Archive for month: April, 2015
Ready For The Fed?
/62 Comments/in Premium /by Alex - Chart FreakIf you look at the volatility in the stock market lately , it would seem reasonable to believe that this Fed Mtg Day could be a shaky one. Yesterday TWTR ironically got rocked from an untimely tweet on their earnings. As mentioned in a prior report, Housing stocks MTH, PHM, TOL, LEN , DHI all got rocked, while MSFT, NFLX, GOOGL shot up higher with their results. After the bell, SSYS, WYNN, AKAM and a few others joined TWTR in the selling off , so we're getting a mixed picture with the weeks earnings reports. And then there was this chart...
IBB - Yes, it has recovered it's 50sma before, but it has work to do. Thats some pretty high volume selling lately.

With the IBB 2 day drop, something interesting happened with the SPX...
Read MoreGOLD & SILVER
/24 Comments/in Premium /by Alex - Chart FreakLets discuss GOLD& SILVER briefly.
Read MoreEARNINGS + FED WEEK = ???
/33 Comments/in Premium /by Alex - Chart FreakMonday morning when we woke up, The General Market Futures were higher and it seemed like smooth sailing. Suddenly a storm was moving in and things started giving it up . With an active week of Earnings and the 2 day Fed meeting , lets take a look at the charts and see what we can see.
IBB- This was taken as of 2:30 P.M. Eastern time ( I added the end of day volume) .
We've seen this before right? A huge drop at the end of March and recovered at the 50sma. Is that what we can expect? Let me show you what it tells me..
Read MoreEARNINGS!
/50 Comments/in Premium /by Alex - Chart FreakBetween the Earnings Reports last week and the FED this week , the markets have begun looking quite interesting in many ways. Lets take a look...
April 22 - I pointed out a consolidation that could break to new 'closing' highs in the NASDAQ.
Would it Break or Fail during earnings ?
Read MoreWhat To Look At
/53 Comments/in Premium /by Alex - Chart FreakI dont always do a Friday report, but there were a few interesting things that happened in the market. Lets see what those were...
This was the SPX going into yesterday, you can see that anything higher would be a break out type move
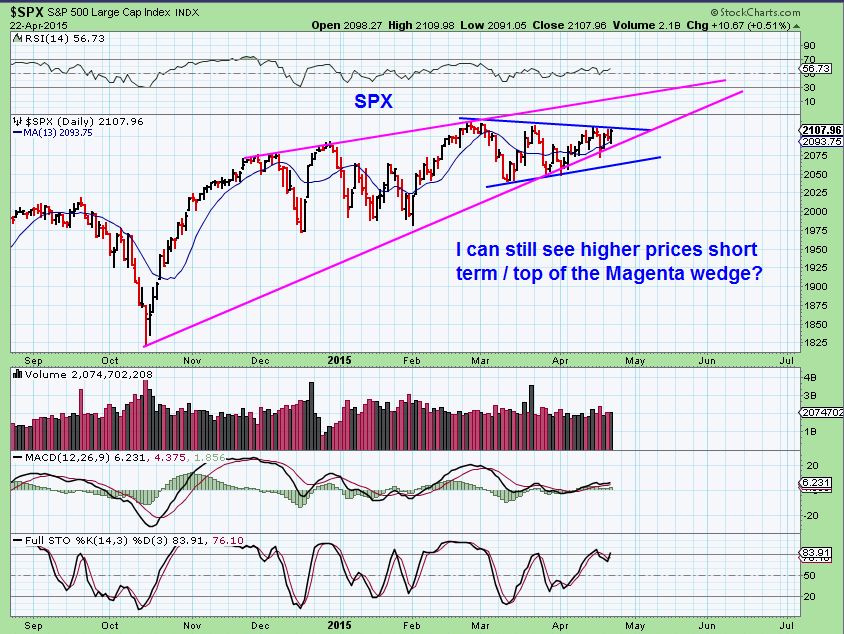
Yesterday the markets did move higher, but they pulled back into the close.
Read MoreWatch Lists and Set Ups
/70 Comments/in Premium /by Alex - Chart FreakFirst, I apologize that this wont be out before the market open, I think I had food poisoning last night and it was a rough ride. I am looking at the markets and stock set ups that have been discussed and wanted to just review a few things to watch for going forward. We'll start with our market recap ..
SPX futures are down as I write, but there is still upside possibility short term, if this breaks out.

