Archive for month: January, 2015
OBSERVATIONS
/10 Comments/in Public /by Alex - Chart FreakI have been watching the various markets intently , examining internals and how they've reacted under similar circumstances in the past to try to get an idea of what to expect . I think that I have done rather well with the general markets and Metals and miners, but I must say...there are some extremes in some areas that I have just left alone until I get a clearer idea of how things may unfold going forward. What am I referring to? Well, specifically the ENERGY sector with OIL and NATGAS has been a little tricky, and of course the $USD has been very strong - now even higher than I anticipated. lets take a look at those areas. They that have been difficult to call, for Sure.
I know what I "Guess" they could do, but when it comes to putting advice in my premium reports on these sectors, I have decided to just wait until things clear up , and focus on some other very trade-able areas.
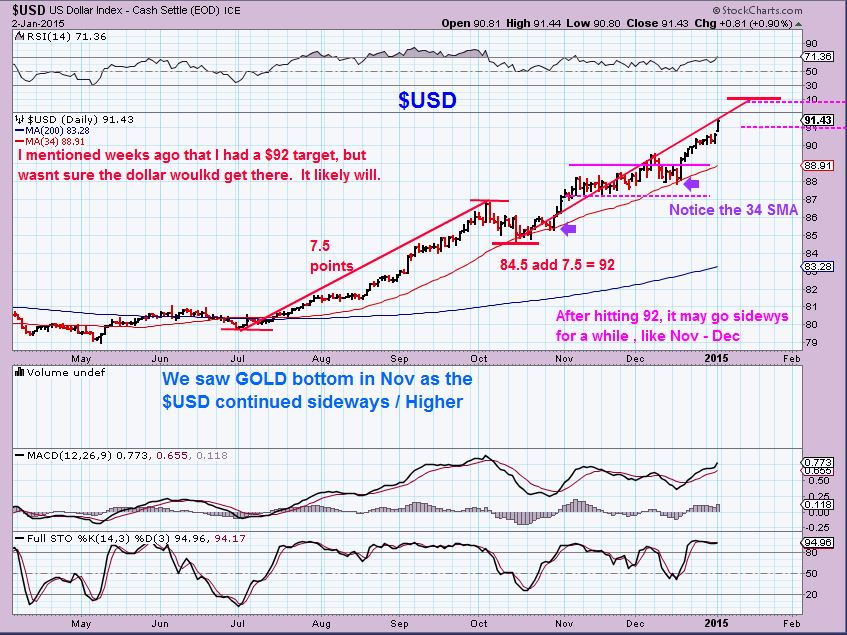
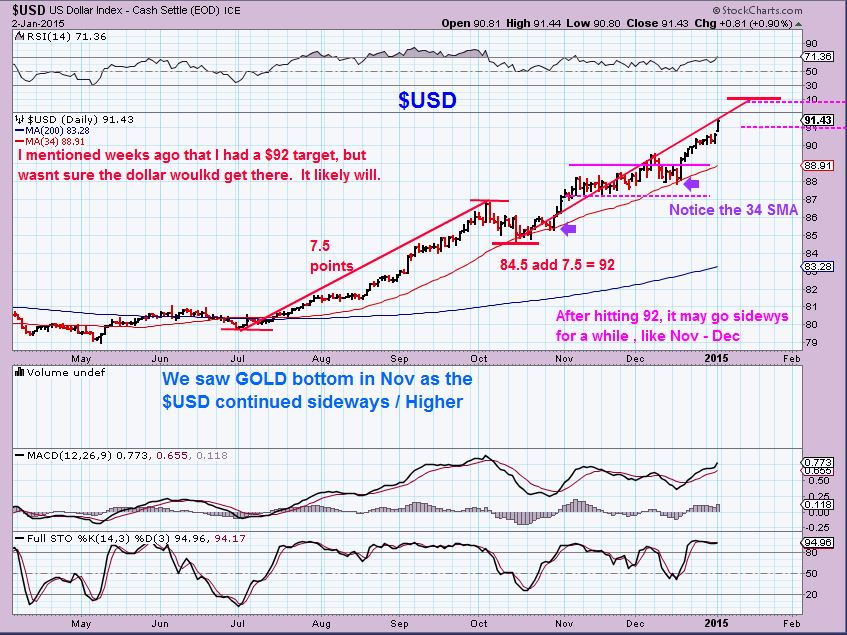
I expected the $USD to stop in the $92 area. ( Actually, I had that as a target, but I thought it may not make it there, I mentioned that it could roll over near 91 because GOLD began completely ignoring the $USD strength. I assumed GOLD was sniffing out Dollar weakening).
