Just a quick run through since we have just 1 trading day left in 2014 and it 'Should Be' a light volume day , since many will be leaving early to prepare for any evening activities. I'll start with QQQ. I posted his chart yesterday and said it looked like we could are stalling and could begin to pullback...

This is what happened Tuesday ...
Read MoreWhen I think about the markets right now, it is Dec 30and we have 2 full days left for the markets to trade in 2014. I'm thinking that we are seeing a little hot air balloon action, where things just keep floating higher on light volume. Maybe people dont want to sell now and have to pay taxes this year on their recent gains, but what will they do in January when they can take some profits and not have to pay taxes on their gains until 2016? Will they lock in some gains?
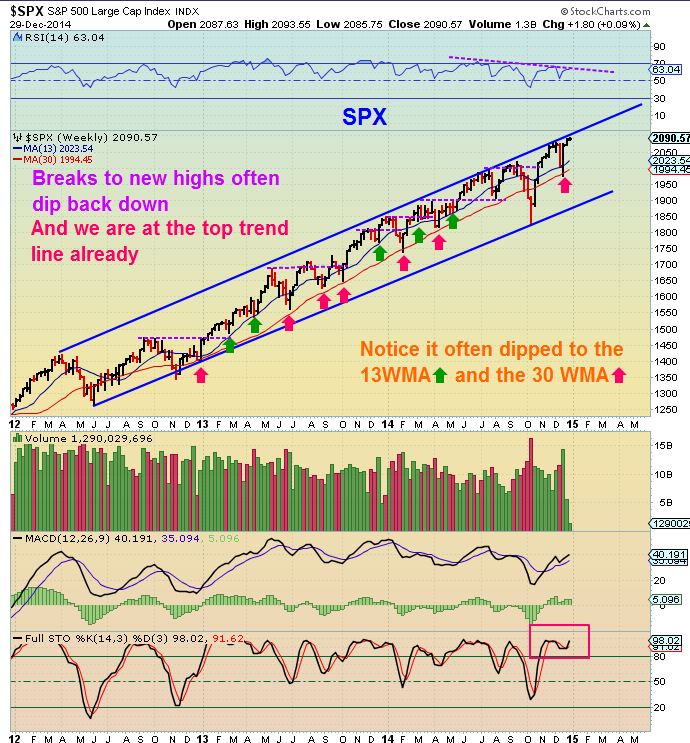
Lets take a look at the SPX
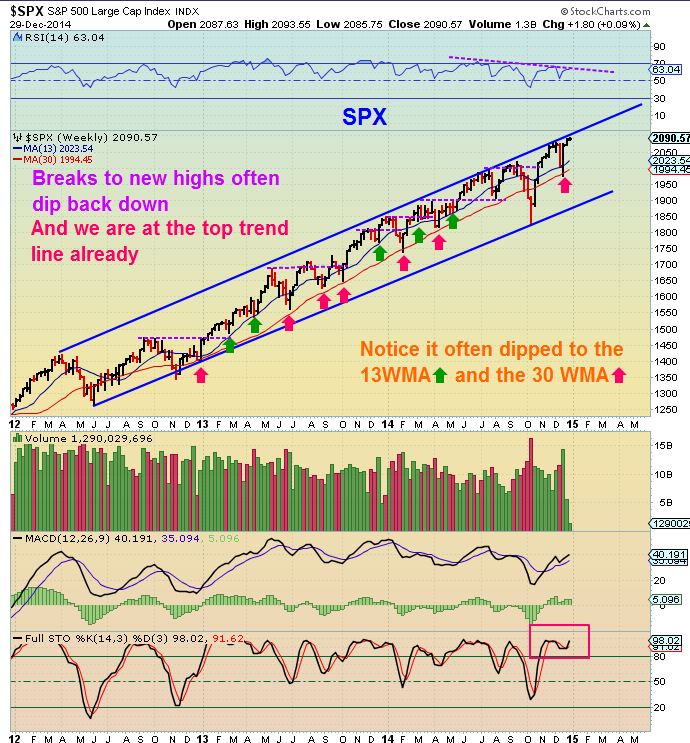
Notice how we hit that upper trend line this summer in JUNE and just rode it higher for a couple of months, will we do that here? ...
Read MoreUsing cycles for 'timing' various sectors of the markets helps us to anticipate when we can expect a possible turn to take place. True, you get a little leeway of maybe plus or minus a few days, but sooner or later, we reach the end of that time period. It seems that we are rapidly approaching the point where it is Do Or Die time. Each day that passes this late in Cycle timing brings us closer to the point where we begin to see clearly how things are going to unfold. As usual, I have about 20+ charts , and at this point I'd like to start with-
GOLD - With the $USD at new highs, GOLD hasn't been hammered down to new lows as one may expect.