That being said, there is still this reminder...
Read MoreSometimes It Feels Like A Roll Of The Dice
/49 Comments/in Premium /by Alex - Chart FreakYesterday I had a ton of bullish chart set ups and I posted some of them here. Since we are in an earnings period, some of the charts broke out higher, some went lower, and others broke out higher and then reversed lower. It felt like a roll of the dice, but honestly, the bigger picture of the markets themselves may have a lot to do with future direction of many stocks, so lets review some charts again!
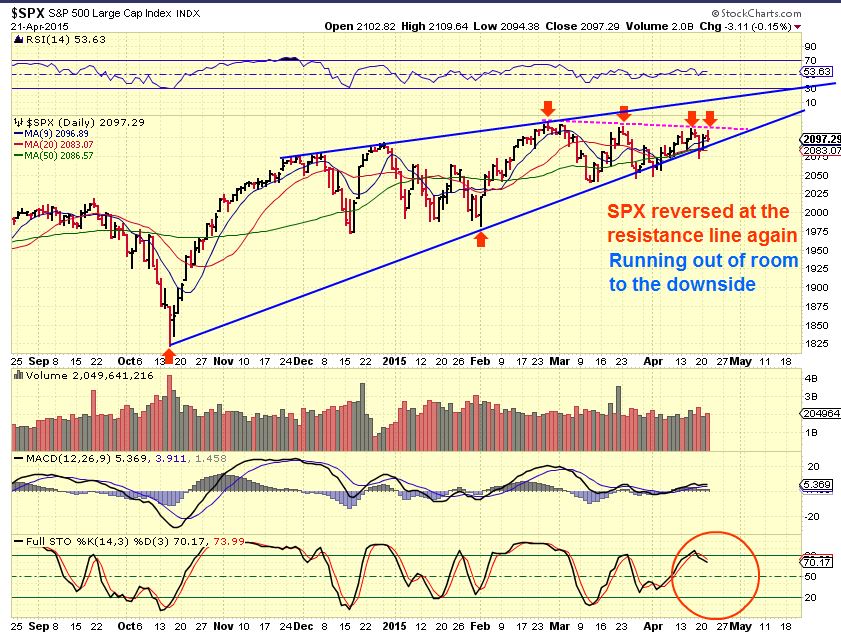
.SPX - I figured we'd make a run for the top of this wedge, but that resistance line reversed price again. It is running out of room!
The NASDAQ gapped higher and didn't quite give it up...
Read MoreSTRONGLY BULLISH CHARTS
/77 Comments/in Premium /by Alex - Chart FreakI dont want to spend a lot of time discussing the SPX, DOW JONES, NASDAQ, ETC when you can just look back at the weekend report and see that not much has changed in the bigger picture. Instead I want to run through a bunch of bullish looking charts. Oddly, it seemed that in almost every sector that I went through on Monday, Bullish set ups were there. Lets view about 30 charts from various sectors and discuss a few of them.
VJET- 3 D Stocks have bullish set ups. For traders , this is a low risk entry above the 50sma.

Next...
Read More
Keeping An Eye On Things
/36 Comments/in Premium /by Alex - Chart FreakThis was a great week of trading. Oil broke out and all of our energy stocks put in some strong gains as expected. My call in NATGAS played out exactly as outlined , and this could play out nicely for traders this week too. Lets look at some charts and see how things went in other sectors too , and what we might expect moving forward.
SPX - I have been showing a bearish rising wedge pattern, like in my April 10 chart. We had more upside, but then the markets did start selling off Friday. Is that it?

I also want to show you something else.
Read MoreContact Us
26 Broadway,
8th Floor
New York, NY 10004
admin@bigleaguefinance.com
admin@bigleaguefinance.com
Latest Blog Posts
accelerator diet pills goji berry diet pills ultra 90 diet pills keto meal replacement bar top weight loss diet pills for thyroid patients where to buy t lite diet pills keto friendly thickener diet fuel diet pills peanuts keto friendly rite aid diet pills that work envy diet pills diet pills for breastfeeding moms belique diet pills perfect slim weight loss pills calories in a bottle of white wine