash to $800-$1000 this spring. My readers know that I maintained all along that I did not see that happening (yet). 🙂
Lets look at The USD , GOLD & SILVER
Read MoreThis report covers a lot, especially when we get to the precious metals - Gold, Silver, & Miners part, so lets just get right into it.
.
SPX - It has been a very volatile market, but let me discuss why I am getting signs of a meaningful trade-able low here (or very soon).
Read More
Scroll to top