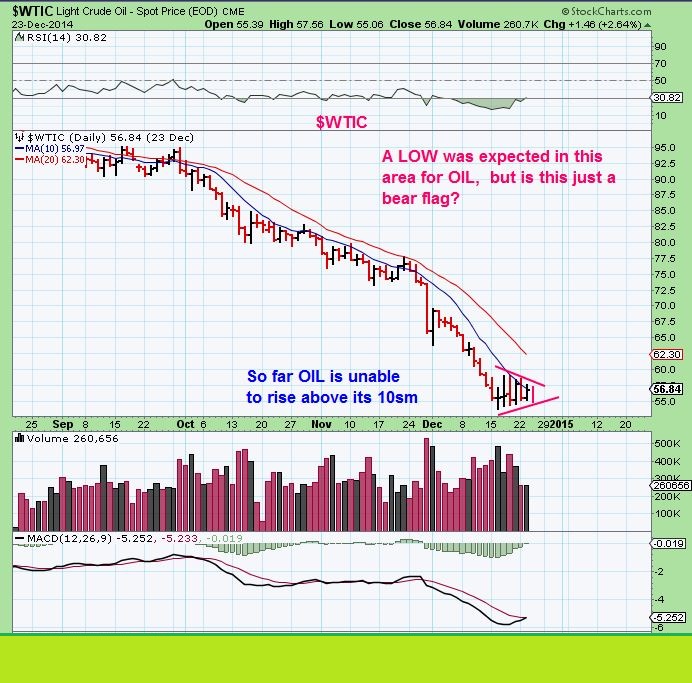
I posted the above chart in my public report, but it still leaves questions. Was that a bear flag that would just break down?...
Read More( This post was written Friday a.m. Dec 26)
Have you ever seen those artists that do 'Chalk Art' along the sidewalks of public streets? They amaze me and at times you just cant believe your eyes. I find myself asking ,
"Is what I am looking at real?" Well lately, many are saying the same thing when they look at the Gold / Silver markets. I have been reporting since Nov 5th & Nov 7th that GOLD was putting in a meaningful low (At least a temporary one). See my Nov 5th report here - http://www.chartfreak.com/afraid-alert/
Looking at the chart of GOLD , you can see that the Nov lows have held and this is with the $USD at new highs!

$SILVER also has shaped up nicely in the past couple of months ...
Read MoreJust a quick post today to show you what I will be watching at the close on this 1/2 day of trading, and also what to look at Friday morning when the markets resume trading. It is noteworthy that OIL sold off again today and OIL is heading back to its lows. Bear Flag?
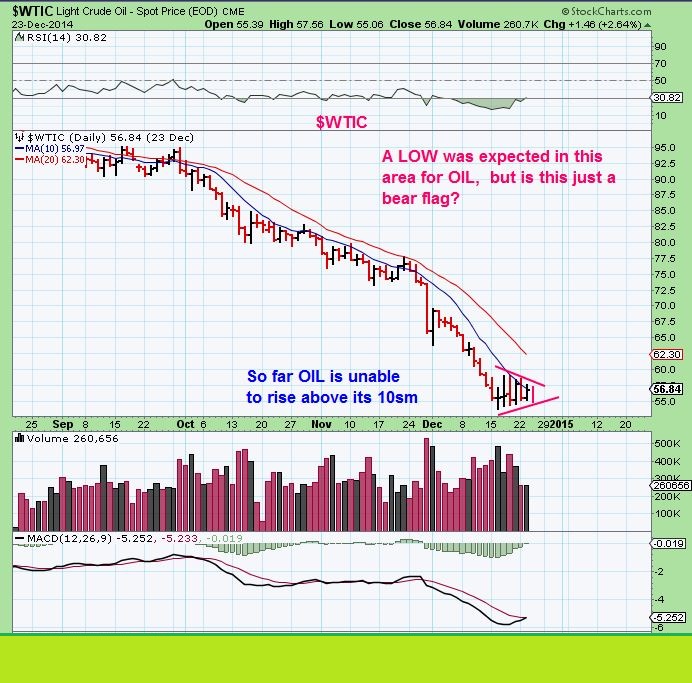
It's certainly possible that OIL undercuts recent lows. It almost did that today, but notice this ...
Read MoreWe had a little bit of selling & volume in The miners today , so instead of a morning report Tuesday, I wanted to post some thoughts tonight. I started getting some questions about things as the day went forward. Nothing wrong with that, it is expected. I had mentioned possibly seeing light volume holiday trading and by noon, we had some selling in Miners. I posted this chart Mid-Day before the selling really started to escalate, to point out some similarities to a prior sell off .
Selling increased from that point on, so what Now?