I posted this chart Jan 2- $92 target
Then on JAN 5 , I noticed this ...
Read MoreNothing Has Changed
/13 Comments/in Premium /by Alex - Chart FreakYou could basically read my last few reports and get the same results. Even though the numbers have changed and the moves are taking place, my outlook hasnt changed.
Here is yesterdays wkly chart of SPX - we expected a move higher, but a bounce or a buy the dip recovery?
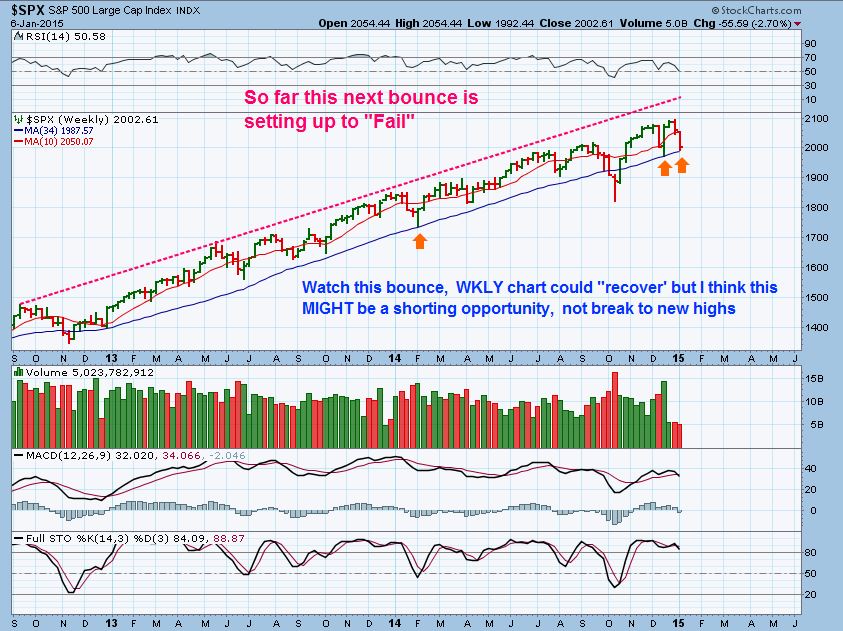
I thought that the markets looked a little 'different' this time, so I mentioned that it could 'fail' . Yesterday we did have a reversal
And CNBC had a lot of people on saying, "You just have to Buy the Dips. Its been working for years now! " Is THAT what I mean when I say nothing has changed?...
Read MoreEXPECT PULLBACKS
/20 Comments/in Premium /by Alex - Chart FreakMarkets dont go straight up or down
( yes I've seen the $USD and Oil Lately  ) Well actually, they haven't been 100% straight up or down either. We expect Pullbacks , consolidations, dips, etc . Even the straight up dollar move wasn't straight up , as you can see here in my Jan 2 chart, there were dips ...
) Well actually, they haven't been 100% straight up or down either. We expect Pullbacks , consolidations, dips, etc . Even the straight up dollar move wasn't straight up , as you can see here in my Jan 2 chart, there were dips ...
Pullbacks happen all the time, and the key is to examine them separately and look for opportunity. Lets discuss pullbacks ...
Read MoreMany Still Cant See It
/22 Comments/in Premium /by Alex - Chart FreakMany still cant see it , lets zoom in for a minute
If you're worried that the public will see this , dont. I have posted for 8 weeks my thoughts on a particular sector in extreme detail, and I still cant convince everybody of what I have been seeing, this Picture wont change anything for the public. So Lets discuss Various Markets ...
Read MoreA Minnie Victory
/19 Comments/in Premium /by Alex - Chart FreakFriday was a Mini victory if you ask me, and I'll tell you why after a brief update of the markets. So far The SPX, Q's and Dow acted just as I thought they would, they have dropped after making new highs (QQQ was likely not going to make new highs, and it didnt ). DEC 30 - I posted this that I'd be watching the QQQ's at the 10sma, it looked weak.

Well, it broke right through the 10sma by the end of Dec 31, so what now? All doom & gloom from here?
Read MoreDo You Recognize The Difference?
