Archive for month: January, 2015
We have been watching some great battles going on, and thankfully we have been able to make some nice trades despite the up & down action of the various markets. Volatility can be a traders paradise, but an investors nightmare as price basically can remain the same in the up & down battle for direction. Having technical analysis, some cycle counts , and a bit of experience in our tool box , we gain an edge in certain areas. This weekend report will highlight some interesting charts ( 24 charts again to be exact!) ...so to the charts!!!
Well look at this break out in OIL

It exploded at the end of Friday and shot up 8%. That is a lot for a commodity like OIL. It closed above the 10 & 20 sma for the first time in a long time , as you can see.
Read MoreI dont always see the need to post Friday , because Thursdays report covers my expectations and Friday usually doesnt leave me with much to say until the big weekend report. Today I just felt the need for a quick update because 2 questions arise...
1. Has anything changed?
2. Do you want to hold over the weekend? QUICK commentary
$NATGAS - The "Floor" broke down. May just be a 'test', but you should be out

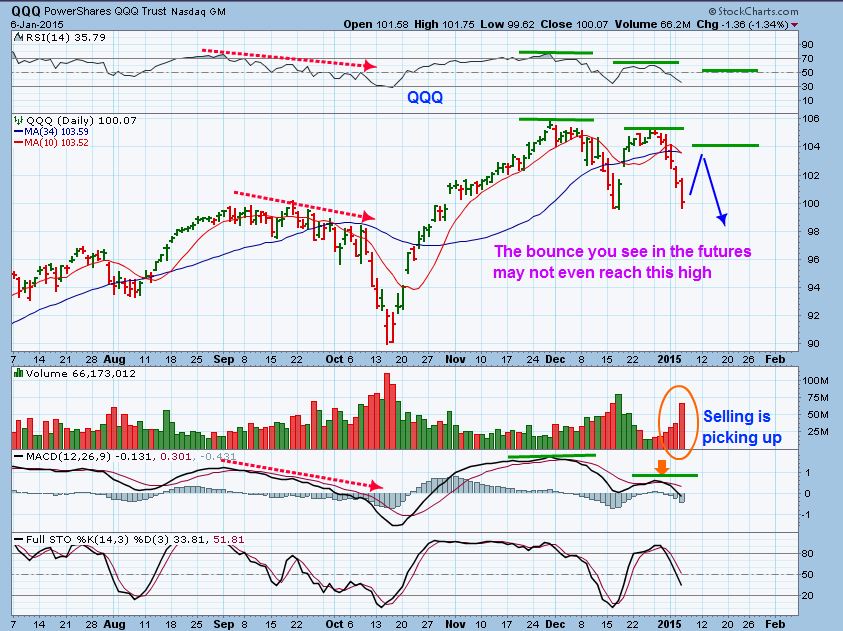
SPX/QQQ/DJIA ...
Read MoreYou can just Re-Read yesterdays report on the General markets , and then come back here and see how much clearer it looks with the charts supplied today. Yesterday I was saying that Futures where up , but could it last? ....
Well, Let me just start with a chart that I posted yesterday ...

Now check this out...
Read More(This report was written Tuesday night )
Warning, this report goes against " common group think" Why? Well , I want to show why slowly but surely it looks like the "Buy The Dips" crowd may be exiting the building and the next few charts may be proof. AAPL & YHOO had pretty good earnings, can they save the day? Or will it prove to be just another bounce? We shall soon see, but it's also another F.O.M.C. Wednesday and as you know...anything can happen after 2 P.M. Eastern time! In the meantime, lets glance at a few charts.
MSFT - Oh she used to be a wall street darling. This is a Weekly chart and so far the volume is HUGE for 2 days.

Is that just a fluke? A one bad amongst many beauties? ...
Read MoreDue to the Storm approaching New England, I may lose power ( As mentioned in my wkend report), So I want to share a few possible trade ideas for you to watch , in case I wont able to post anything tomorrow. Let me start by showing you an Energy stock that got taken out to the whipping post. It is beaten down and double bottomed. It seems like all of the downside ( At least for now) has been met. Risk reward is skewed toward less risk (Using stops) and more upside potential if conditions play out. Some of these stocks could just "Bounce" and do very well.
EXXI WEEKLY - Double bottom with a MACD cross?