Lets take a closer look at all things cycles and technical analysis ...
Read MoreI just wanted to post this before the close
Read MoreThis week is usually a lighter volume / traders going on vacation - holiday week of trading. Not much has changed from Fridays report. Things really have to play out further to confirm our expectations or to change them. In other words...not much has changed. We experienced another peoriod of selling similar to what we had in Oct. Many twondered if the Sell off would end the year ugly and then suddenly , right on time ...
QQQ wkly

Its a strong reversal on a weekly basis and take a look at the next chart...
Read MoreToday is triple witching and that can increase volatility and volumes. The first hour tends to see the volatility, and by the last hour the total day volume increases become evident. If you are long the markets , you'll be happy to know that usually there is a bullish bias to Decembers triple witching activity. Nothing is guaranteed, so We'll have to wait and see.
SPX hit that lower target and reversed as seen here

As shown yesterday on the charts that I had drawn up for QQQ, IWC, IWM, RUT and so on, these markets are being bought at targets as that BUY THE DIPS mantra continues
Read MoreWhen I was a kid, I used to really love playing on the swings. Then when I grew up I found that I still love to play with the swings. ‘Market Swings’ ! They can actually be profitable to an investor or trader, because they may afford a low risk entry with potentially more upside than downside risk. The problem is…They can also fall apart. No one wants to swing on a swing thats prone to fall apart. Can we know when a swing is invest-able and less likely to fail? What can help us to identify a proper swing verses a swing that might be prone to breaking down? Since I’ve been trading for years in various sectors, I would say that Experience , Training , and researching with a keen eye have helped here at Chartfreak. Under the “Strategies” tab I have a premium report discussing just that subject in Gold / Silver & Miners. I will share a little of the thinking there…but the details obviously need to be reserved for paying members.
GOLD WEEKLY (Today , Golds daily chart looks lame. The weekly chart could look bullish or bearish as of yesterday, but it swings lower)

The $USD was a rocket yesterday, Swinging up over one Dollar! Todays follow through seems to be hindering GOLD & SILVERS progress.

Then why are GDX & GDXJ green? WHAT ARE THESE SWINGS? Is it just an oversold bounce, about to tank with the metals? OR Are Miners leading GOLD here?

Even individual Miners ( like MVG) have interesting Swings taking place. MVG , a Silver miner , was swinging up higher yesterday as the $USD was up over a buck. Thats odd.

Today it reached resistance, and Gold & Silver began to sell downward- is it DONE? A broken Swing ready to fall apart with the Metals soon? Or could it possibly pullback to gain some strength & then break out higher?

I do think that I have a good idea of whats going on in Metals and Miners right now . I do feel that things are lining up for a decent move in one direction or the other, and that it could be profitable to take positions soon. Its in today’s report under the strategies tab for paying members. To get my thoughts on the matter and see things the way that I do, you can sign up for a 1 month subscription under the ‘strategies tab’ and see my analysis on Metals / Miners / SPX / IWM / in todays report and also I had an Energy report Tuesday referring to XLE & ENERGY being pssibly at the lows Monday . I personally believe that you will be able to more than make your $37.95 back on 1 good trade, if things play out the way I feel that they will.
Even if you cant sign up, Thanks for stopping by and I appreciate your being here and reading along. I will post publicly from time to time , so check in frequently under the ‘blog’ tab / strategies tab for premium content. Also you can Sign up for our free email alert service & be directly notified whenever I post. Thanks again for stopping by.
~Alex
Scroll to top