/2 Comments/in Public /by Alex - Chart FreakReal Strength and Real Weakness.
In Humans , sometimes strength & weakness can show up as obvious, seen by outward appearance alone. In some cases, however, it may require an X-Ray to peer inside and see how the internals are doing. Its really the same with the markets. A Rally can appear strong, and yet inside it may show evidence of weakness , and visa-versa can be true too.
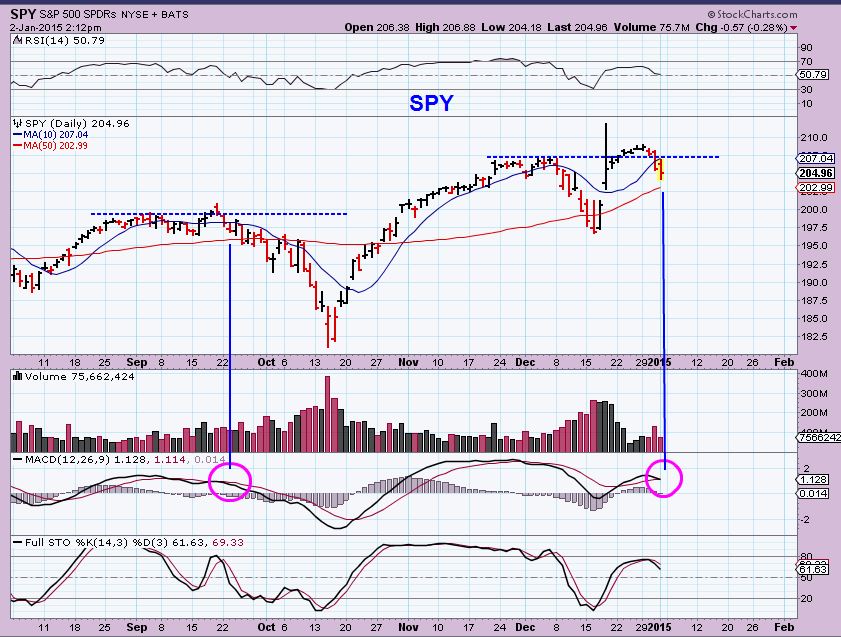
I know many felt that the year end 'Santa Rally ' , as it is often called at the end of the year, looked like a strong continuation of the rallies that we are used to seeing lately. Here at Chartfreak, I was mentioning to my premium readers that under the microscope, the rally looked to be weakening to me. I thought that we might actually see some rolling over and possibly even some selling into 2015. For how long? We will know soon enough, but notice what I was pointing out to my subs last week.
THE SPX was falling short in some of its 'internals'- It looked weak to me as it was breaking out. I thought it might actually roll over after breaking to new highs, like it did in September.

SPY NOW ( Broke with weakness & fell back)
To me the QQQ looked even weaker...
Read MoreLow Liquidity
/16 Comments/in Premium /by Alex - Chart FreakDuring times of low liquidity, it's easy to rock these boats back & forth , but it's not always easy to get them sailing smoothly in the intended direction. When the tide rises , or the flow of liquidity returns, however, they can begin a journey of smoother sailing . During weeks of holiday trading, its similar in the markets. low liquidity can cause volatility and rock things back and forth, but it's not always clear which direction things really want to flow.
Today is January 2, and it's the first trading day of 2015, but I'm not so sure that the liquidity will return until next week. Until then ,we may have more volatility and things may not look very clear, but there are some interesting developments to look at. As I write (Pre-Mkt) Futures are up nicely for the DOW, SPX, and NASDAQ, while GOLD shot down to $1169 , Silver is down .10 , and OIL has dropped to new lows. The $USD is again strong, up to $90.85! I still think next week will clarify the true direction of these markets, but notice this...

The dollar is at new highs in Pre-Mkt at almost $91., yet Even with the continued Dollar strength...
Read MoreContact Us
26 Broadway,
8th Floor
New York, NY 10004
admin@bigleaguefinance.com
admin@bigleaguefinance.com
Latest Blog Posts
accelerator diet pills goji berry diet pills ultra 90 diet pills keto meal replacement bar top weight loss diet pills for thyroid patients where to buy t lite diet pills keto friendly thickener diet fuel diet pills peanuts keto friendly rite aid diet pills that work envy diet pills diet pills for breastfeeding moms belique diet pills perfect slim weight loss pills calories in a bottle of white wine