Why would I call it low risk though? Isnt it high risk, in danger of getting cut in half again? Well, consider this...
Read MoreHave you ever seen Black Ice? living in New England I've seen it a lot. It looks like solid dry black pavement, but Suddenly you see someone walking along and Whoosh! , their feet fly out from under them and they are flat on their back. Invisible Ice. Well on occasion, I've seen something similar occur in the markets. You're going along and all things look solid and safe when suddenly...Whoosh! things slip away. I want to mention this now and first off, so that THAT image sticks in your mind when I cover the weekdend report.
Our recent consolidation that was looking a little Bearish in many ways (as shown in prior reports) Got Draghi juice and suddenly looks a little more normal. This is the SOX index on Friday

Does that mean we'll break out in Bullish fashion soon? ...
Read MoreI have to be honest, I was recently looking at the markets and thinking that the apparent weakness was going to prevail. Recently I've been staring at the SOX and something is starting to pop out at me. let me explain...
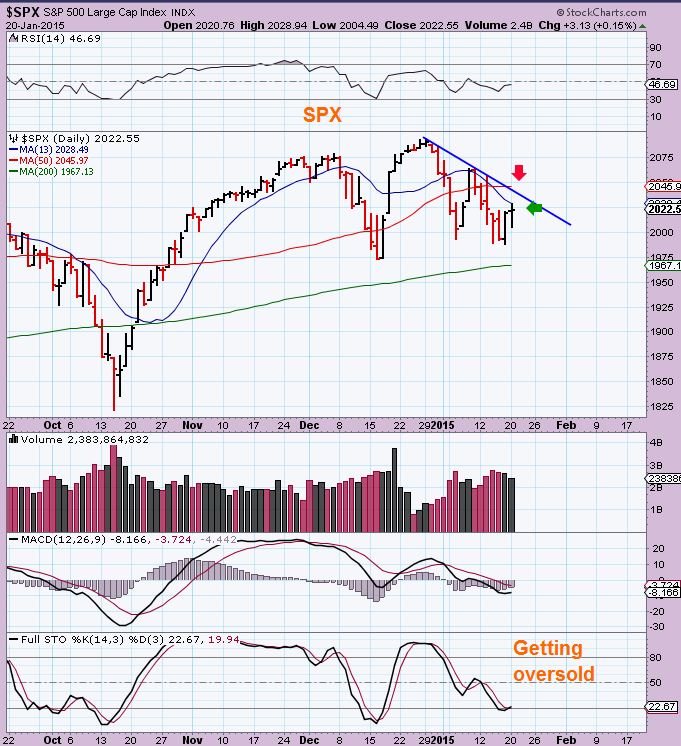
I had mentioned to my readers back in DEC that I thought I saw internal weakness in the markets. As the markets began to weakly bounce & Roll over, I then posted this chart JAN 6 and mentioned that though I expect a bounce here, I thought we may 'fail " at the 50sma. BUY THE DIPS might not work, and possibly a short set up .
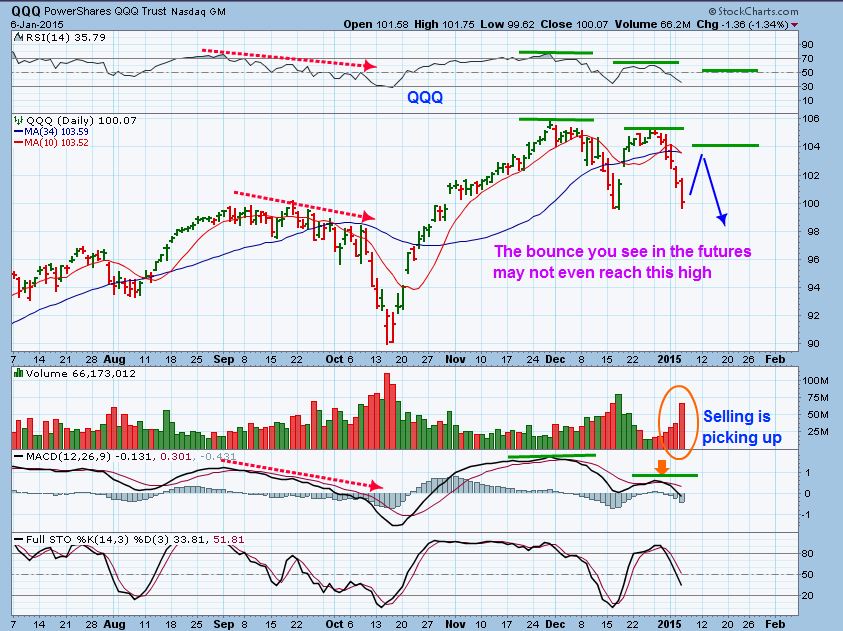
By Jan 21 the weak bounce had played out, I began to think we may get a good shorting opportunity, but wait for that ECB mtg.

But then I saw those SOCKS! No, not the multi colored array of Socks above, I mean ...
Read MoreDid you see the $USD? Did you see the QQQ's? Did you see $Gold? Looks like "Happy days are here again" ? Well the markets certainly did react strongly after the ECB announcement, but will it last? Can it last? It really raised more questions than it answered, so lets look at some charts.
SPY - Which was struggling below the 50 sma got a bit of a boost yesterday

In some ways , the 3 Q's looked even a bit better...
Read MoreMany times when markets move , they are often setting up for the next trade. As things are setting up , Its not always possible to tell if the set up is Bullish or Bearish. I have mentioned here what I am seeing in the markets, but with the ECB meeting taking place and the results of that meeting not being released until (supposedly) 8:30 Eastern time, the goal is patience. Often traders & investors dont realize that over trading can cause one to slowly give back the gains recently made. So while we need to invest to make money, we also need to learn patience to be able to avoid knee jerk reactions and head fakes. While we wait....Quick review.
NOTHING has changed with the SPX,QQQ,DJIA, etc

Like yesterdays report 'Groundhog Day" mentioned, as time goes on, not much has changed. One thing I did notice is...
Read MoreI feel like I'm living in that movie Groundhog Day, where you wake up and though some things continue to change, its just a repeat of yesterdays events. The equity markets moved a bit , but its the same old movement, and leaves me with the same conclusion. As for GOLD & Miners, NATGAS, and Oil? I am expecting changed that I will discuss here.
First lets look at the SPX as of yesterdays close
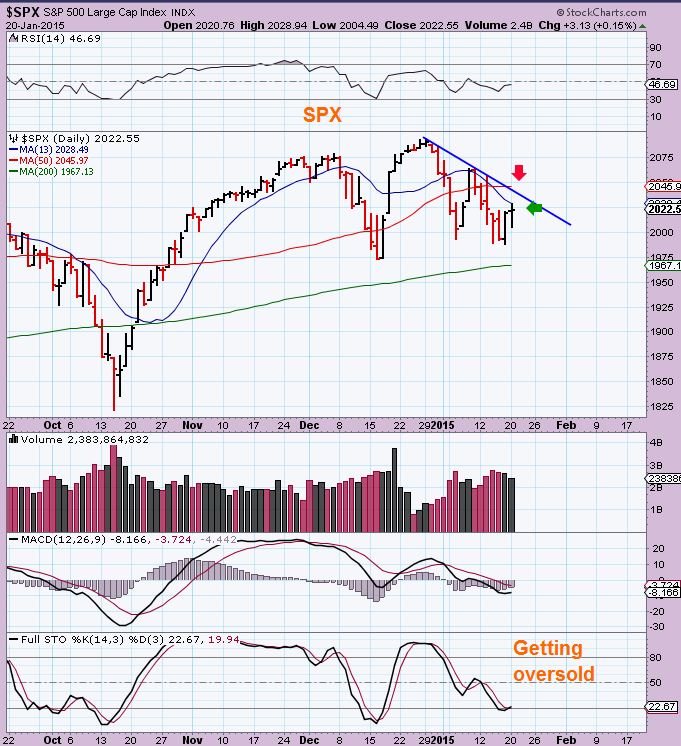
You can see that we are getting the same movement as expected and ...
Read More
Scroll to top